Defense Mode or Panic Mode?

RESPOND PROACTIVELY TO REDUCE THE COST OF A BREACH
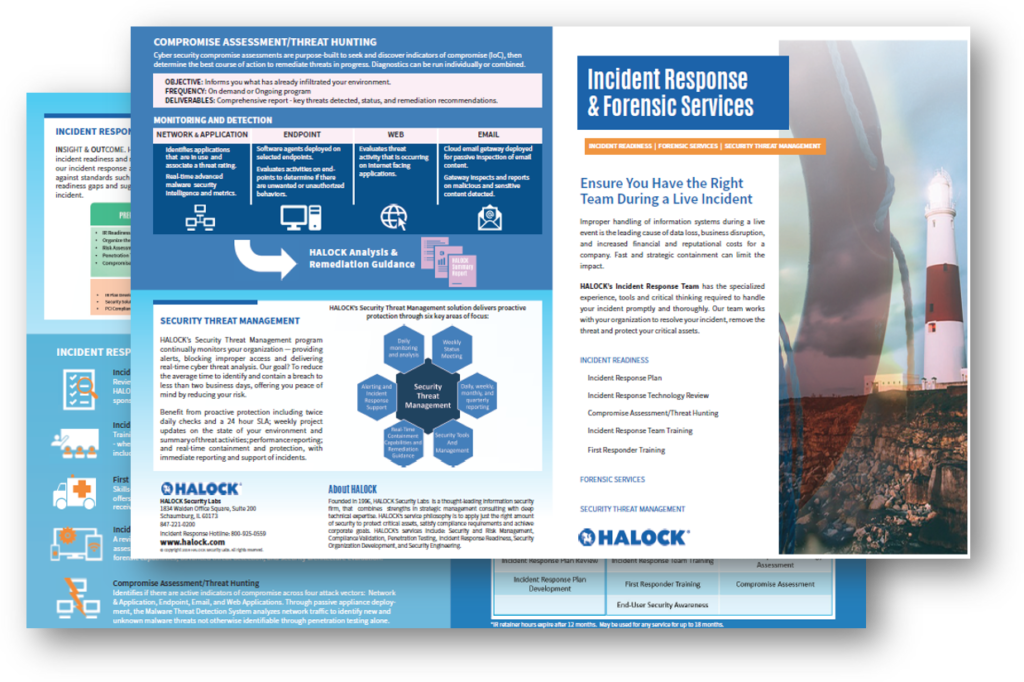
Your attack response could potentially prevent the spread of harmful malware, further data loss, and increased legal liability. We can help minimize the impact on your business.
“Thank you so much for your swift action and remarkable level of expertise.”
– Nationally-Ranked Hospital
RESPOND COMPREHENSIVELY TO MITIGATE RISK
Get the full perspective of potential attacks and how to address them. We can prepare your team on what to do, who to contact, and what to communicate should you get attacked.
- IR Readiness Assessment
- Incident Response Requirements Review
- Point-by-Point Incident Response Planning (IRP)
- First Responder Training and IR Team Training or Tabletop Exercises
- Critical Checklists
- Compromise Assessment
- Threat Hunting (MDR)
RESPOND SMARTLY TO PROTECT CUSTOMERS AND BRAND
Let us help assess your current incident response readiness and get you prepared before a security event occurs. We are here to help you navigate the complexities of a security incident and provide peace of mind that you have a reasonable and appropriate plan.
“The response time was great. HALOCK was able to help put us on the road to recovery as quickly as possible.”
– Electrical Equipment Supplier
HALOCK is a trusted risk management and cybersecurity company headquartered in Schaumburg, IL, in the Chicago area and advises clients on reasonable security, risk assessments, penetration testing services, security management, architecture reviews, and compliance throughout the US.
As principal authors of CIS Risk Assessment Method (RAM) and board members of The Duty of Care Risk Analysis (DoCRA) Council, HALOCK offers unique insight to help organizations define their acceptable level of risk and establish “duty of care” for cybersecurity. Through this risk assessment method, businesses can evaluate cyber risk that is clear to legal authorities, regulators, executives, and security practitioners.
HALOCK Breach Bulletins
Read HALOCK overviews and analyses about recent data breaches to understand what are common threats and attacks may impact your organization – featuring description, indicators of compromise (IoC), containment, and prevention.
Learn how Duty of Care Risk Analysis (DoCRA) can help you achieve reasonable security:
What is Duty of Care Risk Analysis (DoCRA) for Cybersecurity?
What is Duty of Care Risk Analysis (DoCRA) for General Counsel?
What is Duty of Care Risk Analysis (DoCRA) for Regulators?
What is Duty of Care Risk Analysis (DoCRA) for Auditors?
What is Duty of Care Risk Analysis (DoCRA) for Executives?
What is Duty of Care Risk Analysis (DoCRA) for Risk Managers?
To successfully approach managing risk in the age of AI, organizations using AI should incorporate reasonable security into their risk strategy.
Establish reasonable security through duty of care.
With HALOCK, organizations can establish a legally defensible security and risk program through Duty of Care Risk Analysis (DoCRA). This balanced approach provides a methodology to achieve reasonable security as the regulations require.
