Reference Materials
Case Studies
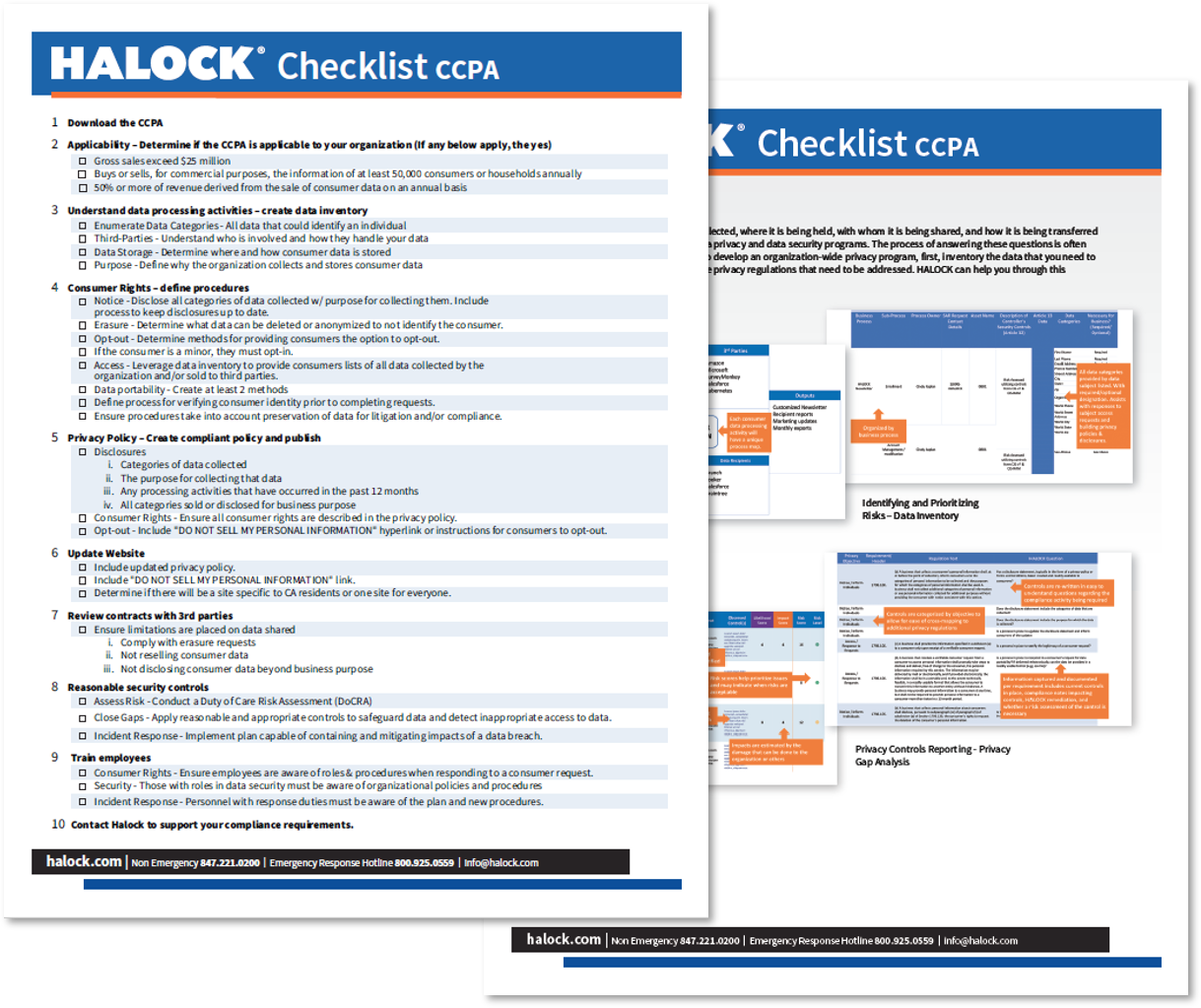
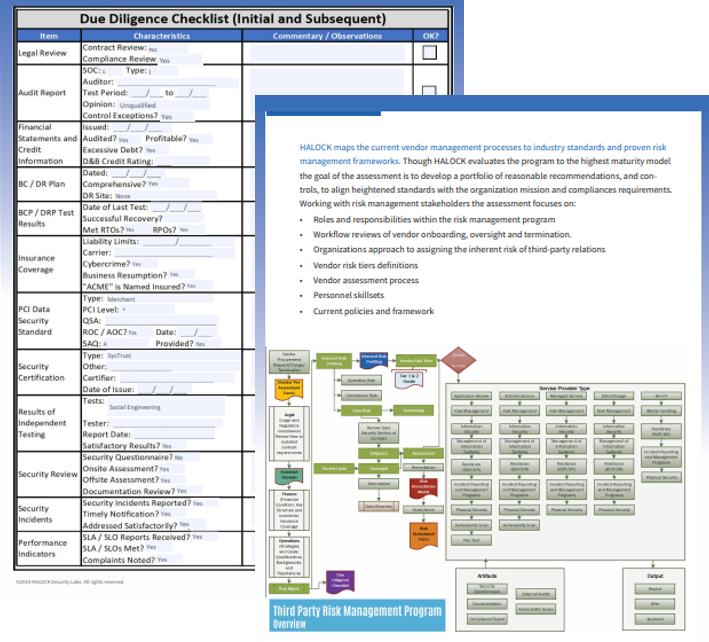
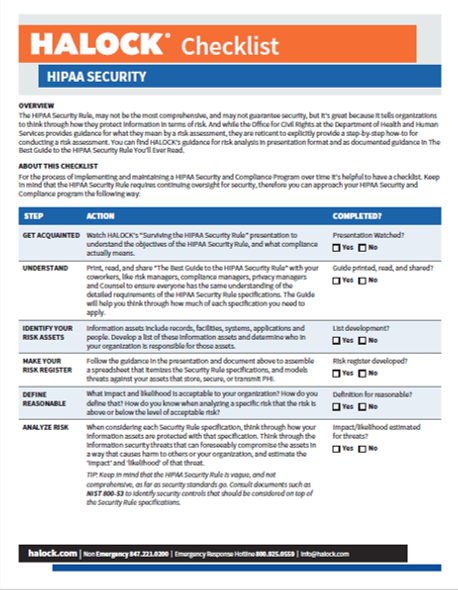
Checklists
Guides/Workbooks
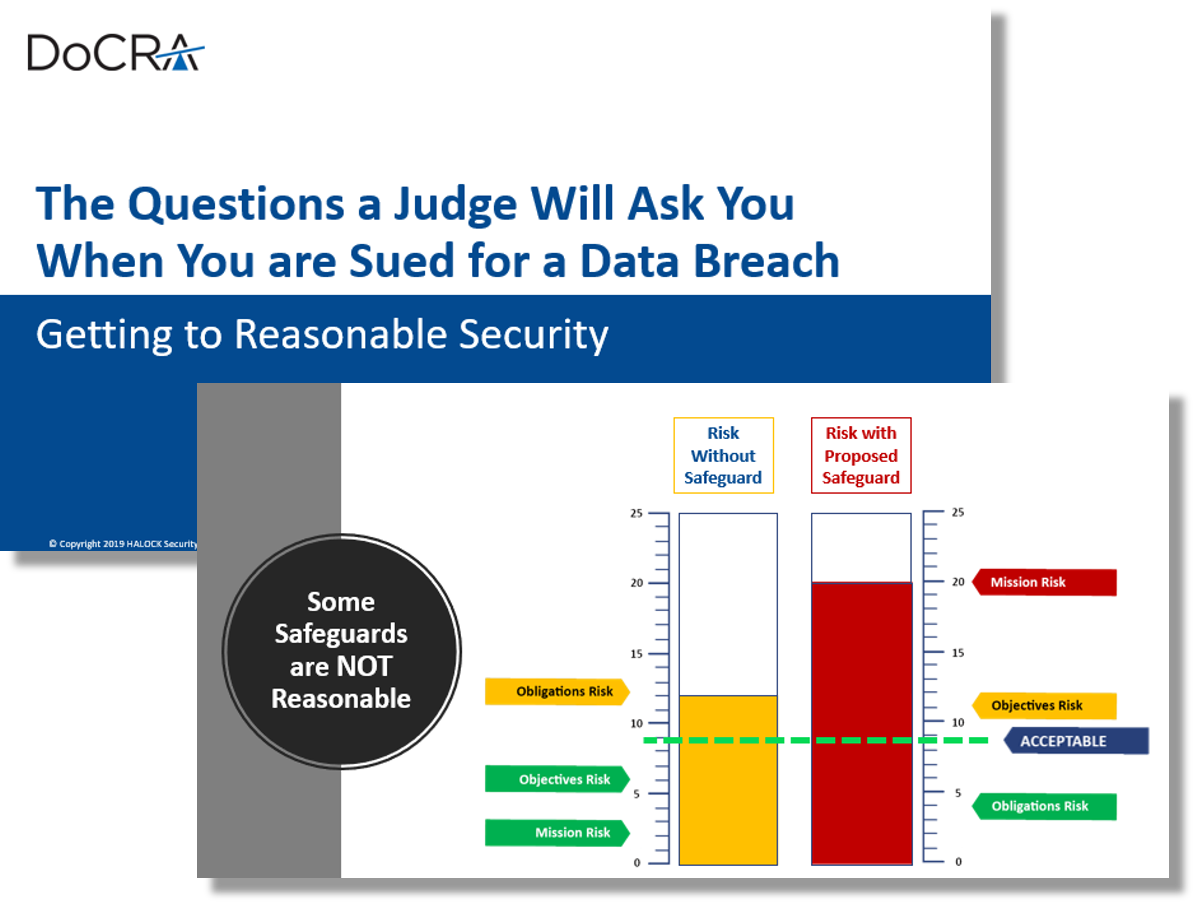
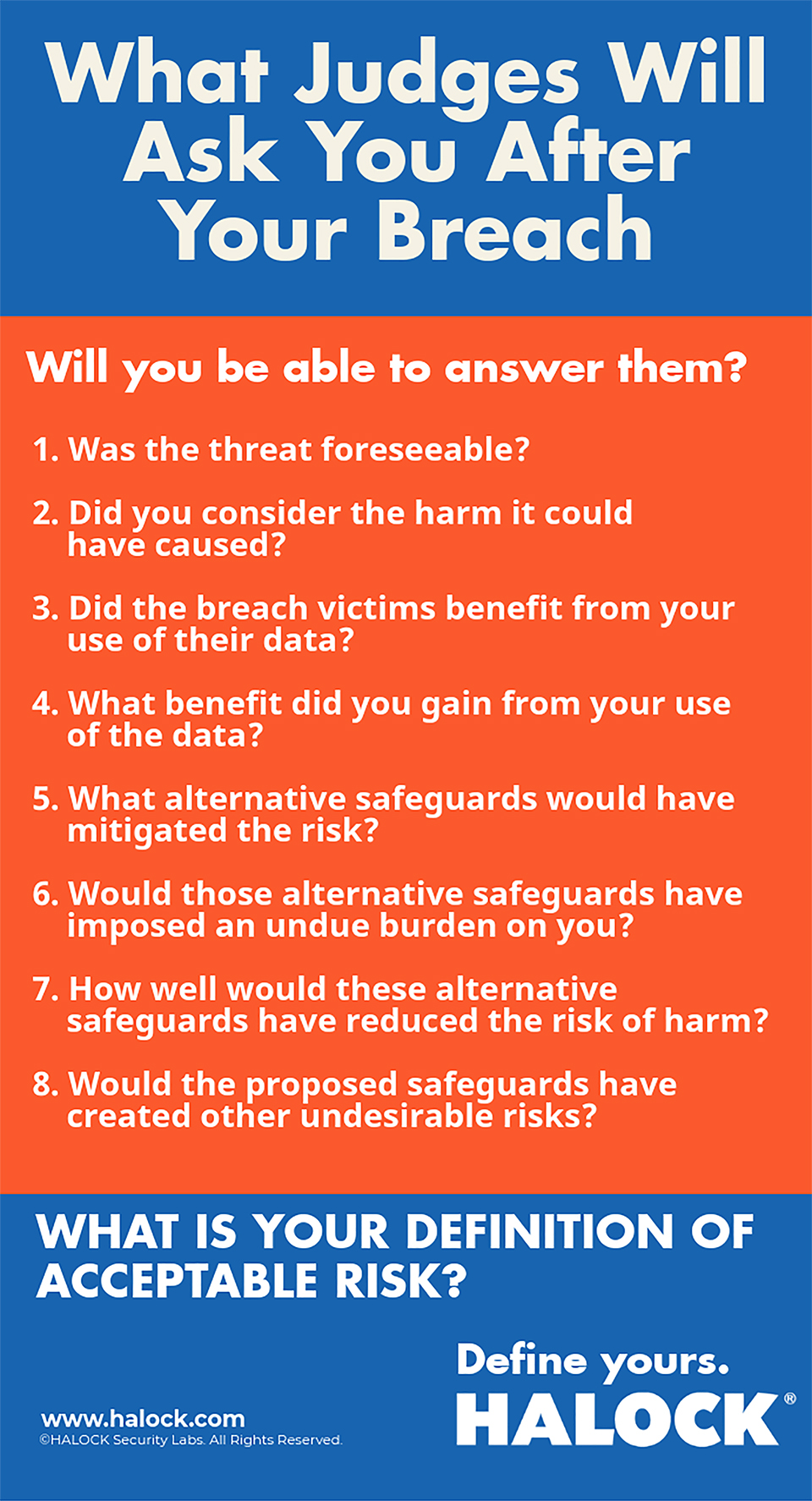
(ISC)2 Security Congress | The Questions a Judge Will Ask You When You are Sued for a Data Breach | Getting to Reasonable Security
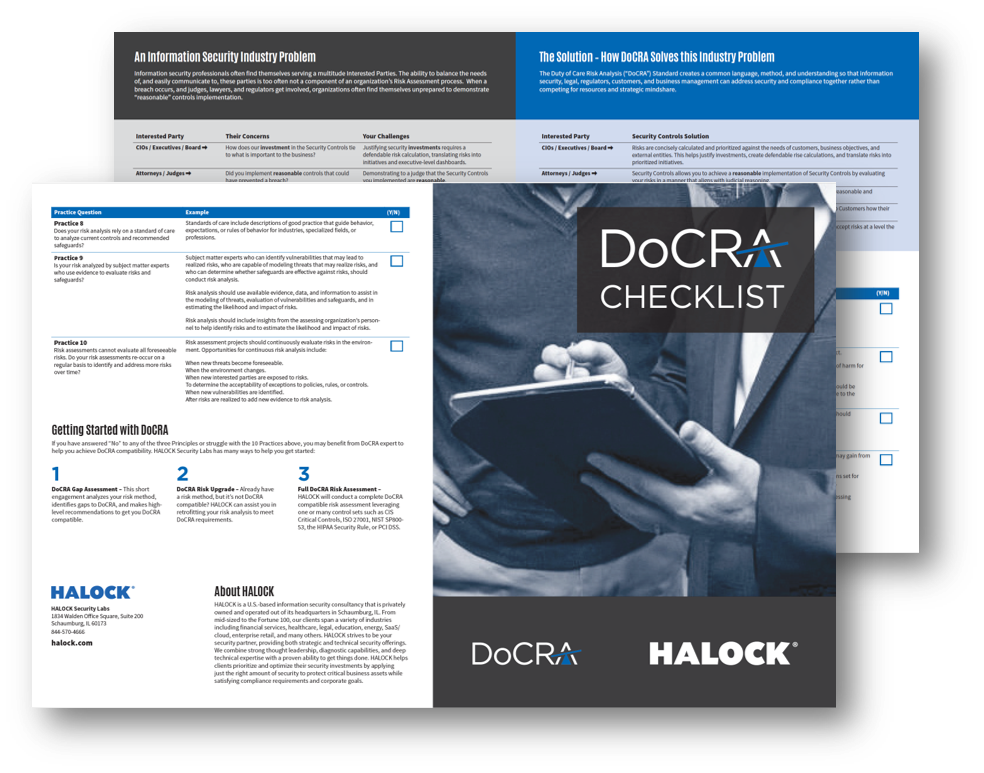
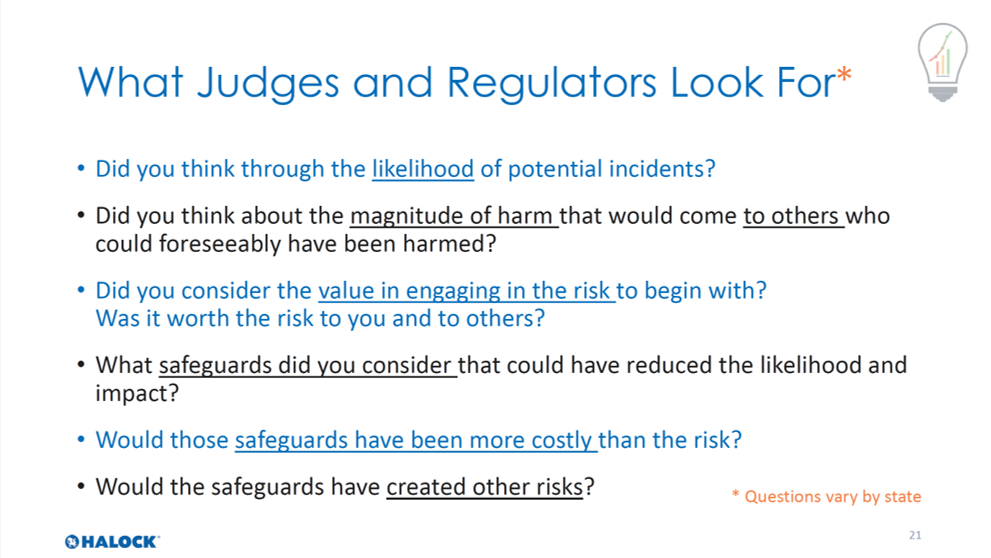
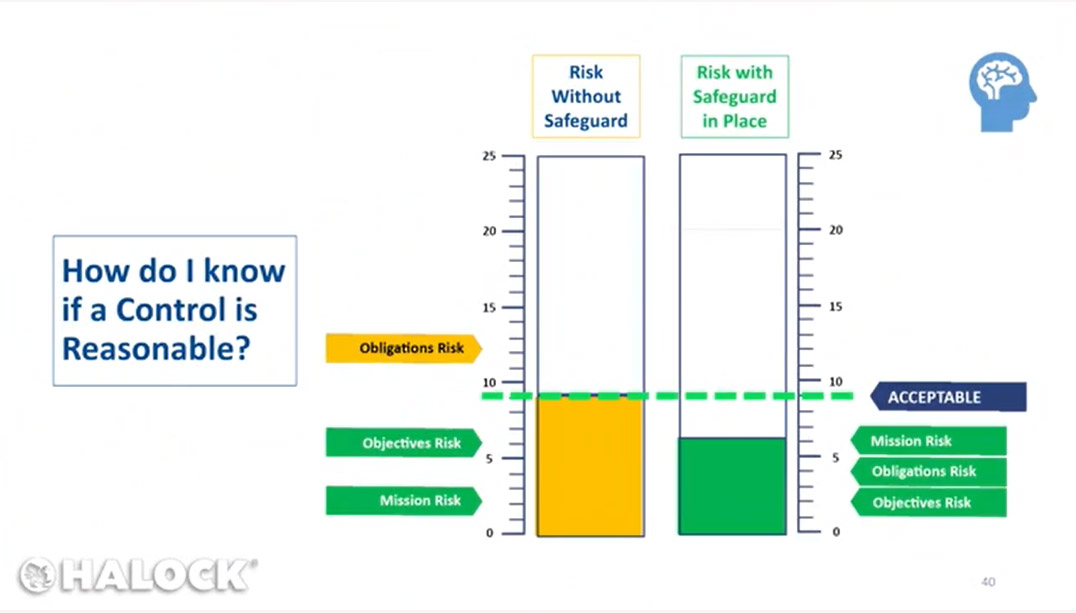
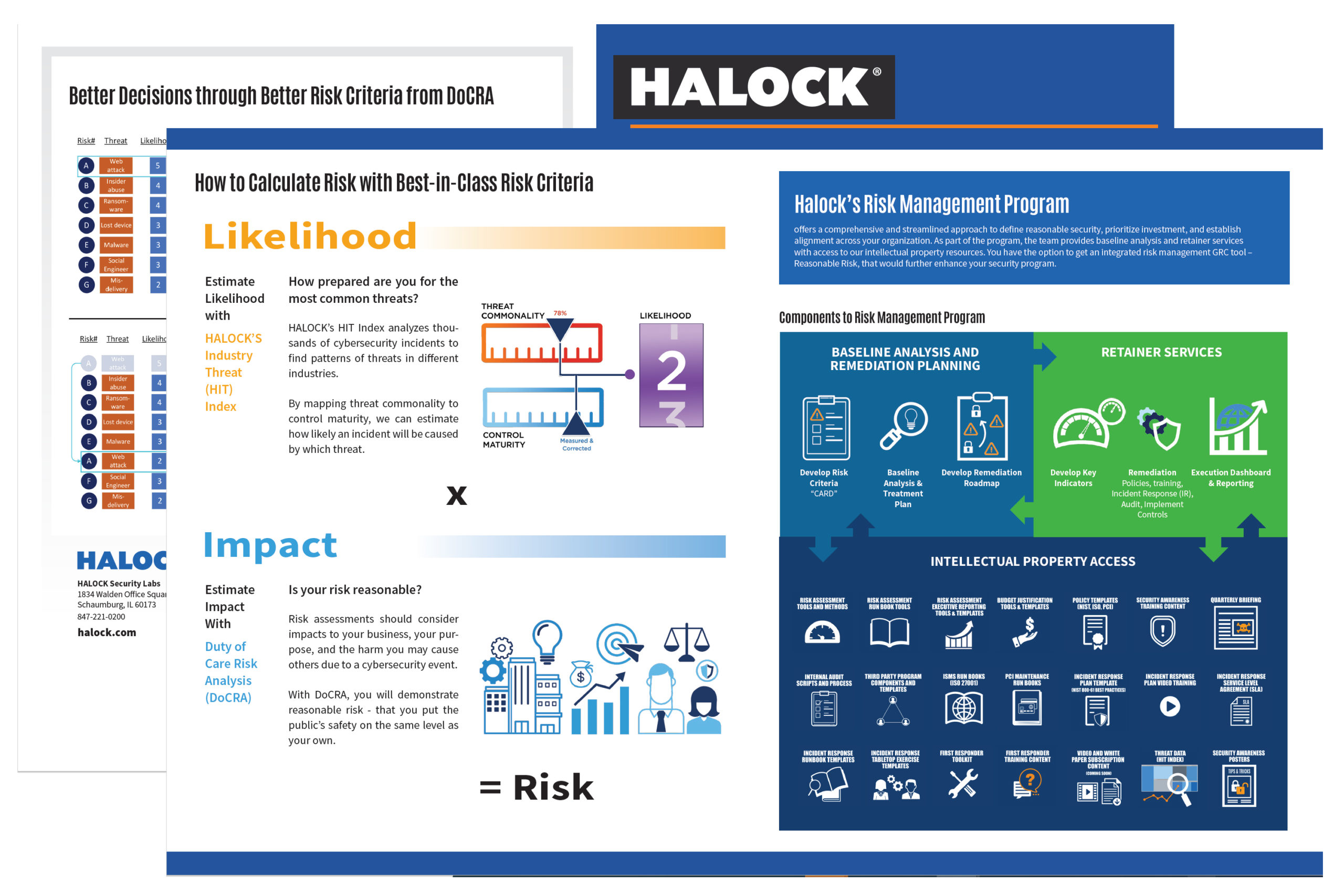
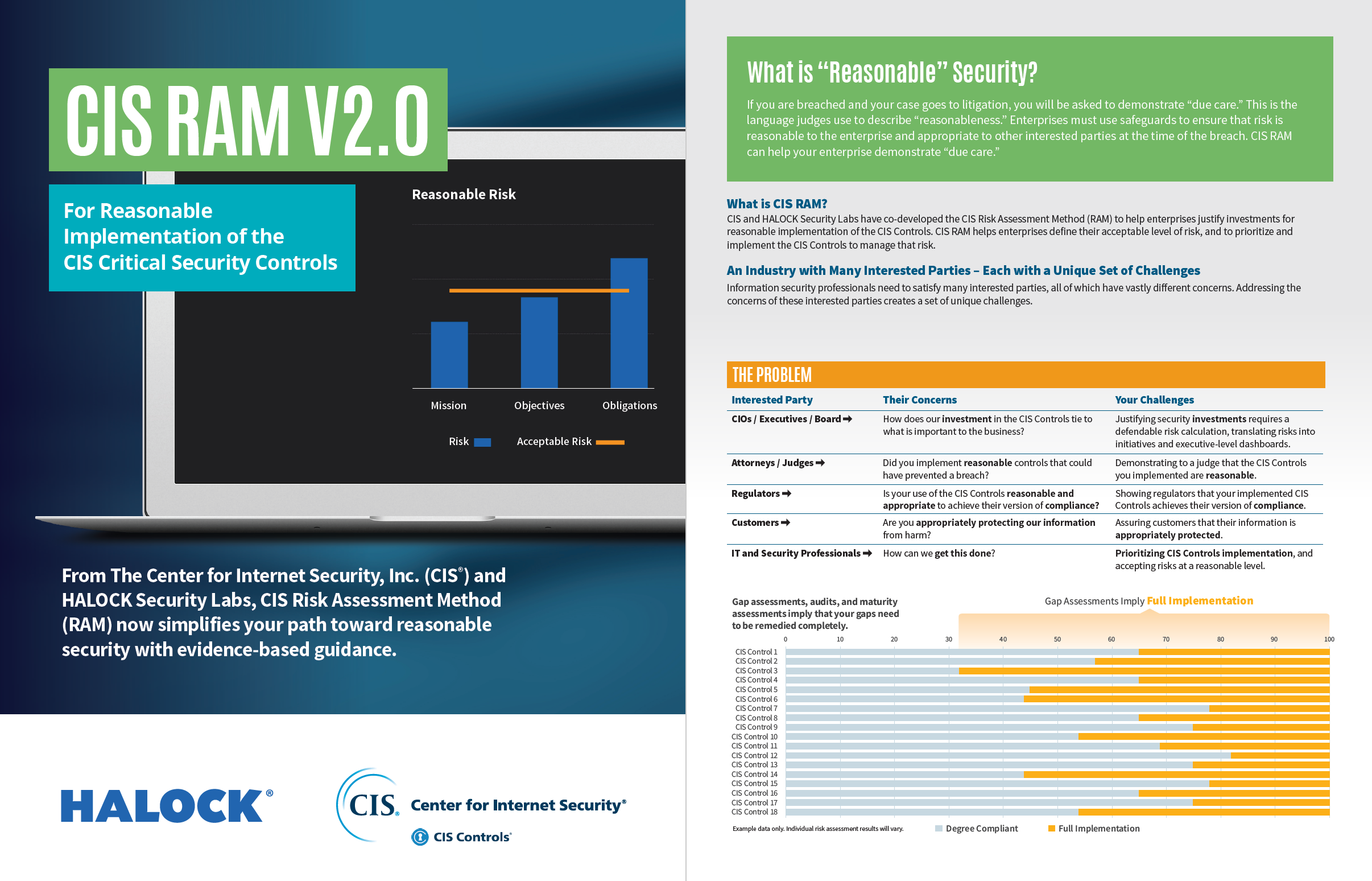
What is reasonable security? This presentation references case law, regulatory oversight and the Center for Internet Security Risk Assessment Method (CIS RAM). CIS RAM is based on the Duty of Care Risk Analysis standard (DoCRA.org) and is recognized by attorneys, regulators and interested parties for its ability to demonstrate reasonable implementation of controls.
HCCA Webinar: Duty of Care Risk Analysis
Duty of Care Risk Analysis How to define “reasonable” security controls that makes sense to business, judges, and regulators. Design and run a risk assessment that is meaningful to technicians, business, and authorities. Learn from case studies involving regulatory oversight, law suits that happened, and law suits that never happened
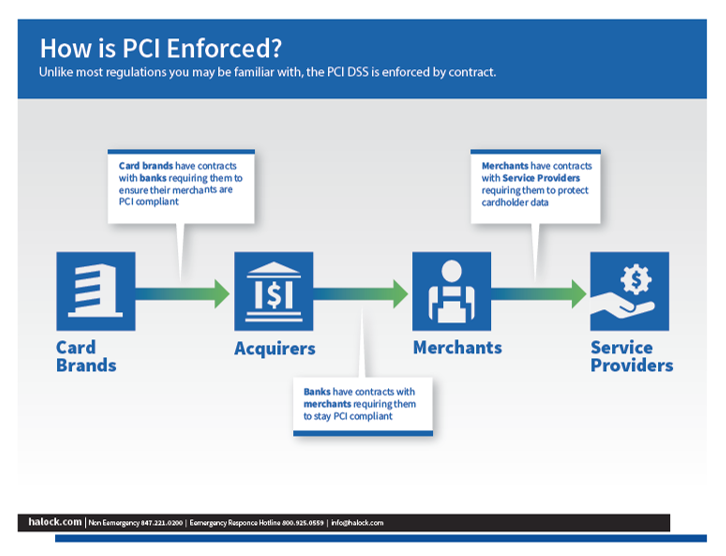
The Guide to PCI DSS 3.2
The PCI Security Standards Council (PCI SSC) in PCI DSS v3.2 is requiring that all versions of SSL and TSL version 1.0 must be disabled. In order to be PCI DSS compliant you must be utilizing TLS 1.1 at a minimum, (although TLS 1.2 is highly recommended). This mandate was originally slated for implementation by 2016 but due to the burdensome impact to organizations, the PCI SSC extended the timeline to June 30, 2018. The PCI DSS applies to all organizations receiving credit card payments for goods and/or services (merchants) and any third party service providers for PCI DSS merchants. This guide helps users through the new requirements.
Industry Insights
InfraGard SuperCon: Getting to Reasonable - What regulators and judges want to see from every organization
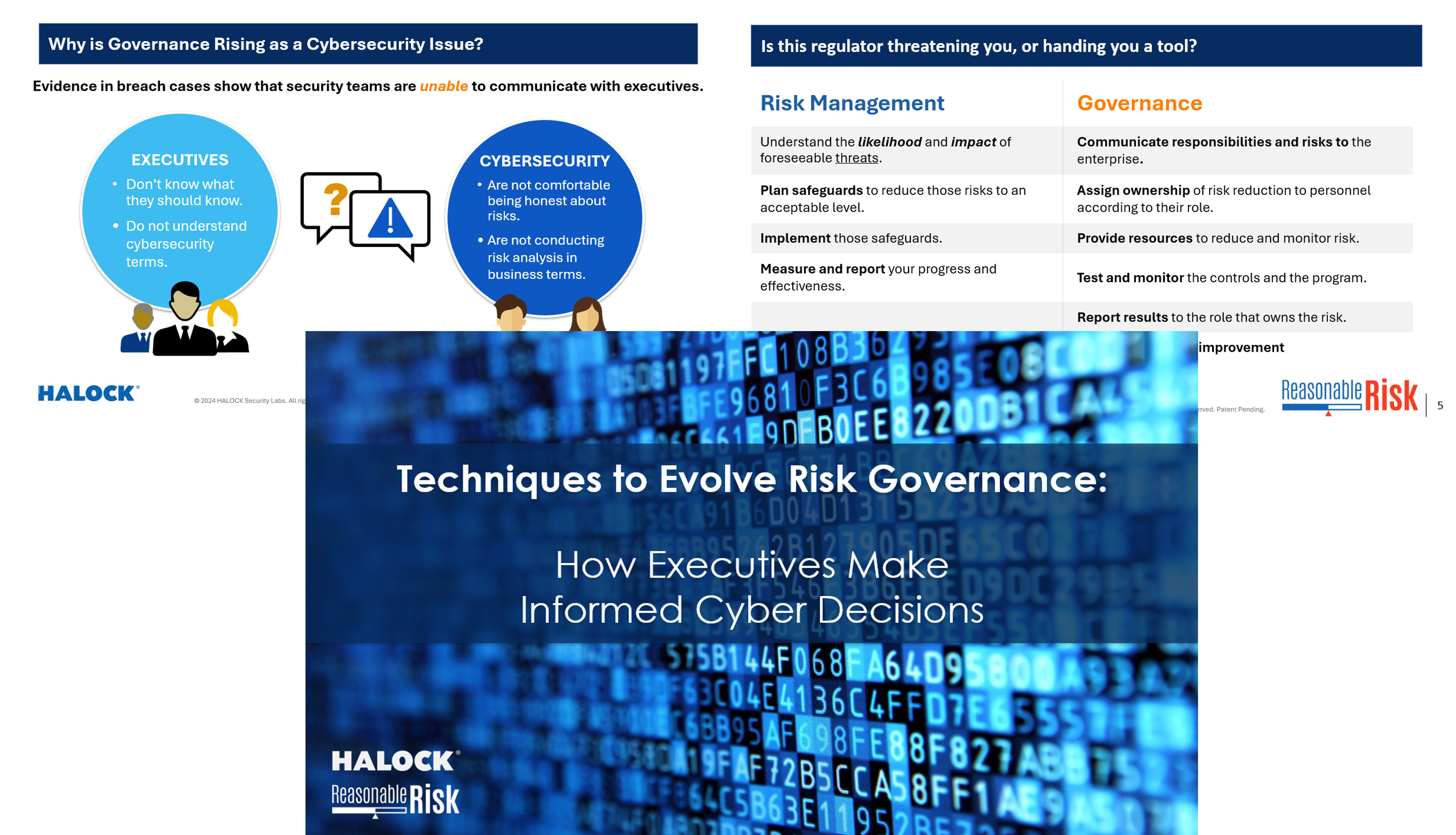
Are you prepared to show your security program was reasonable and appropriate? Until recently the definition of “Reasonable Controls” and “Acceptable Risk” has been vague and left up to the security and risk practitioners in each organization. The regulator, judge, or other interested party wants to understand; “why you did not have that particular control or configuration in place?” Having the calculus to demonstrate your understanding of the foreseeable harm that could come to you and others and how you were planning on addressing the reduction of impact or probability is what the interested parties want to see.
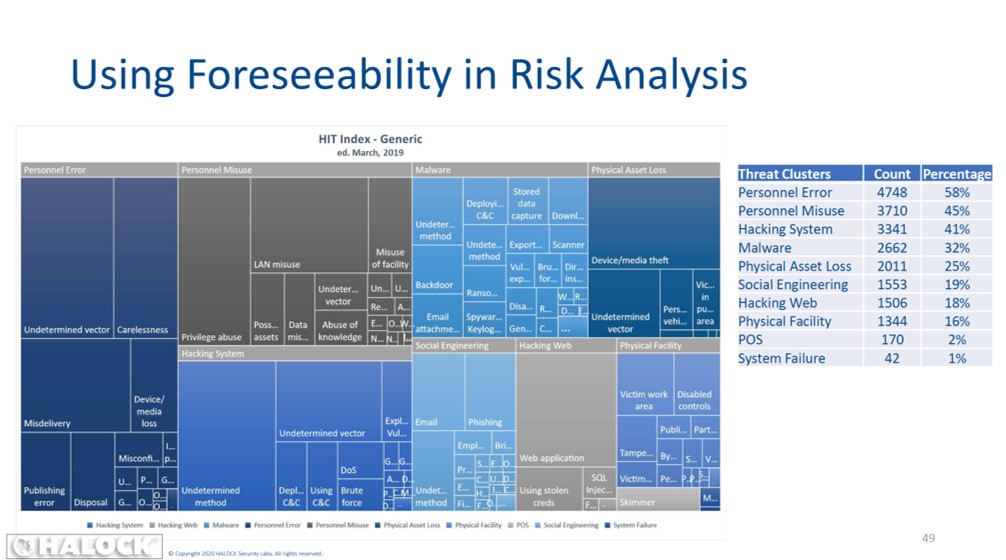
Cyber Security Summit Threat Forecasting: Using Open Source Data to Foresee Your Next Breach
We forecast cybersecurity events not to predict the future, but to change it. Regulators and litigators all hold us accountable for knowing foreseeable threats so we can avoid them. But what is foreseeable? And how do we evaluate risks knowing what is foreseeable? This session will demonstrate how open source information can help you prioritize your cybersecurity efforts, and demonstrate that you were being reasonable even if a breach does occur.
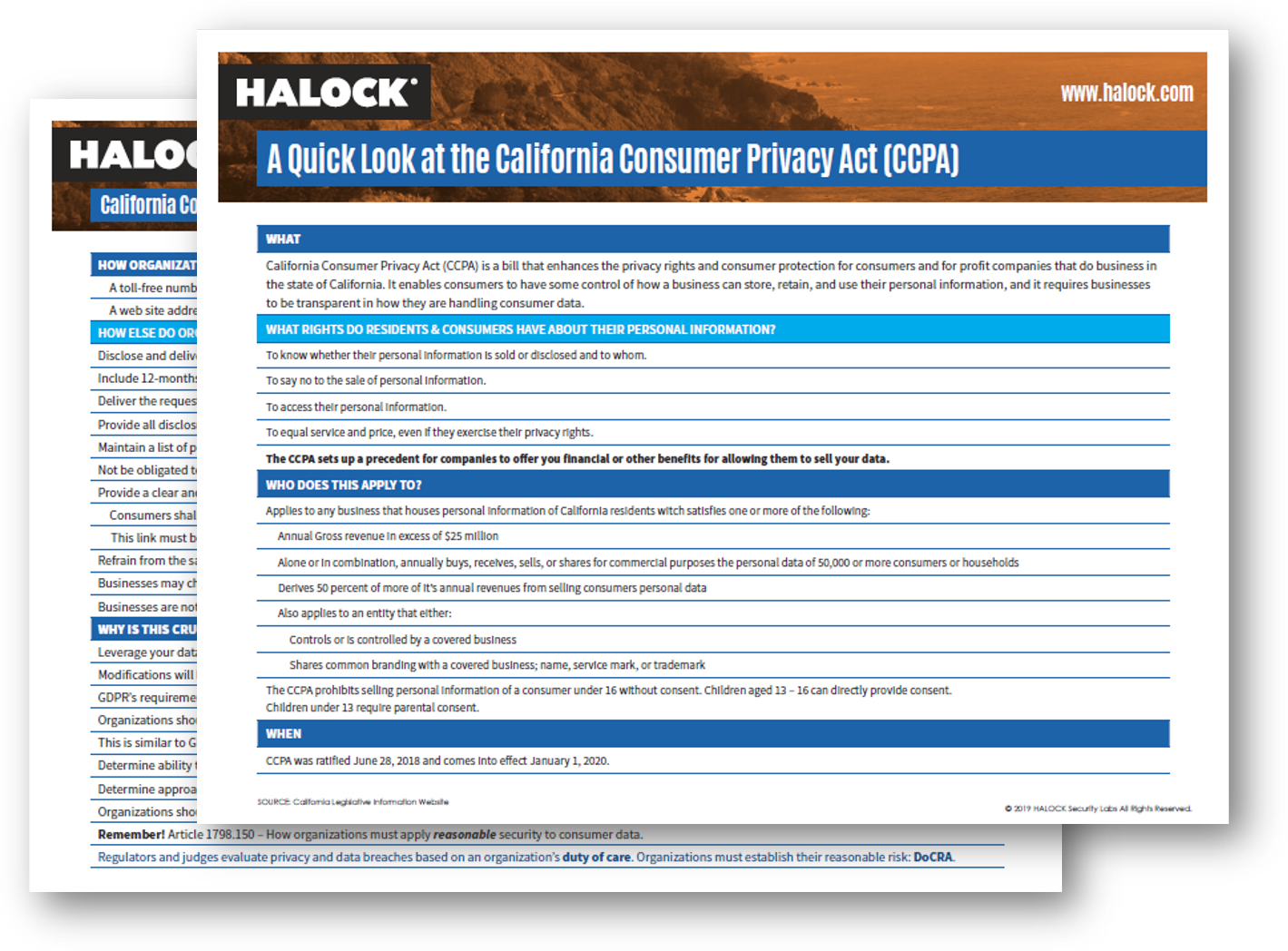
Cyber Security Summit Presentation: CMMC and CCPA. Using Duty of Care Risk to Comply With New Challenges
CMMC and CCPA are very different requirements that push security organizations in new directions. CMMC is specific and for the DoD supply chain. CCPA is generic and for any organization with certain personal information. But both specific and generic security requirements are difficult to comply with. During this session we will show you how Duty of Care Risk Analysis can help you move from either generic or specific requirements to “reasonable” security controls that regulators will understand.
(ISC)2 Security Congress | The Questions a Judge Will Ask You When You are Sued for a Data Breach | Getting to Reasonable Security
What is reasonable security? This presentation references case law, regulatory oversight and the Center for Internet Security Risk Assessment Method (CIS RAM). CIS RAM is based on the Duty of Care Risk Analysis standard (DoCRA.org) and is recognized by attorneys, regulators and interested parties for its ability to demonstrate reasonable implementation of controls.
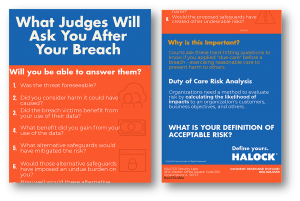
Reasonable Security The Questions a Judge Will Ask You After a Data Breach
This presentation helps establish reasonable security by reviewing judicial balancing tests, how they relate to regulatory definitions of “reasonable” risk, and how to conduct risk assessments that prepare you to answer the tough questions before you need to be asked.
HCCA Webinar: Duty of Care Risk Analysis
Duty of Care Risk Analysis How to define “reasonable” security controls that makes sense to business, judges, and regulators. Design and run a risk assessment that is meaningful to technicians, business, and authorities. Learn from case studies involving regulatory oversight, law suits that happened, and law suits that never happened
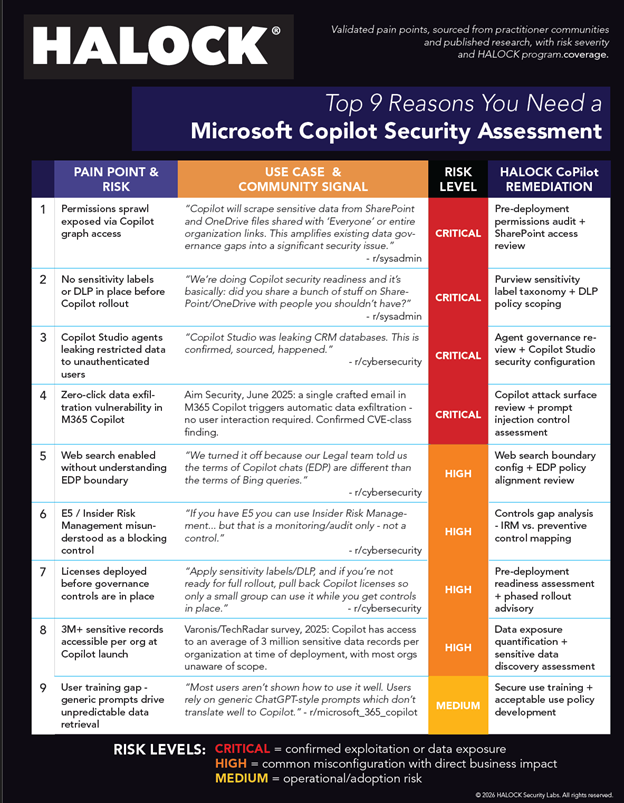
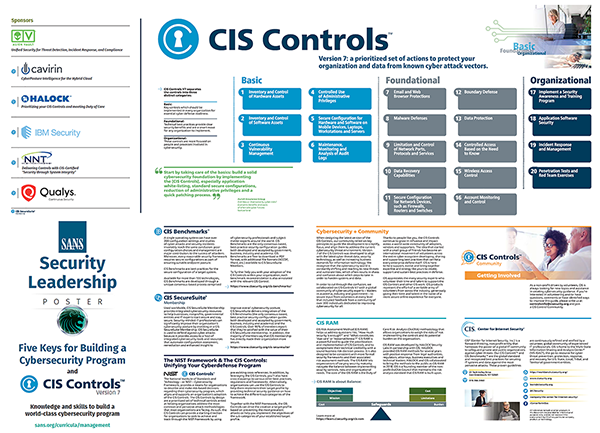
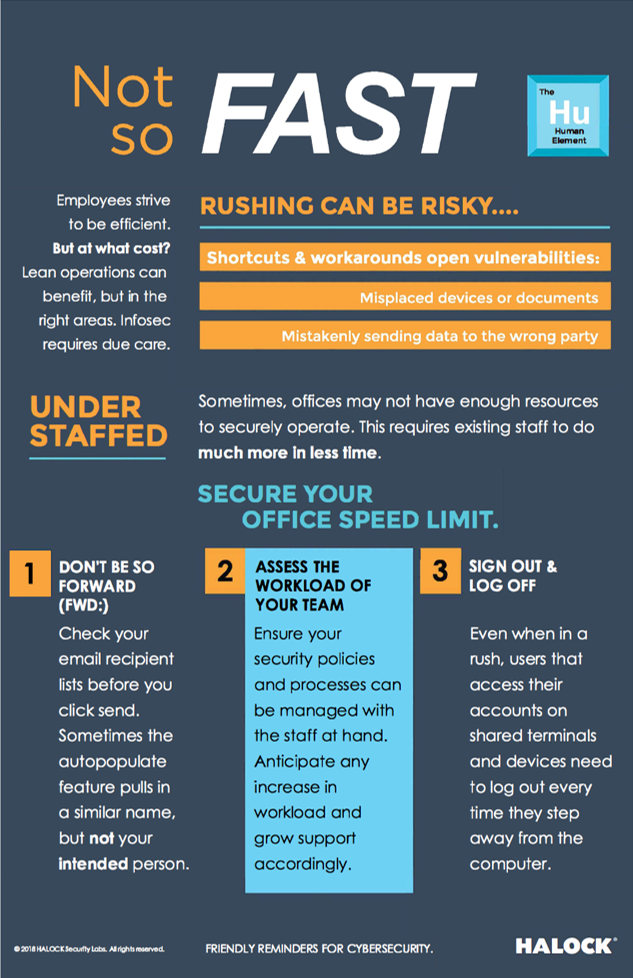
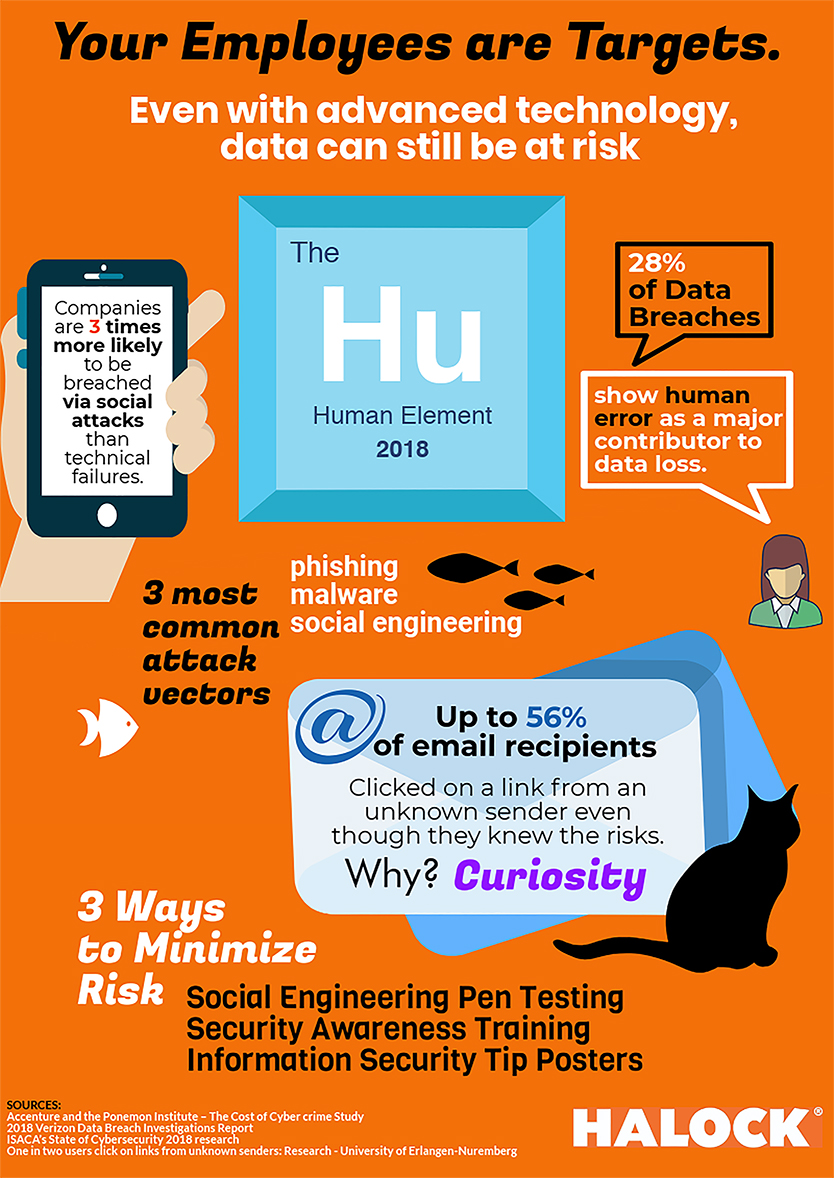
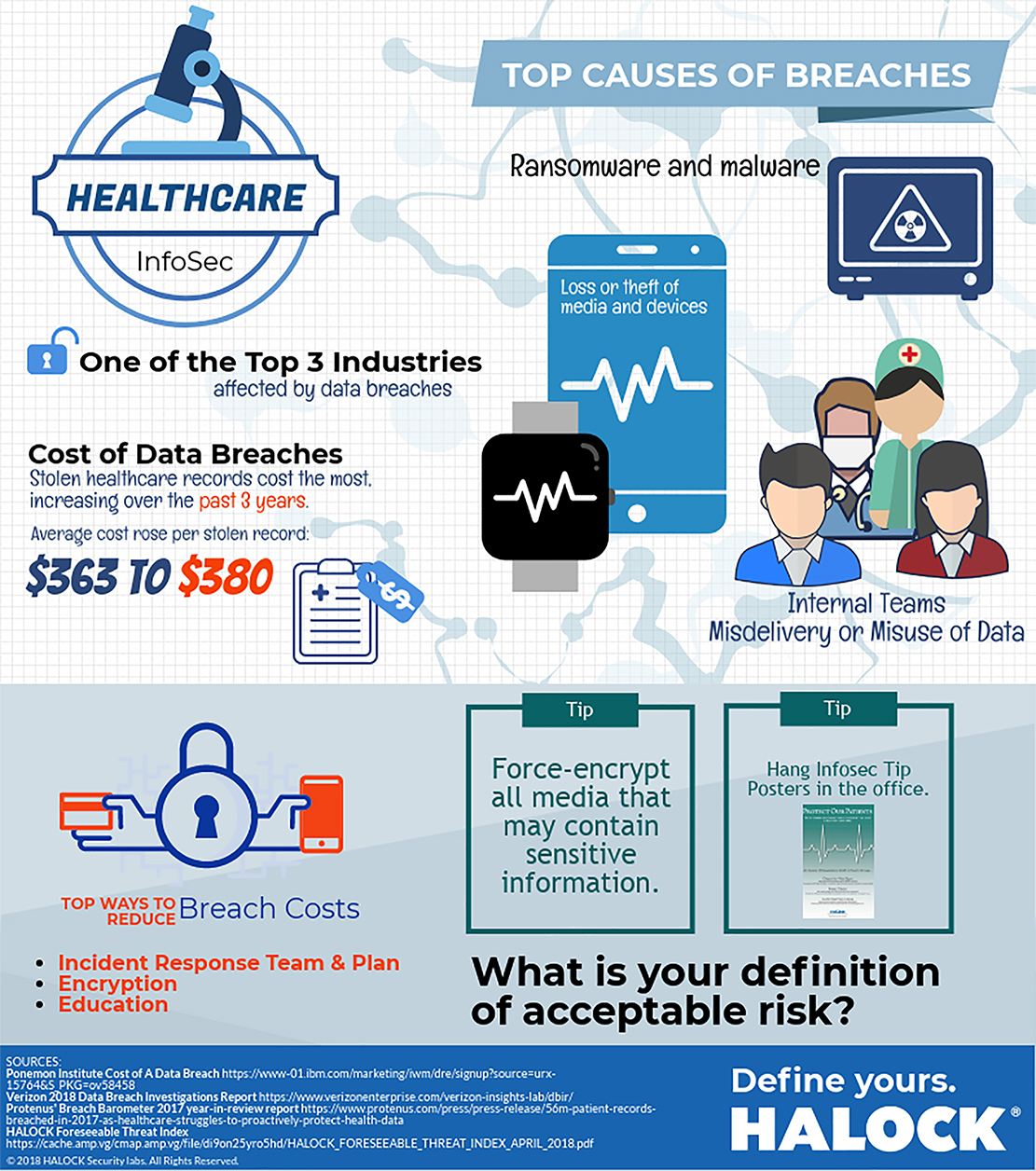
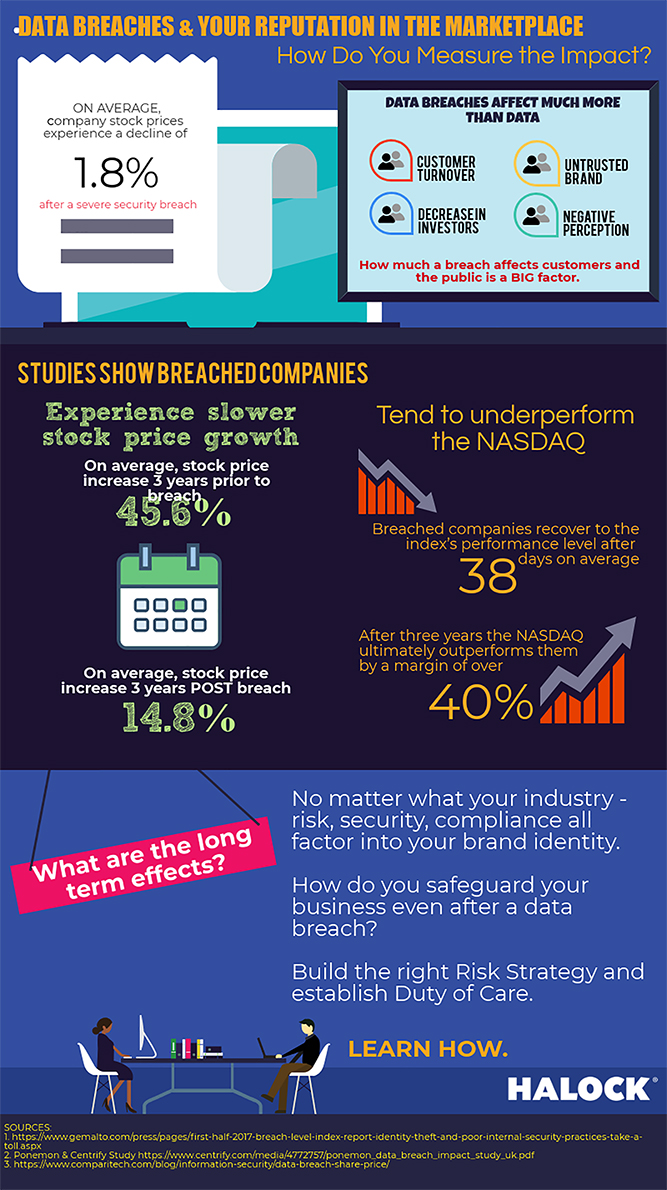
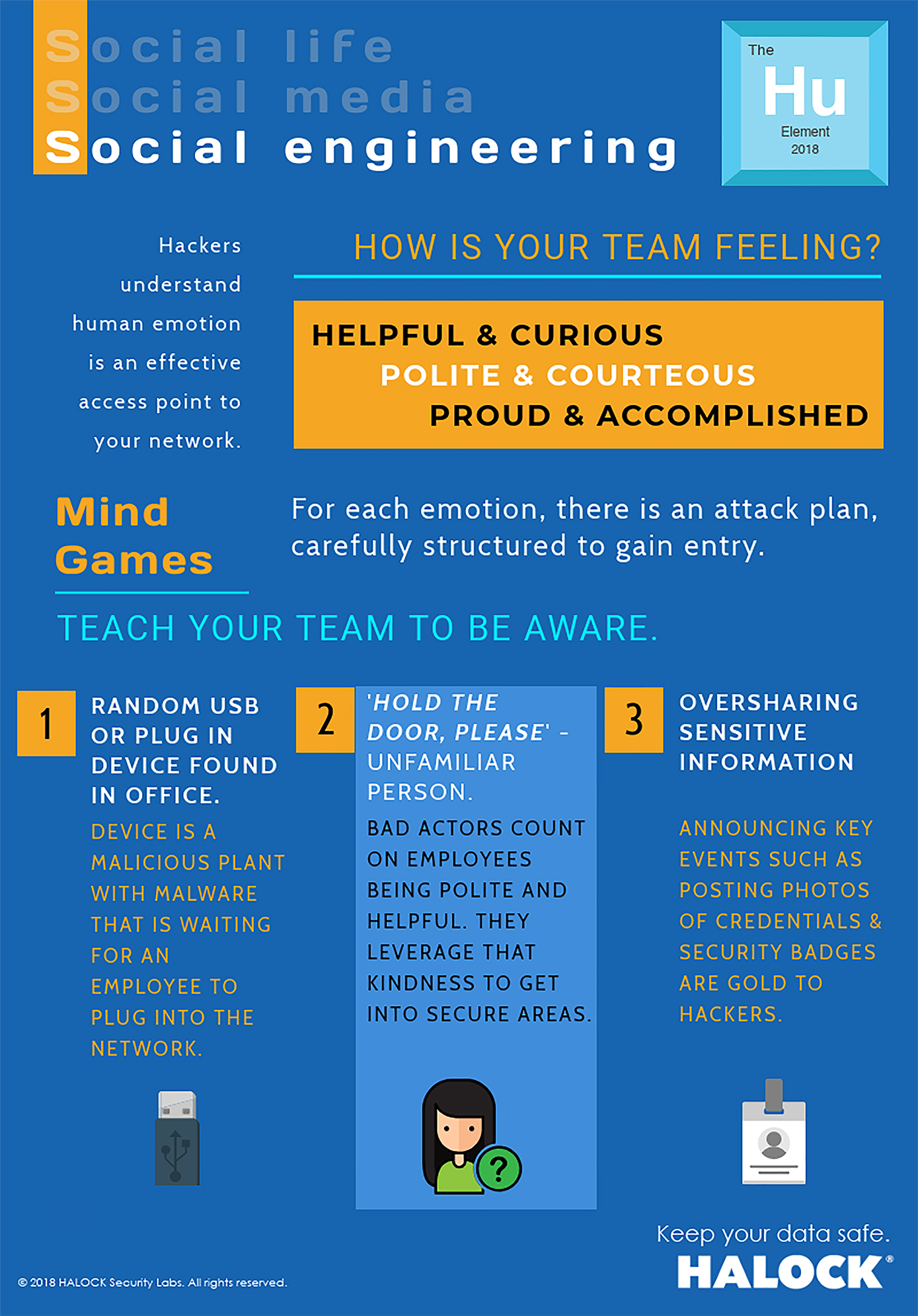
Infographics
A visual overview of cyber security trends, news, industry in infographics.
Solutions
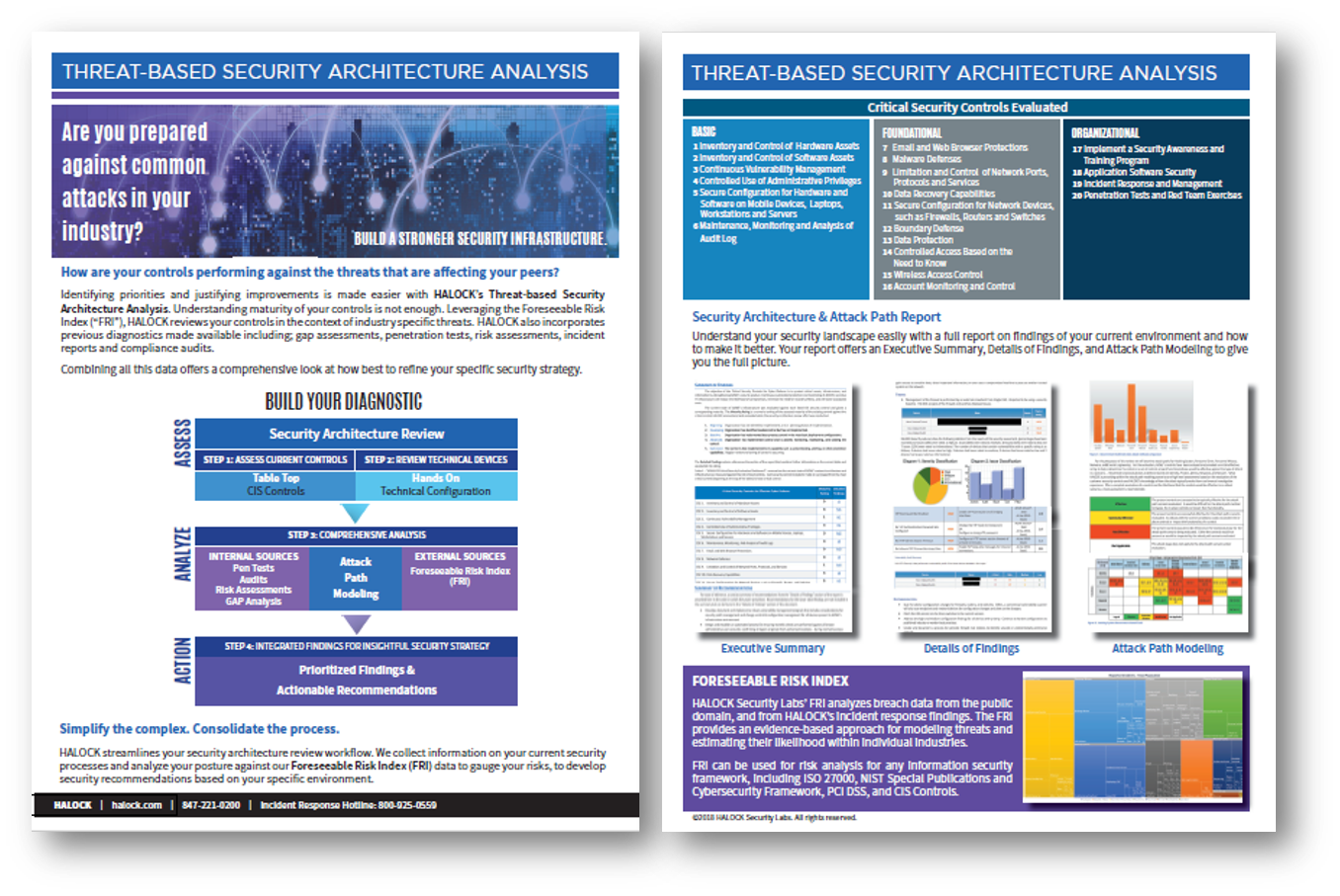
PCI DSS Compliance Information Security
The Payment Card Industry Data Security Standard (PCI DSS) specifies technical and operational requirements for all organizations that store, process or transmit credit card data. If you handle credit card data, then PCI DSS applies to you - achieve PCI Compliance with HALOCK and mitigate your risks.
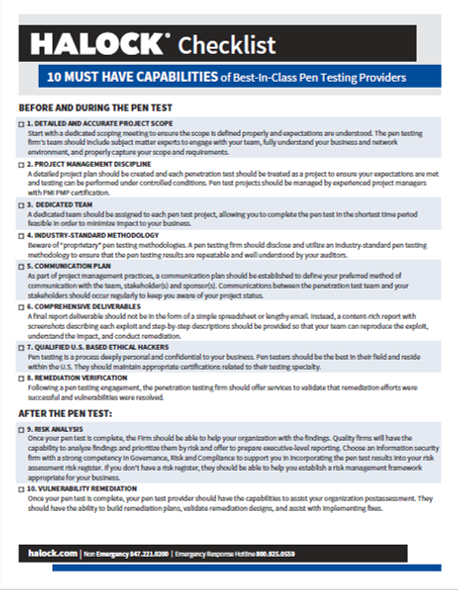
Social Engineering Penetration Test Cyber Security Risk
Remote social engineering penetration testing validates the effectiveness of user security awareness, incident response, and network security controls. Ensuring your teams understand your processes help manage your risk. Conduct a social engineering pen test regularly.
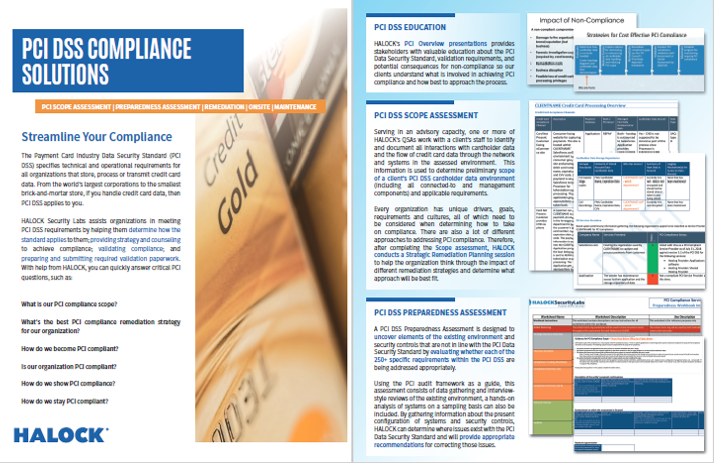
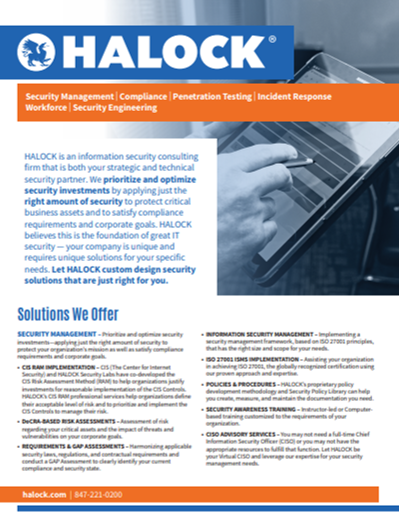
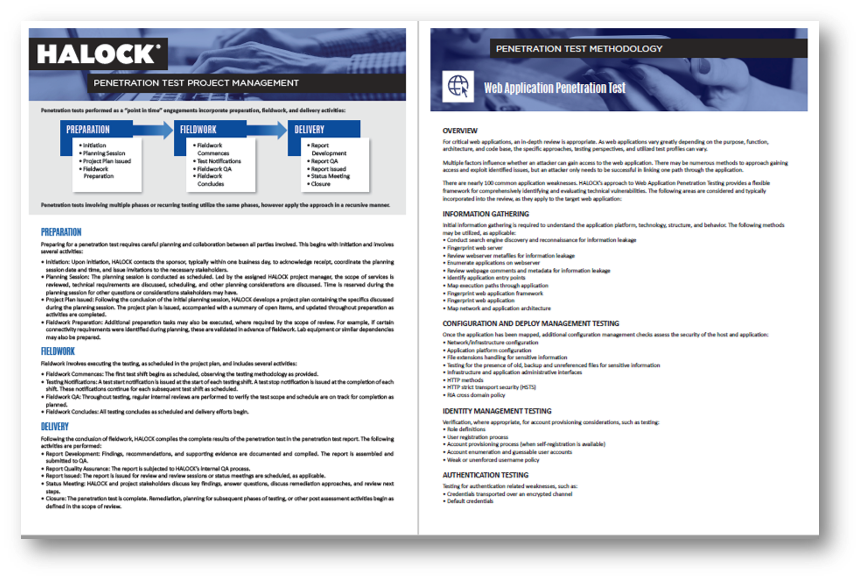
HALOCK Information Security Cyber Security Reasonable Risk
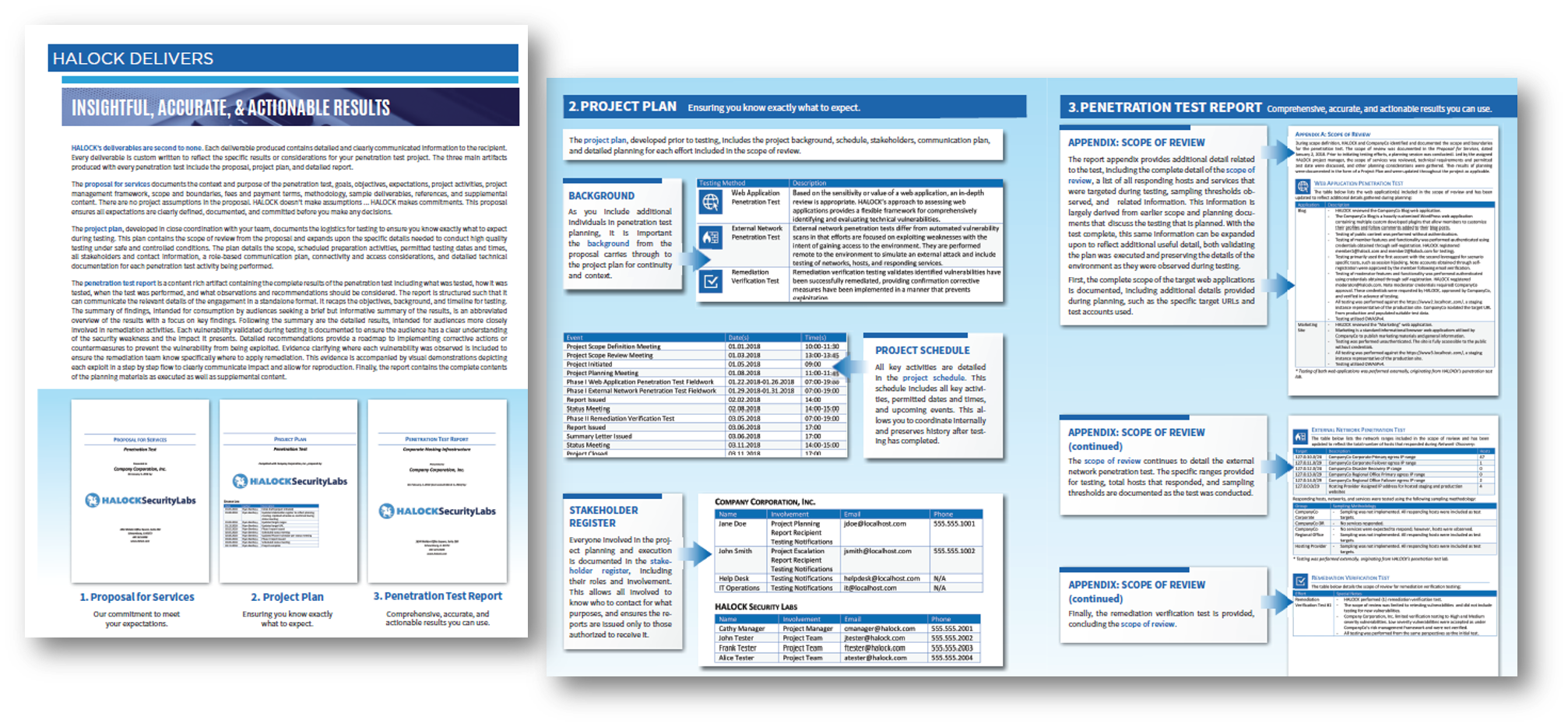
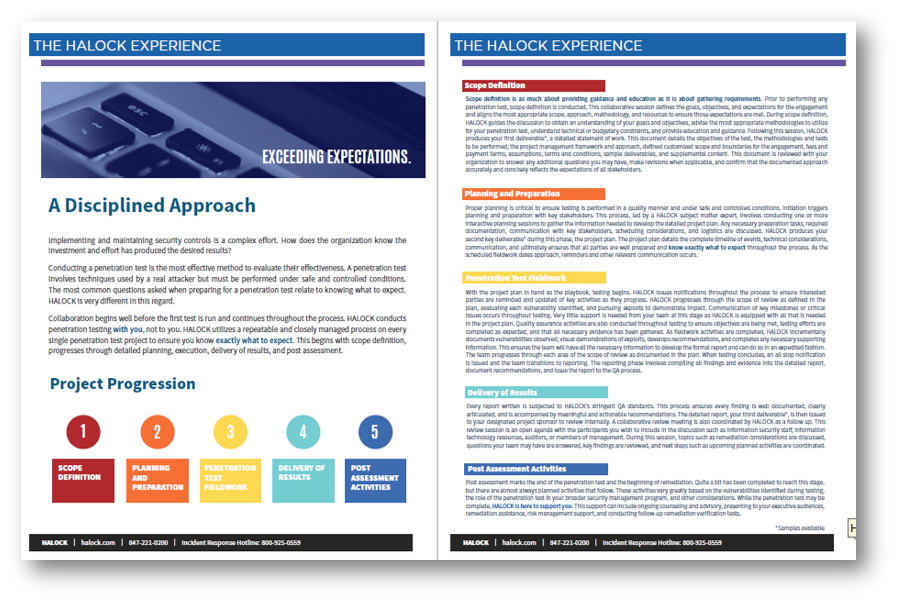
An overview of HALOCK's information security services: Security and Risk Management, Compliance (HIPAA, PCI DSS, Privacy, CMMC-readiness), Penetration Testing, Incident Response & Forensic Services, Workforce, Security Engineering and Products. HALOCK offers recurring and ongoing security programs as well as standalone services.
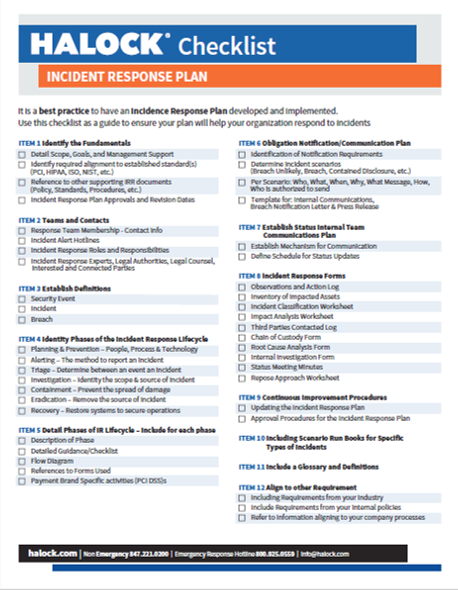
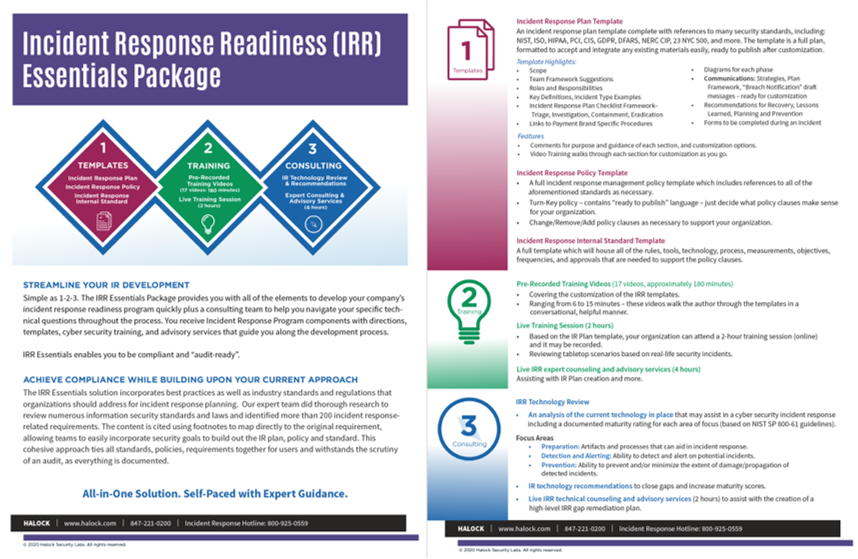
Incident Response Readiness (IRR) Essentials
The Incident Response Readiness (IRR) Essentials Package provides you with all of the elements to develop your company’s incident response readiness program quickly plus a consulting team to help you navigate your specific technical questions throughout the process. You receive Incident Response Program components with directions, templates, cyber security training, and advisory services that guide you along the development process.
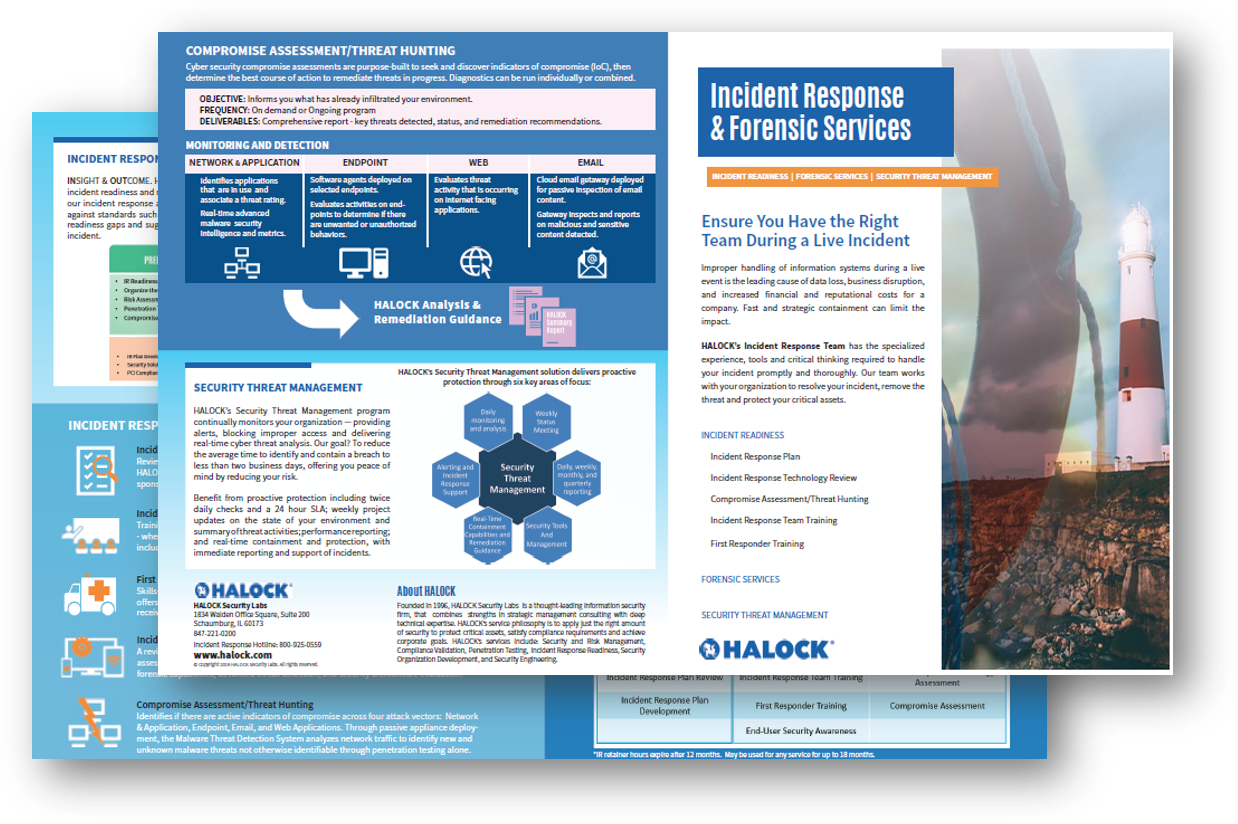
Incident Response & Forensic Services
Incident Response Readiness services include development of the Incident Response Plan (IRP), Incident Response Team Training, First Responder Training, an Incident Response (IR) Technology Review, a Threat Hunting service, and a Service Level Agreement for Live Incident Response to help mitigate your risk.