PCI DSS Compliance
Achieving and Maintaining PCI DSS Compliance | March 31, 2025 and Beyond
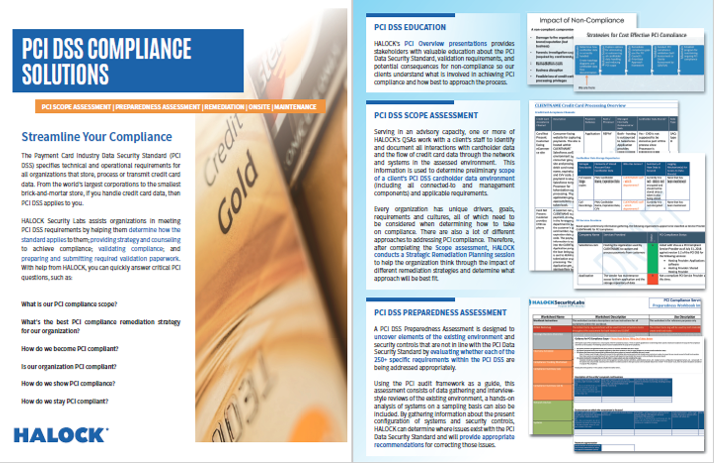
The Payment Card Industry Data Security Standard (PCI DSS) specifies technical and operational requirements for all organizations that store, process or transmit credit card data. From the world’s largest corporations to the smallest brick-and-mortar store, if you handle credit card data, then PCI DSS requirements apply to you.
“Topics were explained in an easy to understand way.”
– Restaurant Franchise chain
PCI REFERENCES & ARTICLES
FOR MANDATORY REQUIREMENTS MARCH 31, 2025 – Cipher Suites & Certificates Inventory, Service and Application Account management, SAQ-A Eligibility Criteria Update, Custom Software Inventory, PoLP for system and application accounts, Authenticated Internal vulnerability Scanning, Control Automation, Updated MFA and Password Complexity requirements, and more.
In today’s digital economy, where credit card transactions and online payments drive business, PCI DSS compliance isn’t optional—it’s required. Organizations that store, process, or transmit payment card data must comply to protect consumers and avoid costly penalties. But with a standard that’s technically complex and constantly evolving, achieving and maintaining compliance can be a real challenge.
At HALOCK, our Qualified Security Assessors (QSAs) help organizations navigate PCI DSS with clarity and confidence. We translate compliance obligations into actionable, business-aligned strategies, guiding you through readiness, remediation, validation, and reporting. Whether you’re new to PCI or updating your program, our QSAs ensure you’re on the right path.
To meet PCI DSS requirements, organizations must address several key areas:
- SCOPE VALIDATION AND OPTIMIZATION
Identify and define your Cardholder Data Environment (CDE), then implement strategies to minimize scope and risk while supporting your business goals.
- CARDHOLDER DATA REMOVAL
Remove unnecessary credit card data to meet business, legal, and compliance requirements—and ensure its securely unrecoverable.
- CLOSING COMPLIANCE GAPS
All applicable PCI DSS controls must be implemented. HALOCK’s QSAs help prioritize remediation and ensure your solutions align with PCI DSS v4.0.1 requirements.
“Extremely happy with the services. Exceed expectations in all areas of the project.”
– Chocolate company
Why HALOCK for PCI DSS Compliance?
HALOCK is uniquely positioned at the intersection of PCI DSS compliance and risk-based cybersecurity. Our PCI Qualified Security Assessors (QSAs) are not only experts in the PCI DSS framework—they also specialize in Duty of Care Risk Analysis (DoCRA), a methodology recognized in breach litigation as a standard for demonstrating reasonable security.
What sets HALOCK’s QSAs apart:
- DUAL EXPERTISE IN COMPLIANCE AND RISK
HALOCK employs the only PCI QSAs who are certified experts in both PCI DSS and Duty of Care Risk Analysis—bringing a balanced approach that addresses both regulatory and legal obligations.
- HANDS-ON TECHNICAL BACKGROUNDS
Every HALOCK QSA began their career in Information Technology before transitioning into cybersecurity, giving them a deep technical foundation and the ability to engage directly with your systems, teams, and challenges.
- LEGAL AND FORENSIC CREDIBILITY
HALOCK’s QSAs frequently serve as subject matter experts in breach litigation, helping organizations demonstrate reasonable security controls in court or during regulatory investigations.
- REAL-WORLD, RISK-ALIGNED ASSESSMENTS
Our team conducts risk assessments and compliance programs using a DoCRA-based methodology that evaluates not only the likelihood and impact of risks, but also the harm they may cause to the organization’s mission, reputation, and legal obligations.
- INNOVATORS IN TARGETED RISK ANALYSIS (TRA)
HALOCK has developed a unique approach to Targeted Risk Analysis that satisfies PCI DSS v4.0.1 requirements while leveraging DoCRA principles—ensuring your controls are not just compliant, but appropriate and defensible.
When you work with HALOCK, you’re partnering with a team that blends regulatory expertise, technical depth, and legal awareness to help you achieve PCI compliance with clarity and confidence.
Am I PCI DSS Compliant?
Perhaps you’ve already taken steps toward PCI DSS compliance—but aren’t certain if you’ve met all the requirements. That uncertainty can leave your organization exposed to risk and unprepared for formal validation.
HALOCK offers a comprehensive PCI DSS preparedness assessment designed to evaluate your current compliance posture. Our QSAs will review each applicable requirement in detail to:
- Identify any existing compliance gaps
- Assess readiness for validation
- Provide clear, actionable guidance to address deficiencies
Whether you’re approaching a self-assessment (SAQ) or preparing for a Report on Compliance (ROC), HALOCK will ensure you know exactly where you stand—and what’s needed to close the gap with confidence.

How Do I Show PCI DSS Compliance?
Demonstrating PCI DSS compliance depends on your organization’s transaction volume and business model. Some organizations are required to complete a full on-site assessment and deliver a Report on Compliance (ROC), while others may qualify to submit a Self-Assessment Questionnaire (SAQ).
Regardless of your validation path, HALOCK’s Qualified Security Assessors (QSAs) provide expert support to ensure you’re fully prepared. We help you:
- Determine the appropriate validation method (ROC vs. SAQ)
- Review and validate supporting documentation and evidence
- Evaluate the effectiveness of your security controls
- Author and submit the necessary compliance reports
With HALOCK, you’ll be equipped to confidently demonstrate your PCI DSS compliance—whether to acquirers, partners, or regulatory authorities.

How Do I Stay PCI DSS Compliant?
Achieving PCI DSS compliance is just the beginning—staying compliant is an ongoing commitment. Because PCI compliance is a point-in-time validation, organizations must continuously monitor, maintain, and adapt their security controls to remain aligned with the standard.
HALOCK’s Compliance Maintenance Program is designed to support this continuous effort. Our QSAs help you:
- Monitor and manage PCI-related maintenance activities year-round
- Prepare for annual validations and minimize surprises
- Assess the compliance impact of new technologies, vendors, or business initiatives
- Receive ongoing advisory support from certified PCI QSAs
- Foster continual improvement and readiness throughout the year
Whether you need periodic check-ins, ad hoc consulting, or a structured compliance management plan, HALOCK provides the experience and expertise to help you maintain PCI DSS compliance with confidence.

PCI DSS Scope Definition
Defining the right scope is one of the most critical—and challenging—steps in achieving PCI DSS compliance. A properly scoped environment ensures you apply the standard effectively, reduce unnecessary effort, and minimize risk exposure.
Organizations often pursue scope reduction strategies to simplify compliance, lower costs, and limit the systems subject to PCI DSS controls. These strategies can be applied individually or in combination, depending on the organization’s infrastructure, business needs, and risk posture.
At HALOCK, our Qualified Security Assessors (QSAs) work closely with your team to:
- Identify and map all credit card acceptance channels
We analyze how payment data flows across your network and determine which system components store, process, or transmit cardholder data
- Evaluate third-party service provider involvement
We account for any outsourcing arrangements that may affect your PCI obligations or reduce your compliance footprint.
- Determine your preliminary cardholder data environment (CDE) scope
Based on our analysis, we identify which parts of your environment fall in scope and why.
- Deliver strategic, risk-based scope reduction recommendations
Our QSAs offer customized scope optimization strategies that help you reduce compliance complexity while preserving security and business operations.
If your goal is to reduce PCI DSS scope while maintaining compliance, this is where the process should begin. HALOCK’s Scope Validation service lays the foundation for an efficient, risk-aligned, and sustainable compliance program.

PCI DSS Preparedness Assessment
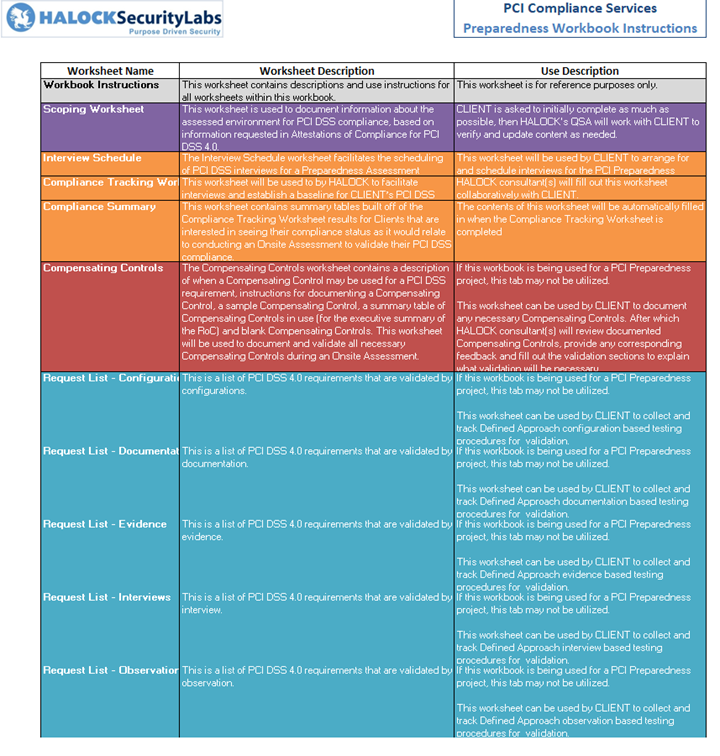
PCI DSS includes more than 200 technical and operational requirements—many of which extend beyond IT and impact core business functions. Preparing for compliance requires more than just checking boxes; it demands a clear understanding of your environment, obligations, and readiness.
HALOCK’s PCI DSS Preparedness Assessment is designed to give you that clarity. As part of the process:
- Our QSAs first validate your PCI DSS scope, identifying systems, data flows, and service providers that fall within the cardholder data environment (CDE).
- We then determine which PCI DSS requirements apply specifically to your environment, based on your business model and scope.
- HALOCK conducts in-depth interviews with key personnel to assess your current compliance posture and establish a baseline.
- Our QSAs identify any gaps in compliance and provide a prioritized roadmap of remediation recommendations, tailored to your organization’s risk, resources, and compliance goals.
This assessment is ideal for organizations preparing for their first PCI DSS validation or those looking to confirm readiness ahead of a formal SAQ or ROC. With HALOCK, you gain actionable insight—not just a checklist.

PCI DSS Remediation
You’ve assessed your PCI DSS compliance posture and identified the gaps—now it’s time to close them. Getting from assessment to full compliance requires the right mix of technical solutions, security expertise, and project oversight.
HALOCK provides a comprehensive suite of PCI DSS remediation and security program management services to help you address compliance gaps efficiently and effectively.
Our approach includes:
- Technical Remediation Support
HALOCK’s security engineers work closely with your team to design and implement the right technical controls—ensuring that each solution aligns with PCI DSS requirements and your operational needs. - Compliance and Program Management
Our PCI compliance consultants can lead or support your remediation initiatives through project management, process improvement, and business analysis, ensuring progress stays on track and aligned with priorities.
From gap identification to fully implemented, validated controls, HALOCK helps you navigate the remediation process with structure, speed, and confidence.
PCI DSS Validation
PCI DSS validation is the final step in demonstrating compliance—and it varies based on your transaction volume and business model. Organizations may be required to complete either:
- A Report on Compliance (ROC) through an on-site assessment (typically for higher-volume merchants), or
- A Self-Assessment Questionnaire (SAQ) for smaller environments or lower transaction volumes.
Regardless of your validation path, HALOCK’s Qualified Security Assessors (QSAs) provide expert support to help you:
- Validate and compile the required documentation and evidence
- Assess the effectiveness of security controls
- Author the appropriate compliance reports
- Officially register and demonstrate your PCI DSS compliance
Why Organizations Choose HALOCK for PCI DSS Validation
- Deep technical and operational understanding of PCI DSS requirements
- Proven methodology, efficient tools, and a tested delivery framework
- Dedicated QSAs and PCI compliance consultants assigned to your program
- Seamless integration with HALOCK’s Penetration Testing and technical services teams
- A Purpose Driven Security® approach—focusing on the intent behind each control and aligning “reasonable security” measures with your organization’s mission, objectives, and obligations
- Legal credibility—HALOCK’s QSAs are recognized subject matter experts in breach litigation cases
Whether you’re pursuing your first validation or undergoing an annual reassessment, HALOCK delivers clear, defensible, and efficient PCI DSS validation services tailored to your specific environment.
PCI DSS v4.0.1 had over 50 compliance activities specifically require ongoing operational efforts to monitor compliance. The most common causes for noncompliance during the annual onsite validation relate to control failures related to these activities. The Compliance Maintenance Program is conducted on a regular basis to monitor and assess recurring compliance activities. The efforts performed under this program support PCI DSS “Business as Usual” activities, establish a proactive approach to validating required PCI compliance activities, and identify control failures in a timely manner that otherwise would result in non-compliance.
HALOCK’s Purpose Driven Security® philosophy and approach help you achieve and maintain PCI compliance in a manner that is aligned with your mission. Regardless of the state of your current PCI compliance requirements and ongoing business needs, HALOCK can help your organization meet PCI compliance goals. Our QSAs are experienced PCI security consultants who will help with all your PCI compliance assessment, remediation, validation and maintenance efforts.
“The Team was great! Thank you!”
– Transportation company
Download the PCI DSS Compliance Brochure.
“Viv has been a great partner to work with and has done a great job this year as well.”
– CISO, Private Research University
HALOCK is a risk management and cybersecurity firm headquartered outside of Chicago in Schaumburg, IL, and advises clients on PCI DSS compliance solutions, including reasonable information security strategies and programs for risk management, cloud security assessments, third-party risk management, incident response readiness, threat hunting or managed detection and response (MDR), ransomware risk assessment, penetration testing, sensitive data management and scanning, and more throughout the US.