A Comprehensive Approach to Manage Your Risk
Manage Your Risk with Confidence and Accountability
In today’s digital world, risk is no longer confined to the IT department. It touches every part of your organization — and every stakeholder has a vested interest in how well you manage your risk. From your cybersecurity team and executive leadership to compliance officers, regulators, partners, and even the public, everyone depends on your ability to identify, assess, and respond to threats effectively.
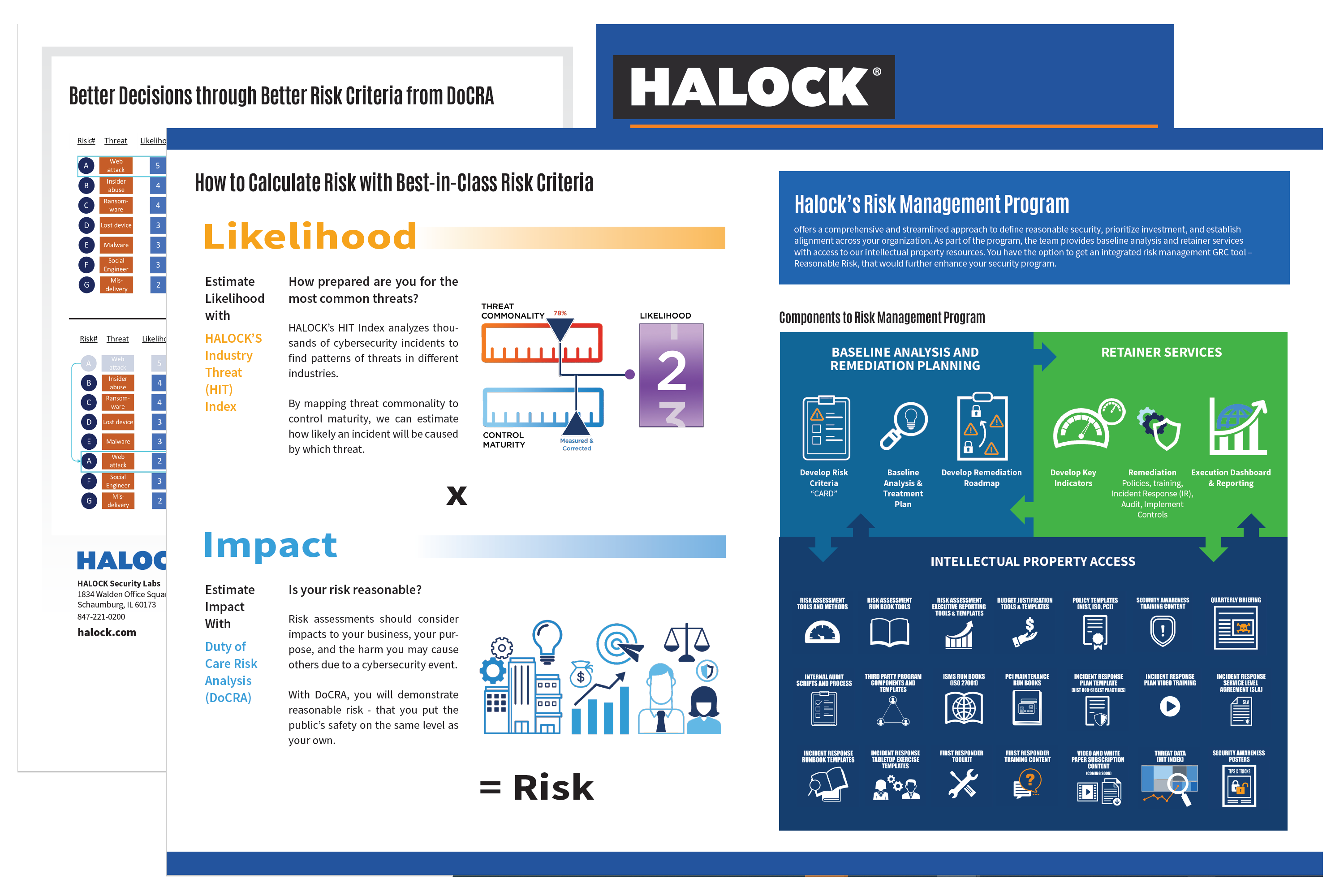
Download the Risk Management brochure
So how do you manage your risk in a way that’s not just reactive — but proactive, inclusive, and aligned with business priorities?
The answer lies in building a risk management strategy that goes beyond technical fixes and integrates a broader framework of accountability, transparency, and care. That means your risk strategy must be clear, collaborative, and rooted in principles that demonstrate you are practicing reasonable security — not just for compliance, but for real-world resilience.
Have You Considered These Critical Factors in Your Risk Operations?
When developing a strategy to manage your risk, it’s not enough to focus solely on technical vulnerabilities or compliance checklists. You must consider:
Stakeholder Impact – Who is affected by your risk decisions? Are your board members informed? Is your communications team equipped to handle a breach? What about your customers and end users?
Regulatory Expectations – Are you meeting legal standards and industry regulations like GDPR, HIPAA, or CCPA? Can you demonstrate your efforts toward ‘reasonable security’ if challenged?
Duty of Care – Have you adopted frameworks such as Duty of Care Risk Analysis (DoCRA), which help balance security, compliance, and business interests in a measurable, responsible way?
Business Continuity – Do you have the processes in place to recover from incidents quickly with minimal disruption to operations or customer trust?
Cultural Integration – Does your team understand the why behind your risk controls? Is risk awareness built into your company culture?
A Risk Strategy That Serves Everyone
To effectively manage your risk, you need a strategy that aligns IT with business goals and bridges communication across departments. It should empower your organization to make informed decisions — ones that balance risk with reward and security with productivity.
When you embed risk thinking into your day-to-day operations, your business becomes more adaptable, more secure, and more trustworthy.
Let Us Help You Manage Your Risk More Effectively
Our team helps organizations create and execute tailored risk management programs based on proven frameworks like DoCRA. We focus on helping you:
Understand your critical assets and vulnerabilities
Prioritize risks based on potential business impact
Engage stakeholders at every level
Demonstrate reasonable security to regulators and the public
Build resilience through continuous monitoring and improvement
Whether you’re preparing for an audit, responding to increased threats, or just want more control over your digital risk landscape, we can help you manage your risk with confidence.