There is a new deadline that Department of Defense (DOD) contractors and vendors need to be aware of. The deadline concerns Cybersecurity Maturity Model Certification (CMMC). CMMC was implemented by the U.S. Department of Defense on January 31, 2020 in order to be more proactive concerning compliance with the National Institute of Standards and Technology (NIST) security controls. The primary objective of CMMC is to properly secure Controlled Unclassified Information (CUI) throughout the DOD supply chain. This includes any type of information or data created or possessed by the government or any entity on the government’s behalf. This includes data such as government financial information, research data, critical infrastructure plans, etc.
Prior to CMMC, contractors were responsible for certifying their own security controls and information technology systems. CMMC changed this standard by requiring third-party assessments in order to confirm compliance and adherence to mandatory practices and procedures for all DOD contractors. These mandatory practices center around 17 capability domains such as Access Control, Incident Response, Risk Management and Asset Management to name a few.
The original intention of CMMC was to slowly phase in the number of DOD contracts that would require certification up until October 1, 2025. At that point, all DOD contacts would fall under strict CMMC compliance. DOD contractors include any type of business that provides services or goods to the DOD including IT services, bookkeeping and janitorial services. If you do business with the DOD, then CMMC affects you.
The Interim Rule has Changed Things
If you are a DOD contractor (or plan to be) and thought that the only hard deadline you had to worry about was five years from now, think again. On September 29, 2020, the DOD issued an interim rule to accelerate efforts to attain compliance and adherence to NIST 800-171 requirements. The interim rule introduces two new DFARS clauses: DFARS 252.204-7021 and DFARS 252.204-7020. It also introduces a new potential deadline of November 30, 2020 that will affect many DOD contractors.
The primary concern for DOD contractors is the mandatory obligation to perform a “basic self-assessment” concerning their current state of compliance with NIST 800-171. Results of the assessment must then be submitted to the DOD. Contractors will then have to update this self-assessment every three years, or sooner, if required by an involved contract. The key aspect of all of this is that starting November 30, 2020, contractors will not be eligible for new contracts unless the self-assessment has been properly implemented and posted.
It is extremely important to note that the DOD anticipates that the submission process will take 30 days. This means that current and potential contractors need to submit their assessment score (based on a published scoring criteria) by the end of October. While the interim rule does not require complete compliance with NIST 800-171, contracts must submit a date for when they anticipate full compliance in addition to the self-assessment. Contractors that have completed these essential steps will remain eligible for new contracts.
The self-assessment methodology can be accessed at the Office of the Under Secretary of Defense for Acquisition & Sustainment website.
More about CMMC
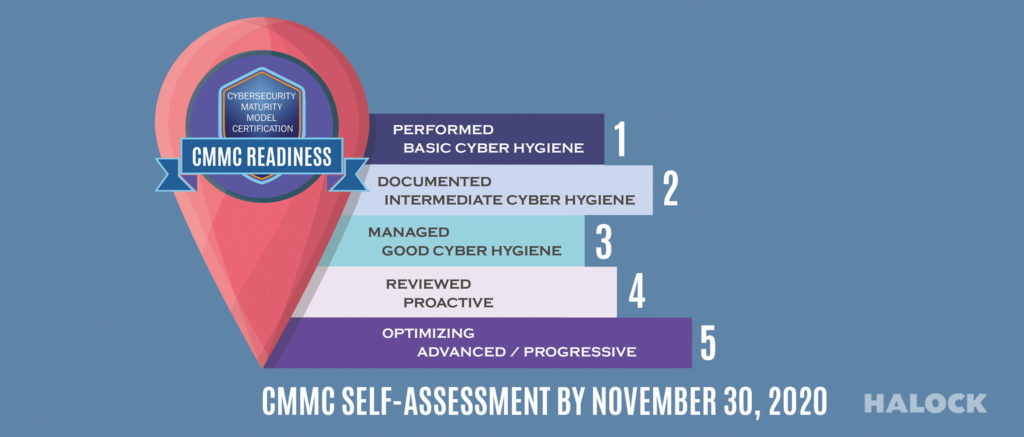
CMMC takes an incremental approach that sets different levels of requirements depending on the industry and company. There are currently 5 CMMC levels.
- Level 1 demonstrates basic cyber hygiene and requires DOD contractors to pass an audit involving 17 controls of NIST 800-171 rev1. The six domains involved in this proof of basic compliance includes Access control, Identification and Authentication, Media Protection, Physical Protection, System and Communications Protection and System and Information Integrity.
- Level 2 is deemed an intermediate level that introduces 55 additional controls. Requirements include steps such as the logging and monitoring of user activity involving enterprise systems as well as well as the implementation of basic cybersecurity training for all users.
- Level 3 requires complete compliance with the full slate of NIST requirements as well as 20 CMMC practices. If your company works with CUI, you will most likely be required to attain level 3 compliance.
- Levels 4 and 5 are proactive levels involving advanced practices and are reserved for contractors that can be expected to be subject to advanced persistent threats involving adversarial intentions.
Time to Assess
While all current and future DOD contractors must have a long-term strategy in order to fulfill their required CMMC level by the 2025 deadline, the immediate concern is to complete the self-audit submission process by the pending deadline of November 30, 2020. Due to the anticipated 30-day submission process, it is imperative to act fast. Those involved in a current contract need to determine what impact the interim rule has on it. If required, it is imperative to start the basic self-assessment now. A self-assessment does not have to be performed by your own organization. The fastest and most efficient way to implement the assessment is to have a third-party auditor that is trained and knowledgeable in the NIST 800-171 and CMMC control sets, and the scoring process. An outside specialist team will not only save you precocious time, but money as well.
As time is of the essence, we invite you to contact us today and allows us to outline our proven NIST 800-171 and CMMC expertise, and implementation strategies. Let our team of experts help you navigate November deadline requirements for you, so that you can concentrate on your core business.
SOURCES:
- National Law Review: Updated Cybersecurity Assessment Requirements for Federal Contractors
- JD Supra: New Department of Defense Regulations Clarify Contractors’ Responsibilities to Comply with NIST SP 800-171 and CMMC Requirements
- Federal News Network: DoD’s interim rule adds a new twist to implementing cyber maturity model
</font size=3>