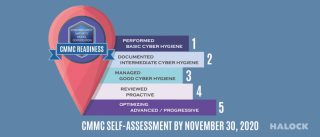
New Interim Rule Requires CMMC Self-Assessment by November 30, 2020
There is a new deadline that Department of Defense (more…)
CMMC 101: The Basics of Cybersecurity Maturity Model Certification
WHAT IS CMMC? CMMC (more…)
NIST Cyber Security Risk Management Conference – Reasonable Risk
NIST Cyber Security Risk Management Conference – Reasonable Risk. Our partner, Chris (more…)
PCI DSS v3.1 Coming – SSL No Longer Considered Strong Cryptography
SSL No Longer Considered Strong Cryptography
In a recent (more…)
Darrell Issa Just Learned the Difference Between Compliance and Security. Let’s Hope for a Payoff.
Darrell Issa’s House Committee on Oversight and Government Reform has been (more…)
New Draft Guidance from NIST for Cloud Computing
Guidance from NIST for Cloud Computing. With the rapid trend towards (more…)




 (more…)
(more…)
