Cindy Kaplan2024-08-01T18:22:55+00:00Tags: Compliance, HCCA, healthcare, HIPAA, reasonable and appropriate, reasonable risk, reasonable security, risk analysis|
Author! Author! Happy Hour at RSA
Highlight your RSA Experience at the Author! Author! Happy (more…)
NIST Cyber Security Risk Management Conference – Reasonable Risk
NIST Cyber Security Risk Management Conference – Reasonable Risk. Our partner, Chris (more…)
WHAT IS HIPAA?
HALOCK is deep in the regulatory compliance and (more…)
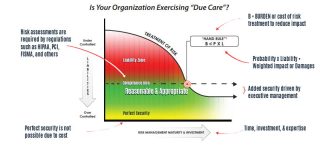
Risk Acceptance Levels: Managing the Lower Limits of Security Costs
Last week I presented a topic here at Halock’s blog site (more…)
The Hand Rule: Managing the Upper Limits of Security Costs
While presenting a talk at CAMP IT last week I got (more…)
Are iPads HIPAA Compliant?
I hear this question very often. It is similar to the (more…)
UNLIMITED SECURITY BUDGETS AND PERFECT SECURITY
Perfect security is not possible, feasible nor (more…)