RISKS
What happened
In August 2022, Cisco Systems revealed details of a May 2022 hack by the Yanluowang ransomware group that leveraged a compromised employee’s Google account. Cisco called the attack a “potential compromise” in a post by the company’s own Cisco Talos threat research arm.
“During the investigation, it was determined that a Cisco employee’s credentials were compromised after an attacker gained control of a personal Google account where credentials saved in the victim’s browser were being synchronized,” wrote Cisco Talos in a lengthy breakdown of the attack.
Forensic details of the attack lead Cisco Talos researchers to attribute the attack to the Yanluowang threat group, which they maintain has ties to both the UNC2447 and the notorious Lapsus$ cybergangs.
Ultimately, Cisco Talos said the adversaries were not successful at deploying ransomware malware, but they were successful at penetrating its network and planting a cadre of offensive hacking tools and conducting internal network reconnaissance “commonly observed leading up to the deployment of ransomware in victim environments.”
“Initial access to the Cisco VPN was achieved via the successful compromise of a Cisco employee’s personal Google account. The user had enabled password syncing via Google Chrome and had stored their Cisco credentials in their browser, enabling that information to synchronize to their Google account,” wrote Cisco Talos.
With credentials in their possession, attackers then used a multitude of techniques to bypass the multifactor authentication tied to the VPN client. Efforts included voice phishing and a type of attack called MFA fatigue. Cisco Talos describes the MFA fatigue attack technique as “the process of sending a high volume of push requests to the target’s mobile device until the user accepts, either accidentally or simply to attempt to silence the repeated push notifications they are receiving.”
The MFA spoofing attacks leveraged against Cisco employee were ultimately successfully and allowed the attackers to run the VPN software as the targeted Cisco employee. “Once the attacker had obtained initial access, they enrolled a series of new devices for MFA and authenticated successfully to the Cisco VPN,” researchers wrote.
“The attacker then escalated to administrative privileges, allowing them to login to multiple systems, which alerted our Cisco Security Incident Response Team (CSIRT), who subsequently responded to the incident,” they said.
Tools used by attackers included LogMeIn and TeamViewer and also offensive security tools such as Cobalt Strike, PowerSploit, Mimikatz and Impacket.
Why is this important?
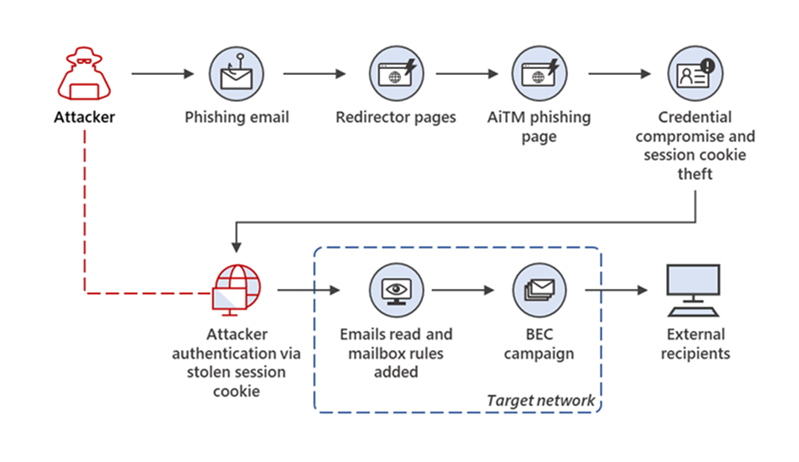
While MFA is essential for organization security, it can still be hacked. In July 2022, Microsoft researchers uncovered a large-scale phishing campaign that used adversary-in-the-middle (AiTM) phishing sites stole passwords, hijacked a user’s sign-in session, and skipped the authentication process even if the user had enabled MFA. Based on their threat data, the AiTM phishing campaign attempted to target more than 10,000 organizations since September 2021. Here is an overview of the AiTM phishing campaign and follow-on business email compromise (BEC) campaign:
Image Source: Microsoft
What does this mean to me?
As hackers continue to find new ways into corporate systems, risk assessments and cyber security awareness training are more important than ever to stay ahead of the curve. Adequate training could have possibly prevented the employee from accepting the attacker’s MFA push notifications. Additionally, incident response readiness could have shortened the time for the company to have responded to and provided notification regarding the data breach.
Customers using Azure should also consider complementing MFA with conditional access policies, where sign-in requests are evaluated using additional identity driven signals like user or group membership, IP location information, and device status, among others.
APPROACHES
Helpful Controls
Commonality of attack
Medium
Article on story
Cisco Confirms Network Breach Via Hacked Employee Google Account
HALOCK Security Briefing Archives: Updates on cybersecurity trends, threats, legislation, reasonable security, duty of care, key acts and laws, and more that impact your risk management program.
SCHEDULE YOUR FULL HALOCK SECURITY BRIEFING