External Network Penetration Testing

How Secure Are Your Internet-Facing Networks, Systems and Services?
Experts predict an increase in technology in artificial intelligence (AI), quantum computing, supply chains, cloud security and more, which will require more comprehensive penetration testing on our security controls. Proactively assess new vulnerabilities and threats. Fulfill your compliance, regulatory or other external requirements to test your environment and ensure they are effective. Our comprehensive external penetration testing can support your security needs while mitigating your risks.

External penetration testing services focus on exploiting network security weaknesses.
How effective are your safeguards?
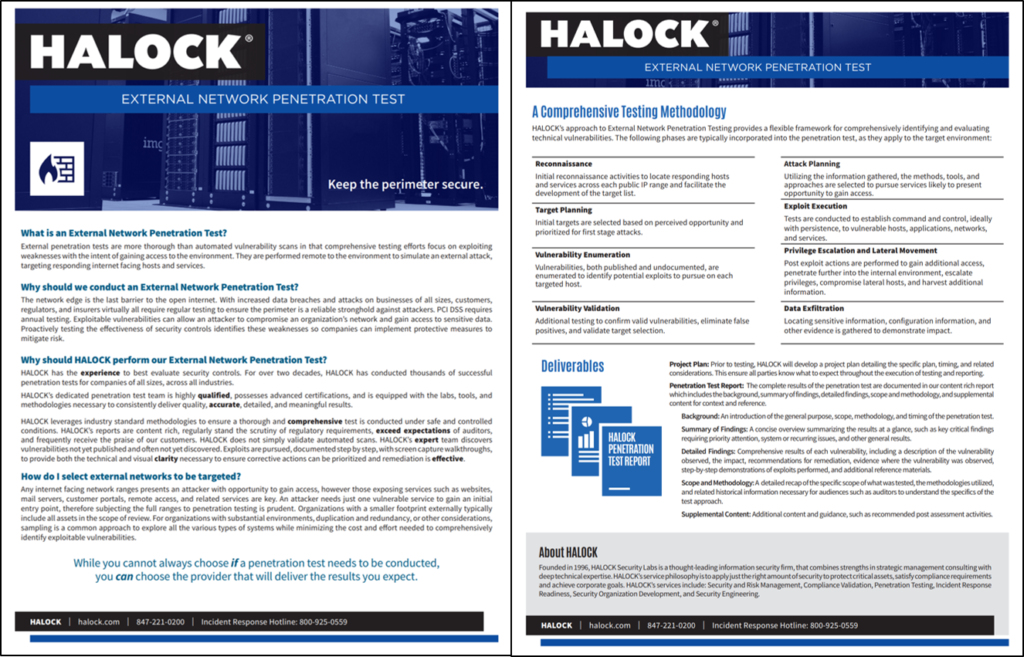
External network penetration testing is more thorough than automated vulnerability scans in that comprehensive external pen test efforts focus on exploiting weaknesses with the intent of gaining access to the environment. They are performed remote to the environment to simulate an external penetration attack, targeting responding internet facing hosts and services.

Why should we conduct external penetration testing?
The network edge is the last barrier to the open internet. With increased data breaches and attacks on businesses of all sizes, customers, regulators and insurers virtually all require external penetration testing services to ensure the perimeter is a reliable stronghold against attackers. PCI DSS requires annual testing, such as external pentests and evaluations.
Exploitable vulnerabilities can allow an attacker to compromise an organization’s network and gain access to sensitive data. Proactively testing the effectiveness of security controls with external network penetration testing identifies these weaknesses so companies can implement protective measures to mitigate risk.
“Great process.”
– Healthcare Consulting and Technology Company
Why should HALOCK perform our External Network Penetration Test?
HALOCK has the experience to best evaluate security controls. For over two decades, HALOCK has conducted thousands of successful penetration tests for companies of all sizes, across all industries.
HALOCK’s dedicated penetration test team is highly qualified, possesses advanced certifications, and is equipped with the labs, tools, and methodologies necessary to consistently deliver quality, accurate, detailed, and meaningful results.
HALOCK leverages industry standard methodologies to ensure a thorough and comprehensive test is conducted under safe and controlled conditions. HALOCK’s reports are content rich, regularly stand the scrutiny of regulatory requirements, exceed expectations of auditors, and frequently receive the praise of our customers. HALOCK does not simply validate automated scans. HALOCK’s expert team discovers vulnerabilities not yet published and often not yet discovered. Exploits are pursued, documented step by step, with screen capture walkthroughs, to provide both the technical and visual clarity necessary to ensure corrective actions can be prioritized and remediation is effective.
How do I select external networks to be targeted?
Any internet facing network ranges presents an attacker with opportunity to gain access, however those exposing services such as websites, mail servers, customer portals, remote access, and related services are key. An attacker needs just one vulnerable service to gain an initial entry point, therefore subjecting the full ranges to penetration testing is prudent. Organizations with a smaller footprint externally typically include all assets in the scope of review. For organizations with substantial environments, duplication and redundancy, or other considerations, sampling is a common approach to explore all the various types of systems while minimizing the cost and effort needed to comprehensively identify exploitable vulnerabilities.
“We like working with Halock. The quality of the project and the final product are usually excellent.”
– National provider of physical therapy and rehabilitation services
External Network Penetration Testing Methodology and Tools
When HALOCK undertakes external pen testing, we attempt to exploit vulnerabilities identified on networks, systems and services to gain access to sensitive information using any appropriate means at our disposal. We perform testing under controlled conditions to minimize the risk of disruption. The goal is to provide comprehensive details regarding the security weaknesses present in your environment.
Multiple factors influence whether an attacker can access your environment externally. While numerous methods may allow access and exploitation of identified threats, an attacker needs to be successful only in linking one path into the environment.
HALOCK’s approach to pen testing is summarized as follows: Locate target hosts and services, evaluate the security of those targets via penetration test tools and methods, attempt to gain access to the target hosts, and escalate privileges throughout the environment.
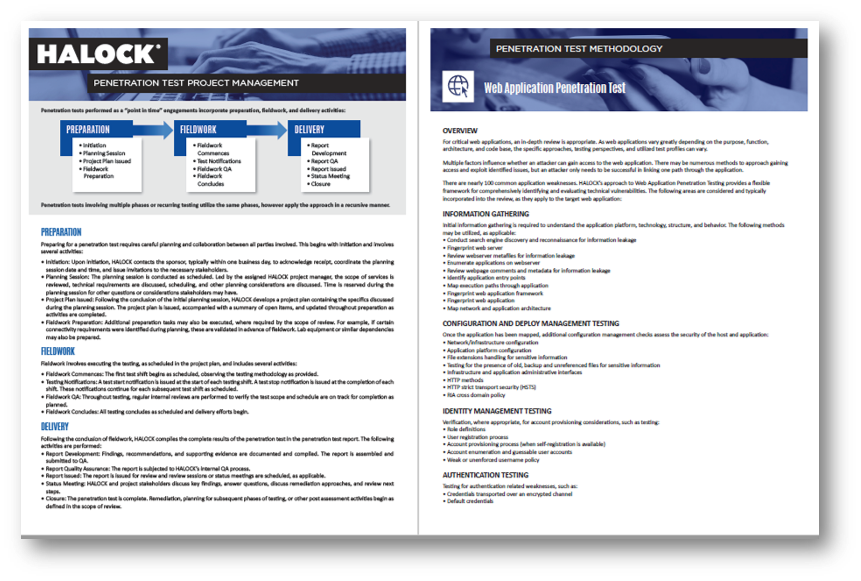
Our detailed methodology includes the following phases:
- RECONNAISSANCE: Initial reconnaissance activities to locate responding hosts and services across each public IP range and facilitate the development of the target list.
- TARGET PLANNING: Initial targets are selected based on perceived opportunity and prioritized for first stage attacks.
- VULNERABILITY ENUMERATION: Vulnerabilities, both published and undocumented, are enumerated to identify potential exploits to pursue on each targeted host.
- VULNERABILITY VALIDATION: Additional testing to confirm valid vulnerabilities, eliminate false positives, and validate target selection.
- ATTACK PLANNING: Utilizing the information gathered, the methods, tools, and approaches are selected to pursue services likely to present opportunity to gain access.
- EXPLOIT EXECUTION: Tests are conducted to establish command and control, ideally with persistence, to vulnerable hosts, applications, networks, and services.
- PRIVILEGE ESCALATION AND LATERAL MOVEMENT: Post exploit actions are performed to gain additional access, penetrate further into the internal environment, escalate privileges, compromise lateral hosts, and harvest additional information.
- DATA EXFILTRATION: Locating sensitive information, configuration information, and other evidence is gathered to demonstrate impact.
“The process was super smooth with great communication and quick handling of a late addition we had in December. The team went out of their way to make that request happen. Great experience all the way around.”
– Authentication Services Organization
Deliverables
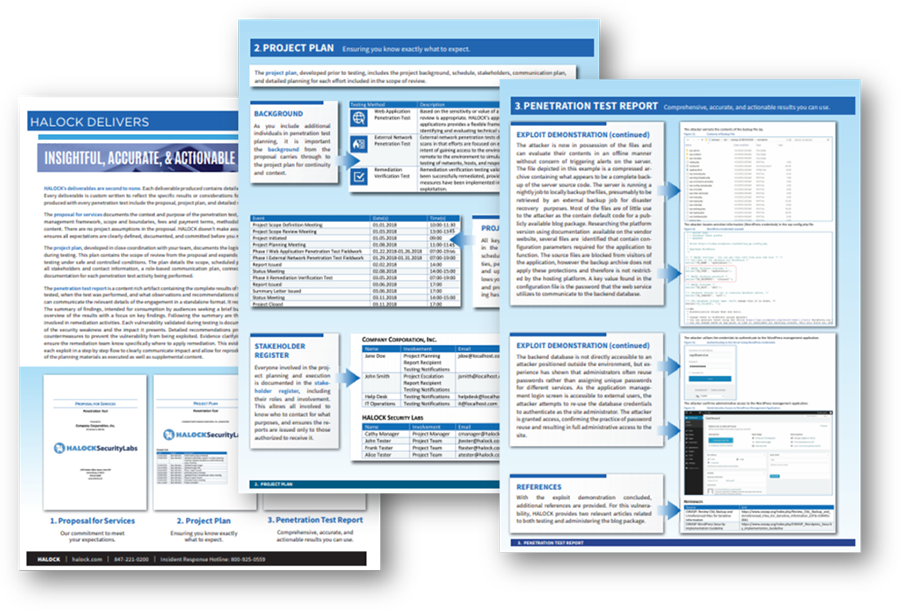
Project Plan: Prior to testing, HALOCK will develop a project plan detailing the specific plan, timing, and related considerations. This ensure all parties know what to expect throughout the execution of testing and reporting.
Penetration Test Report: The complete penetration testing results are documented in our content rich report which includes the background, summary of findings, detailed findings, scope and methodology, and supplemental content for context and reference.
- Background: An introduction of the general purpose, scope, methodology, and timing of the penetration test.
- Summary of Findings: A concise overview summarizing the results at a glance, such as key critical findings requiring priority attention, system or recurring issues, and other general results.
- Detailed Findings: Comprehensive results of each vulnerability, including a description of the vulnerability observed, the impact, recommendations for remediation, evidence where the vulnerability was observed, step-by-step demonstrations of exploits performed, and additional reference materials.
- Scope and Methodology: A detailed recap of the specific scope of what was tested, the methodologies utilized, and related historical information necessary for audiences such as auditors to understand the specifics of the test approach.
- Supplemental Content: Additional content and guidance, such as recommended post assessment activities.
Consider a Penetration Testing program to assess your safeguards throughout the year for a proactive security approach.
“The team were great in all areas. I really appreciate all of their help.”
– Global insurance firm
KEEPING YOU INFORMED – HALOCK SECURITY BRIEFING FOR CLIENTS
The HALOCK Security Briefing is a review of significant events, trends, and movements that will influence how you manage cybersecurity, risk, and compliance. Our clients receive periodic overviews with an extensive report file on the topics discussed. This insightful document also includes reference links throughout the report for easy navigation and deeper research.
HALOCK, a trusted penetration testing and risk management company headquartered in Schaumburg, IL, near Chicago, advises clients on reasonable security strategies, risk management, and compliance throughout the US.