Malware remains a massive security problem, costing companies billions each year to manage, mitigate and remediate. While the term itself is straightforward — malware refers to any software designed to cause harm on a system or device — there are a host of malware types and techniques used by attackers to circumvent defenses and compromise key systems.
Unsurprisingly, the rapid remote work shifts of 2020 also came with a significant uptick in malware attacks. With companies suddenly managing entire workforces from home while simultaneously embracing the cloud and designing an effective mobile device policy, cybercriminals found the perfect opportunity to exploit existing weak points and explore potential threats.
Even more worrisome? Once equipped with persistent permissions to corporate systems, hackers can wreak havoc. From exfiltrating key product or performance data, to setting up back doors that empower ongoing surveillance, to deleting or encrypting key files for financial compensation; malware attacks pose critical risks for revenue, reputation and IT reliability.
In this piece, we’ll tackle five types of malware attacks, how they work and what steps your business can take to limit their impact.
1. Ransomware
Ransomware is next — and with good reason. While instances of this attack type had begun to flatten as companies deployed more robust defensive architecture, the unique IT landscape of 2020 saw a resurgence of ransomware efforts.
The concept behind ransomware is simple: Once they gain access, attackers deploy malware payloads that encrypt critical data, and then demand payment for its release. Increasing availability of ransomware-as-a-service (RaaS) tools have lowered the bar for entry, making it possible for even moderately skilled cybercriminals to attempt electronic extortion.
Some of the most common ransomware attacks — including Bad Rabbit, CryptoLocker, Cerber and Jigsaw — differ in their approaches. For example, Cerber typically leverages phishing attacks aimed at Microsoft 365 users, while Jigsaw opts for a progressive file-deletion countdown. Regardless, the outcome is often the same: If businesses are unable to remove the malware and refuse to pay the ransom, their data may be destroyed.
Savvy business owners would do well to remember that hackers are dishonest by nature — meaning that even if your company pays the ransom, you may still lose your data.
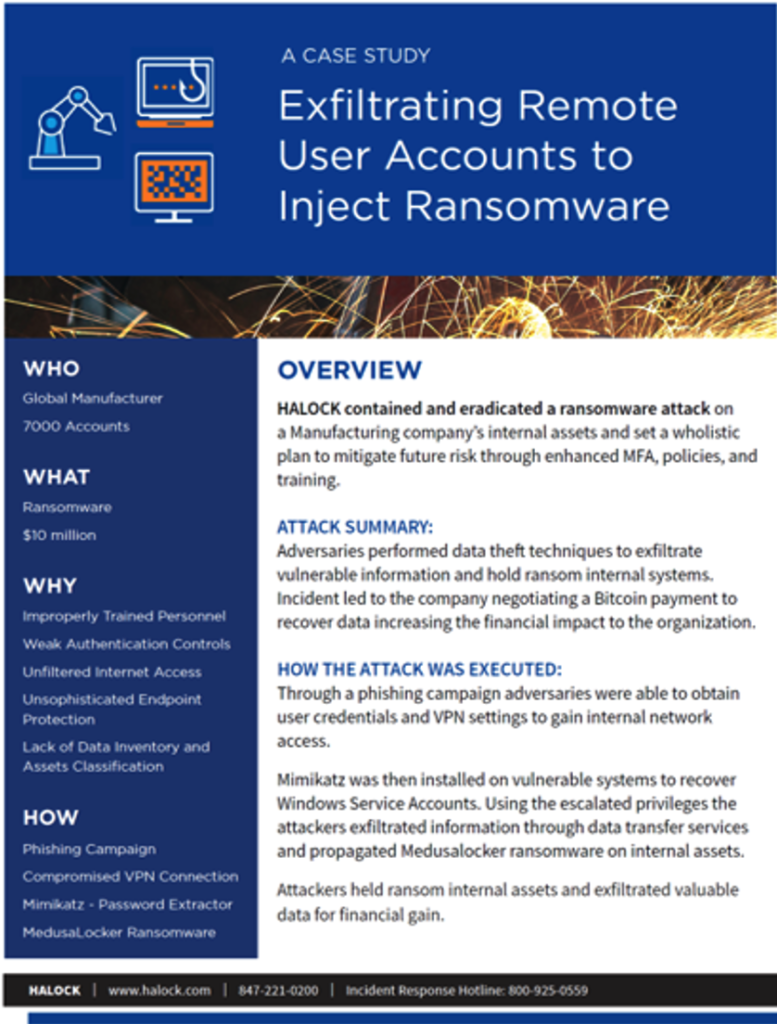
Ransomware Case Study: Learn how HALOCK eradicated a ransomware attack on a manufacturing company.
2. Trojans
Taking their name from the Trojan Horse, this type of malware is designed to appear as a legitimate program or application but is in fact malicious. In some instances, download links may be forwarded to users as part of a larger phishing campaign. In other cases, Trojans are embedded in applications available through popular third-party application stores.
Once installed on corporate systems, Trojans such as Rakhni often hide in plain sight rather than causing chaos. Some are designed simply to collect data, while others act as touchpoints for the deployment of more malicious malware strains. Trojans are also used for “cryptomining”, which repurposes corporate IT resources to mine for cryptocurrencies such as bitcoin and can significantly impact network performance.
While Trojan impacts vary by code type and intent, they often display similar symptoms. If users suddenly discover that applications and services are running much slower than usual; that overall computer usage is up; or that applications are continually asking for more robust access, a Trojan may be the cause.
3. Drive-By Attacks
Drive-by attacks make use of insecure applications or systems to deploy malware on corporate devices without raising defensive alarm bells. This often takes the form of code placed on websites that are part of a phishing campaign — when users click through, scripts run automatically to download and install malware.
These attacks often rely on operating systems and web browsers that haven’t been updated with the latest security patches and are therefore vulnerable to specific compromise vectors. What’s more, these known weaknesses are often detailed in public patch notes. This public information makes it possible for attackers to create malicious code that can bypass detection systems and allow digital threats to “drive-by” security systems, drop off malware payloads and leave without being detected.
Considering The 2021 Threat Landscape
While the bulk of cyberattacks in 2021 will mimic their 2020 counterparts, companies can’t afford static security solutions. Attackers are constantly changing their techniques, looking for new ways to compromise defenses and access critical corporate services. In fact, 2021 has already seen an uptick in COVID vaccine-related phishing attacks claiming to have special knowledge about or access to vaccine distribution campaigns and that include links or files for users to download.
2021 has also seen a steady increase of social engineering attacks aimed at staff working from home: If cybercriminals can convince employees to respond with login details or account information, they may be able to access complete corporate networks at a distance, all without being detected. The result is a malware landscape that’s constantly evolving to exploit existing weaknesses, capitalize on new threat vectors and leverage social vectors to deliver malicious, persistent payloads.
Worried about malware? HALOCK can help. From incident response and forensic services that can mitigate the impact of malware attacks and discover their root causes, to risk assessments and cyber awareness training that can limit the possibility of initial compromise — HALOCK has you covered.
Ready to get started? Let’s talk.
RESOURCES & NEWS
Learn more about Penetration Testing and new exploits in HALOCK’s Exploit Insider.
The Dangers of Legacy Protocols
PCI Targeted Risk Analysis & DoCRA
https://www.halock.com/pci-compliance-new-requirements-and-targeted-risk-analysis/
HIPAA & Penetration Testing & Incident Response Plans
Top Threats in Healthcare
https://www.halock.com/top-cyber-threats-in-healthcare/
Cloud Security Risk Management
https://www.halock.com/prioritized-findings-and-remediation-in-cloud-security-reporting/
Penetration Testing Reports to Manage and Prioritize Risk
https://www.halock.com/a-threat-based-approach-to-penetration-test-reporting/

HALOCK Breach Bulletins
Recent data breaches to understand common threats and attacks that may impact you – featuring description, indicators of compromise (IoC), containment, and prevention.