Risk Based Threat Assessment

Informed Risk Management
Did you know a ransomware attack happens about every 14 seconds? And nearly 25% of data breaches are tied to web application attacks. The reality is—cyber threats are on the rise across the board, and your team is on the front lines of managing that risk.
But here’s the question: how confident are you in your organization’s ability to bounce back if a cyberattack hits?
That’s where a Risk Based Threat Assessment comes in. By pinpointing the most likely threats to your organization, you can focus your efforts where they matter most. Regularly reviewing your controls and overall security performance gives you a clear picture of where you stand—and where you need to improve. It’s all about staying one step ahead and closing any gaps before they become problems.
Strengthen Protection Against the Five MITRE ATT&CK Types
Cyber threats are getting smarter and harder to predict every day. That’s why it’s so important to take a strategic look at how you’re defending your organization—especially against the five MITRE ATT&CK Types identified in the Center for Internet Security’s Community Defense Model.
A Risk Based Threat Assessment is your best first step. At HALOCK, we’ve built a powerful approach that blends guidance from CIS®, MITRE, NIST, and the VERIS Community Database (VCDB). Using our Duty of Care Risk Analysis (DoCRA) methodology, the HALOCK Risk-Based Threat Assessment helps you understand where your biggest vulnerabilities are and what to do about them—without wasting time or resources.
This assessment helps you prioritize which security controls to strengthen or put in place, using the latest and most trusted threat data in the industry. That way, you’re focusing your budget and efforts on what matters most—and becoming more resilient against attacks that really matter.
The Five MITRE ATT&CK Types we target:
- Ransomware attacks
- Malware attacks
- Insider abuse
- Web application attacks
- Persistent external threats
The Methodology and Deliverables
Our Risk Based Threat Assessment is built on the trusted DoCRA framework and starts with something simple—but powerful: a conversation. We conduct interviews with your team to get a clear understanding of how your current security measures are actually working day to day, using the CIS Critical Security Controls as our guide.
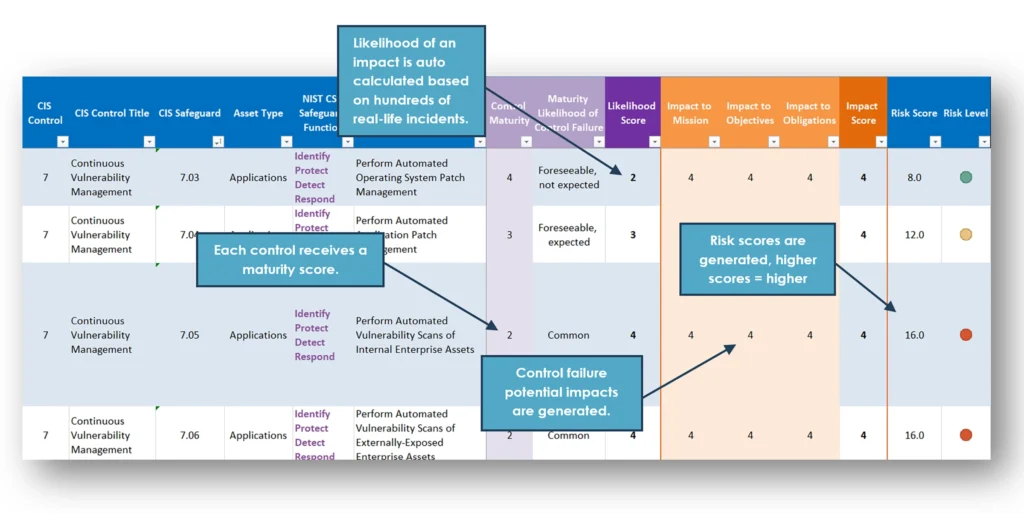
From there, we create a detailed risk register that outlines your organization’s specific threats. Each relevant CIS control is scored, giving you a clear, measurable picture of your current security posture—and where you can improve. It’s a practical, data-driven way to make informed decisions about your cybersecurity strategy.
Visualizing Risk: Heat Maps by Attack Type
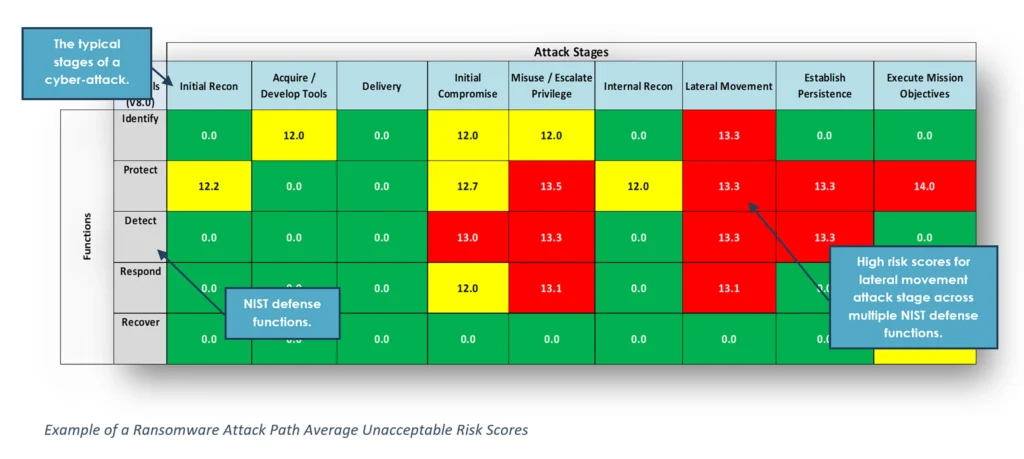
Once your risk based threat assessment is complete and we’ve scored the CIS controls in your risk register, we take things a step further by making the results visual and actionable.
For each type of cyberattack, we generate a heat map that highlights exactly where your biggest vulnerabilities lie. These maps make it easy to see which threats pose the greatest risk to your organization, so you can focus your time, energy, and budget where it counts most.
Actionable Insights at Every Step
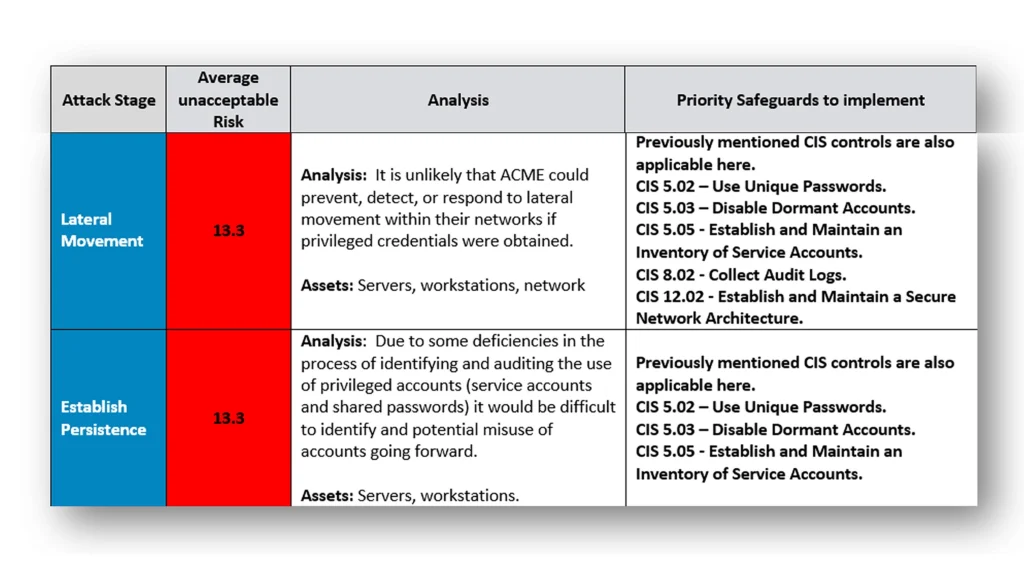
Throughout your Risk Based Threat Assessment, we don’t just hand over data—we guide you through it. At each stage, we provide clear analysis and tailored recommendations, so you know exactly what to tackle first.
You’ll walk away with a priority roadmap that helps you strengthen your risk posture in a strategic, efficient way. No guesswork—just a focused plan to improve your defenses where they’re needed most.
Prioritized Options That Fit Your Needs
Our Risk Based Threat Assessment is built to work the way you need it to. Whether you’re looking for a one-time project or want to make it part of an ongoing, annual program, we’ve got you covered. You can focus on just one attack type—or assess all five. And if you already have a risk register, great! We can build on that. If not, we’ll help you start fresh.
Prioritize What Matters Most, First
With our approach, you’re not just checking boxes—you’re making smart, targeted decisions based on your unique risk profile. We help you prioritize remediation based on:
- The maturity of your current security controls
- NIST CSF Security Functions
- Risk levels tied to each control
- The five MITRE ATT&CK Types
- A customized roadmap to move from your current risks toward what’s considered ‘reasonable’ protection
Why Choose HALOCK?
At HALOCK, we don’t just use industry standards—we help create them. As the authors of the DoCRA Standard and developers of CIS RAM, we bring a level of risk expertise that’s hard to match. Our deep knowledge helps you apply a Risk Based Threat Assessment approach that ensures your security controls are not only effective but also reasonable and appropriate for your unique environment.
Headquartered in Schaumburg, IL, near Chicago, HALOCK is a trusted cybersecurity and risk management consulting firm serving clients across the U.S. We’re here to help you make smarter, more legally-defensible decisions about your security posture.
Estimating Risk with Real-World Data
When it comes to a Risk Based Threat Assessment, using real threat intelligence is a game-changer. Check out Appendix D of the 2024 Verizon Data Breach Investigations Report (DBIR) to enrich your risk analysis with actual breach data and trends.
Want to take it even further? Learn how to apply open-source data in your assessments with our guide on Threat Forecasting to Foresee Your Next Breach. It’s all about improving your ability to estimate likelihood and make informed, data-driven security decisions.

