2020 has been quite a year so far, surfacing security vulnerabilities many were unprepared for. Cyber attackers took advantage of new remote working environments as well as our fear and uncertainty due to COVID-19, and hit our networks hard. Just this year:
- 16 billion records were exposed, according to Cyber Risk Analytics
- 20,000 cyber security threats related to coronavirus (COVID-19) were reported to the Federal Bureau of Investigation’s (FBI) Internet Crime Complaint Center (IC3)
- Google noted a 350% increase in phishing websites, and its Threat Analysis Group blocked 18 million phishing and emails with the topic of COVID-19.
- Phishing, ransomware, remote working, and business email compromise (BEC) arose as the top COVID-19 cyber threats.
With expanded remote workforces, companies turned to additional solutions to accommodate their dispersed teams – but these solutions also brought security risks. We are seeing businesses:
- Are relying on more third-party applications, however, 35% of cyber security professionals indicate this could be one of their biggest security vulnerabilities. And 84% said they encountered problems just around enabling a remote workforce.
- Increasing adoption of multi-cloud environments, but in a TripWire survey, 84% of respondents indicated it was difficult to maintain security configurations across cloud services and cloud-related attacks rose 1,350% in some industries.
Our clients experienced a number of these pandemic cyber attacks which we helped remediate below:
EXFILTRATING REMOTE USER ACCOUNTS TO INJECT RANSOMWARE Adversaries utilized a phishing campaign to exfiltrate authentication credentials and corporate VPN settings from remote users. Incident led to the organization suffering a significant financial impact after negotiating a Bitcoin payment to recover their data.
WHEN RANSOMWARE HAS CAPTURED DATA … BUT WE DON’T KNOW WHAT THAT DATA IS Ransomware victims that have not categorized and inventoried sensitive data are paying high ransom fees just to begin the investigation phase of their breach response.
WHAT IS YOUR BUSINESS RESILIENCY OR ATTACK RECOVERY PLAN?
Compliance regulations such as The Gramm–Leach–Bliley Act (GLBA), PCI DSS Requirement 12.10, HIPAA Administrative Safeguards, The California Consumer Privacy Act (CCPA), Cybersecurity Maturity Model Certification (CMMC), and The Securities and Exchange Commission’s Office of Compliance Inspections and Examinations (OCIE) require companies should have an incident response plan (IRP) to detect and respond to cyber attacks.
Preparation makes for a more secure organization. An incident response plan (IRP) builds a stronger operation, as it mitigates significant disruption and cost to a business. Research indicates being proactive pays off:
- Only 39% of companies with an IRP had significant disruption due to a data breach versus 62% of those with less formalized plans.
- Companies with IRPs and teams in place spend approximately $1.2 million less than companies with no plans.
WHERE DO YOU START?
Developing a full incident response process that incorporates preparation, identification, containment, eradication, recovery, lessons learned can be overwhelming and time-consuming in our fast-paced digital world. It is time well-spent when having that comprehensive plan in place and implemented efficiently helps manage data breach costs in the future.
“Companies that contained a breach in less than 30 days saved over (US) $1 million vs. those that took more than 30 days to resolve.
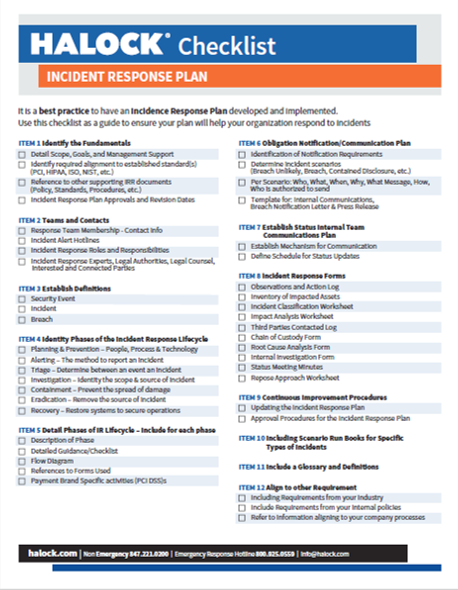
A best practice is to review your teams and resources to identify what you need for an IRP. Start by using this incident response plan checklist and contact us to ensure you build an IRP appropriate for your organization.
HALOCK recognized in 2024 Verizon Data Breach Investigations Report (DBIR) on how to estimate risk.
Estimate risk based on real threat data. Read Appendix D in the 2024 Verizon Data Breach Investigations Report (DBIR) to augment your risk analysis.