CIS Based Security Assessment
CIS Based Security Assessment
Comprehensive Evaluation of Your Security Posture
Understanding your security posture requires more than checking boxes. A CIS Based Security Assessment provides a comprehensive evaluation of your security architecture by combining best practices from the Center for Internet Security (CIS) Critical Security Controls with HALOCK’s threat‑based analysis methodology. This blended approach gives executive leadership a clear, prioritized view of vulnerabilities, exposures, and strategic recommendations to strengthen cyber defenses and reduce organizational risk.
What HALOCK’s Security Assessment Includes
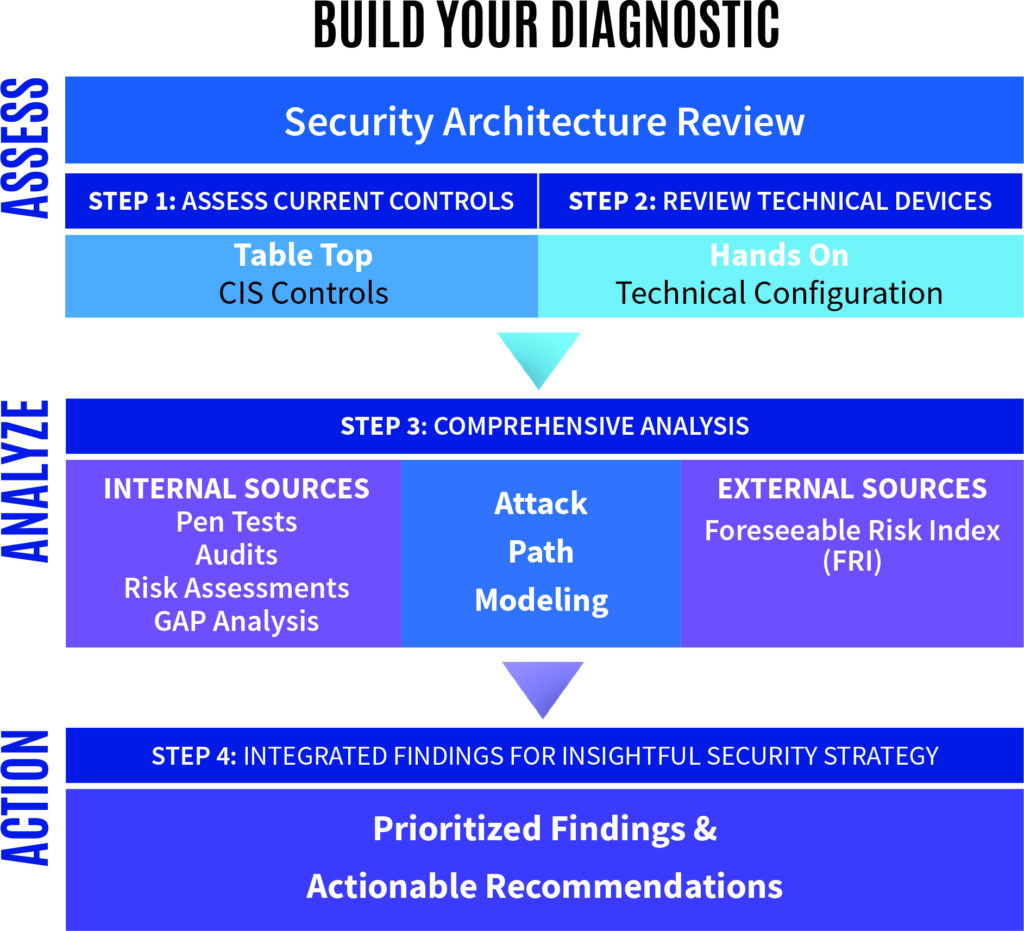
Our assessment begins with a thorough review of your current security architecture, which may include your network design, system configurations, cloud deployments, controls, and defensive mechanisms. We analyze your environment against the CIS Controls and leverage industry context and threat intelligence to understand how your defenses perform in real-world attack scenarios. Rather than just measuring maturity, we prioritize weaknesses based on how likely and impactful they would be if exploited.
As part of this evaluation, we consider existing documentation, configuration data, and discussions with key personnel to assess both technical and procedural controls. This combined review identifies systemic security issues that can reduce your resilience to threat actors before they lead to a breach. The assessment concludes with a detailed report outlining findings, prioritized remediation recommendations, and a roadmap to strengthen your security posture based on real risk insights.
Your CIS Based Security Assessment and report offers an Executive Summary, Details of Findings, and Attack Path Modeling to give you the full picture.
Security Architecture Review: Beyond the Firewall
A core component of this assessment is a security architecture review that identifies opportunities to improve your technical defenses. This non-disruptive study uses architecture diagrams, configuration data, and interviews to evaluate the effectiveness of your current security controls and infrastructure. It uncovers systemic issues in network segmentation, remote access, wireless security, control integrations, and more, providing actionable insights for remediation that go beyond simple device-level checks.
Why Choose HALOCK for Your Security Assessment
HALOCK combines decades of experience in security architecture, threat assessment, and risk management. Our team brings deep technical expertise together with strategic insights to help you prioritize improvements that align with business goals and risk tolerance. This assessment delivers defensible, business-focused reporting built for executive review, audit support, and continuous program maturity.
With our approach, you get an integrated view that helps evaluate your security architecture across technology, policy, and procedural layers, tie control gaps to real industry threats, prioritize recommendations based on risk impact, and build a roadmap that supports compliance, resilience, and informed decision-making.
Frequently Asked Questions about HALOCK’s CIS Based Security Assessment
What makes a CIS Based Security Assessment different from a traditional security audit?
A traditional audit often checks compliance against a static list of controls. A CIS Based Security Assessment goes further by evaluating how well your controls would defend against likely, real-world threats and prioritizes gaps based on risk to your business.
How long does an assessment take?
Timelines vary by environment complexity but typically range from several weeks to about a month from initial scoping through delivery of final reporting.
Will I receive remediation guidance?
Yes. The final report includes prioritized, actionable recommendations tied to business risk, helping your organization plan and justify improvements.
Can this assessment help with compliance goals?
Yes. While the assessment is designed for risk and resilience, many elements also map to compliance frameworks such as NIST, HIPAA, PCI DSS, and others, providing useful documentation for audit and regulatory purposes.