CIS RAM
Do you need assistance implementing CIS RAM at your organization?
We can help. Contact us to review your risk.
Learn about Reasonable Risk, the only GRC SOFTWARE PACKAGE ready for CIS RAM out of the box!
Download CIS RAM
The Center for Internet Security Risk Assessment Method
What Is CIS RAM?
CIS (Center for Internet Security®) and HALOCK Security Labs co-developed the CIS Risk Assessment Method (CIS RAM) to help organizations implement the CIS Controls in a reasonable manner.
Using CIS RAM, organizations can build reasonable and appropriate cyber security safeguards for their specific environments. This methodology helps define your acceptable risk level, achieve compliance and ensure your organization devotes the proper amount of resources to security.
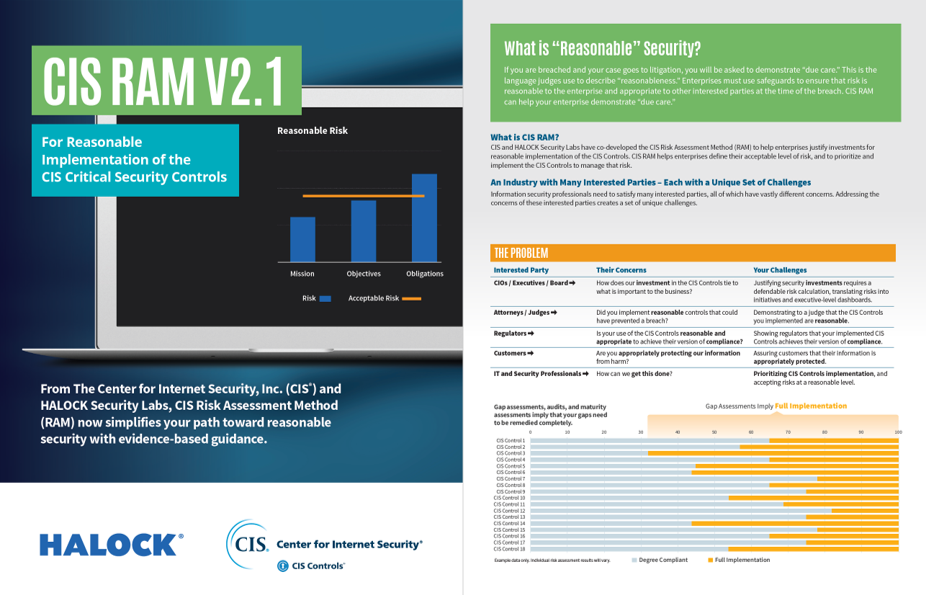
What Is ‘Reasonable Security’?
If your information is breached and your case goes to litigation, you will be asked to demonstrate “due care.” Organizations must use safeguards to ensure that risk is reasonable to the organization and appropriate to other interested parties at the time of the breach. For reasonable implementation of the CIS Controls, the CIS risk assessment method (RAM) helps your organization demonstrate the right level of due care.
Justification for CIS RAM
HALOCK and CIS designed CIS RAM to provide utility for both advanced practitioners and companies new to the assessment process. Experienced cyber security professionals can use CIS RAM to model threats against information assets and determine the ideal implementation of CIS controls. Organizations conducting initial risk analysis, meanwhile, can leverage CIS RAM’s instructions to model foreseeable threats and define actionable information security controls lists.
No matter your level of risk assessment experience, CIS RAM offers multiple benefits, including:
- Helps organizations prioritize and implement CIS controls reasonably.
- Provides a method to develop risk criteria that meet the standard of due care as expected by the appropriate authorities.
- Creates consensus among interested parties.
- Provides instructions, worksheets and exercises to guide you through your risk assessment; three different sets of materials support tiers of risk maturity found in the National Institute of Standards and Technology (NIST) Cybersecurity Framework.
- Integrates with the CIS Community Attack Model to model complex threats.
The Right Amount of Security
Risk analysis helps shape and customize controls to address the internal and external challenges that organizations face. Too often, organizations rely solely on gap assessments to determine the severity of their vulnerabilities, but remediating all gap assessment deficiencies can lead to over-securing and over-investing.
Effectively evaluating potential risk and your need for security controls is about finding balance. If assessments aren’t extensive enough, new deployments could fail to meet the standards of due care and reasonable security, putting your organization at risk of data breaches and potential legal action. If assessments are too extensive, you could spend substantial time and money safeguarding your network against incredibly unlikely security events. The result? Marginally improved defenses that may interfere with day-to-day operations and consume significant IT resources.
Using CIS RAM to evaluate and plan CIS Controls implementation provides a “just right” assessment of risks and potential safeguards, allowing your company to readily define its CIS information security controls list — the prioritized set of actions put into place to protect organizations and data from known cyber attacks.
Risk Assessment Done Right
Remediating the risks identified through a CIS RAM assessment results in the security you need for the investment you can afford. CIS RAM enables you to apply exactly the right amount of security — not too much, not too little — striking a balance between staying safe and ensuring your organization can conduct business as usual.
Partner with HALOCK to establish reasonable security controls based on your mission, objectives, and obligations. Manage your risk according to your specific business environment. Learn about our comprehensive approach to risk with our Risk Management Program.
What’s New in CIS RAM v2.1
- Workbooks automate much of your risk analysis for faster results.
- CIS RAM 2.1 estimates likelihood by comparing the commonality of reported threats to the strength of CIS Safeguards that prevent them.
- Using the Veris Community Database (VCDB), CIS RAM introduces an evidence-based heuristic for estimating likelihood.
Reasonable Security is Defined
The Sedona Conference – an influential think tank that advises attorneys, regulators, and judges on challenging technical matters – just released its Commentary on a Reasonable Security Test. The Commentary is the first document of its kind that provides the legal community with a clear definition of a “reasonable” security control.
HALOCK’s Chris Cronin was a co-author of Commentary on a Reasonable Security Test and CIS RAM. To learn how to apply the test, contact us.
HALOCK, a trusted risk management and cybersecurity consulting firm headquartered in Schaumburg, IL, near Chicago, advises clients on reasonable information security.


