How Healthy is Your HIPAA Security Risk?

HIPAA Is Evolving. Enforcement Is Increasing. Risk Is Expanding.
With anticipated updates to the HIPAA Security Rule, increased OCR enforcement activity, expanded third-party risk scrutiny, AI governance concerns, and the continued rise in ransomware targeting PHI, organizations must move beyond checklist compliance. Access HIPAA Resources to help manage your risk below: Cybersecurity Awareness Posters, HIPAA News, Breaches, Requirements, AI Risk, and more.
HALOCK helps covered entities, business associates, and PHI-handling organizations build defensible, risk-based HIPAA programs that withstand regulatory review and real-world cyber threats.
Preparing for Upcoming HIPAA Security Rule Enhancements
Regulatory signals indicate stronger expectations for:
- Continuous risk analysis
- Multi-factor authentication (MFA) and stronger technical safeguards
- Enhanced logging, monitoring, and incident response readiness
- Vendor risk documentation and oversight
- Encryption enforcement and cloud configuration validation
- Documented governance for emerging technologies, including AI
HALOCK’s services align directly to these evolving requirements and help you achieve both security and compliance.
HIPAA-Centered Services For Reasonable Security
Risk-Based Threat Assessment. Understand Your True Risk Exposure
HALOCK’s Risk-Based Threat Assessment methodology prioritizes threats based on likelihood and impact — not just vulnerability lists. This approach supports defensible HIPAA risk analysis documentation aligned with regulatory expectations.
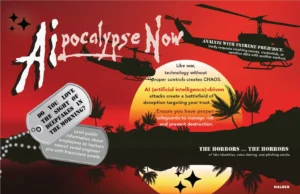
AI Risk & Governance for PHI Environments
As AI tools are integrated into healthcare operations, billing systems, analytics platforms, and patient engagement tools, HIPAA compliance must extend to algorithmic processing of PHI. Manage your AI risk with AI Risk Assessment, CoPilot Security Services, and CCPA Privacy Risk Services. HALOCK’s AI governance approach applies reasonable security principles and risk analysis discipline to AI deployments:
This helps organizations address:
- AI privacy and data exposure risk
- Model transparency and explainability
- Secure development and third-party AI vendor review
- Documentation suitable for regulatory scrutiny
Offensive Security & Penetration Testing
Regulators increasingly expect organizations to validate technical safeguards — not just assert them.
- External Network Pen Testing
- Internal Network | Internal Wireless Pen Testing
- Web Application Pen Testing
- Assumed Breach Pen Testing
- Adversary Simulation Pen Testing
- Red Team Pen Testing
- Remediation Validation Pen Testing
These services directly support HIPAA technical safeguard validation, vulnerability management improvement, and audit defensibility.
Incident Response & Breach Readiness
With strict breach notification timelines and growing ransomware severity, incident response preparedness is essential.
These services ensure:
- Rapid containment and forensic investigation
- Clear documentation for OCR reporting
- Executive and board-level readiness
- Tabletop exercises aligned with HIPAA breach requirements
Cloud Security for HIPAA-Regulated Environments
Cloud adoption does not reduce compliance obligations; it expands configuration risk and shared-responsibility complexity. HALOCK’s Cloud Security Assessment evaluates access controls, encryption posture, logging and monitoring, architecture risk, and alignment with HIPAA safeguards.
External Attack Surface Management (EASM). You cannot secure what you cannot see.
HALOCK’s External Attack Surface Management identifies internet-facing assets, shadow IT, exposed services, and exploitable vulnerabilities:
EASM supports continuous risk monitoring — a growing expectation under HIPAA enforcement trends.
Why HALOCK for HIPAA?
- Healthcare-focused expertise
- Risk-based methodology (not checkbox audits)
- Technical validation plus governance alignment
- Board-ready reporting and documentation
- Support for covered entities AND business associates
HALOCK bridges compliance and cybersecurity — ensuring your HIPAA program is both defensible and operationally effective.
Protect PHI. Reduce Risk. Strengthen Compliance.
Schedule a consultation with HALOCK today and build a HIPAA program prepared for evolving regulations and modern threats.
What HIPAA and Cybersecurity Resources Can You Provide?
- HIPAA and Healthcare Articles, Overviews, on the industry developments, breaches, regulations, and news.
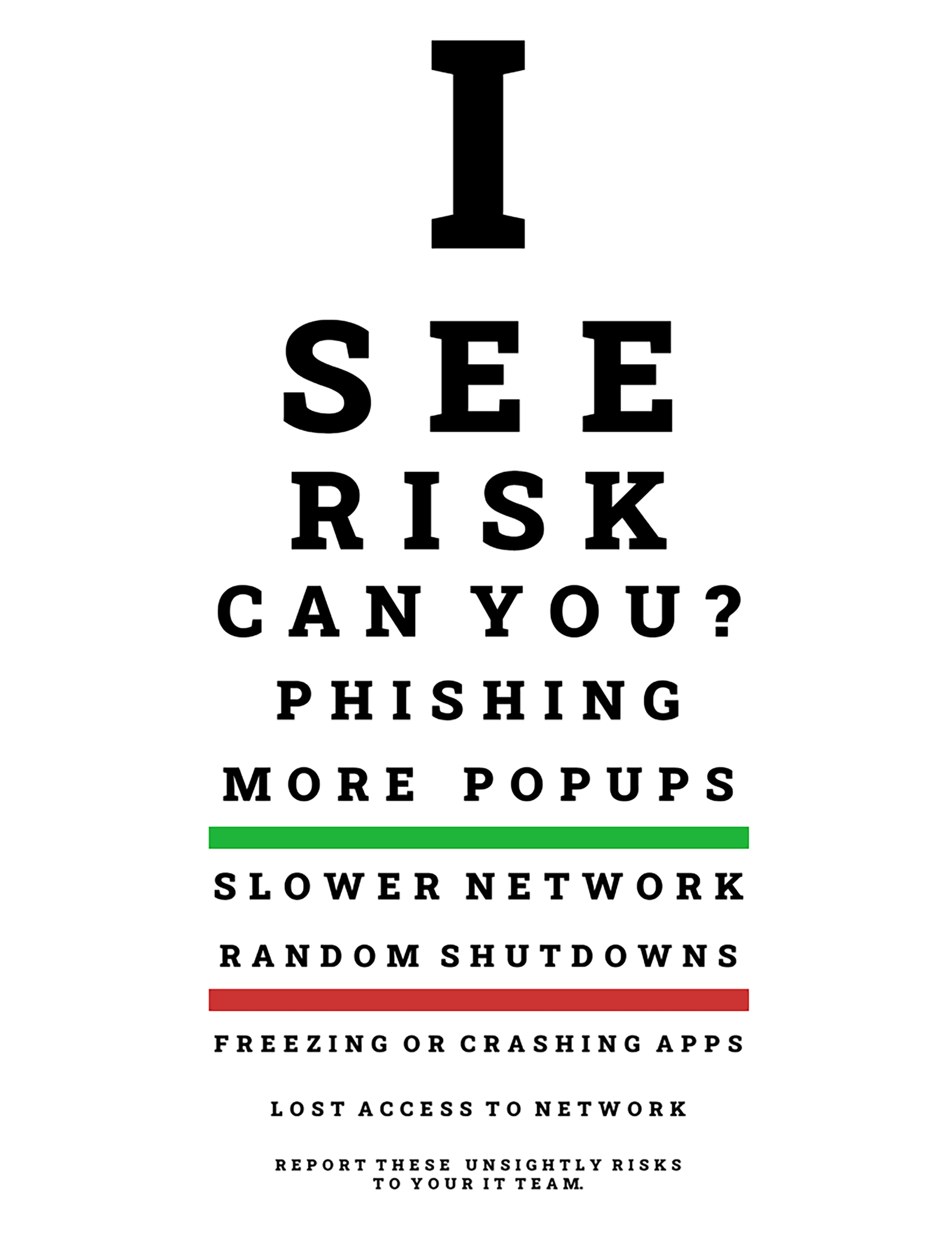
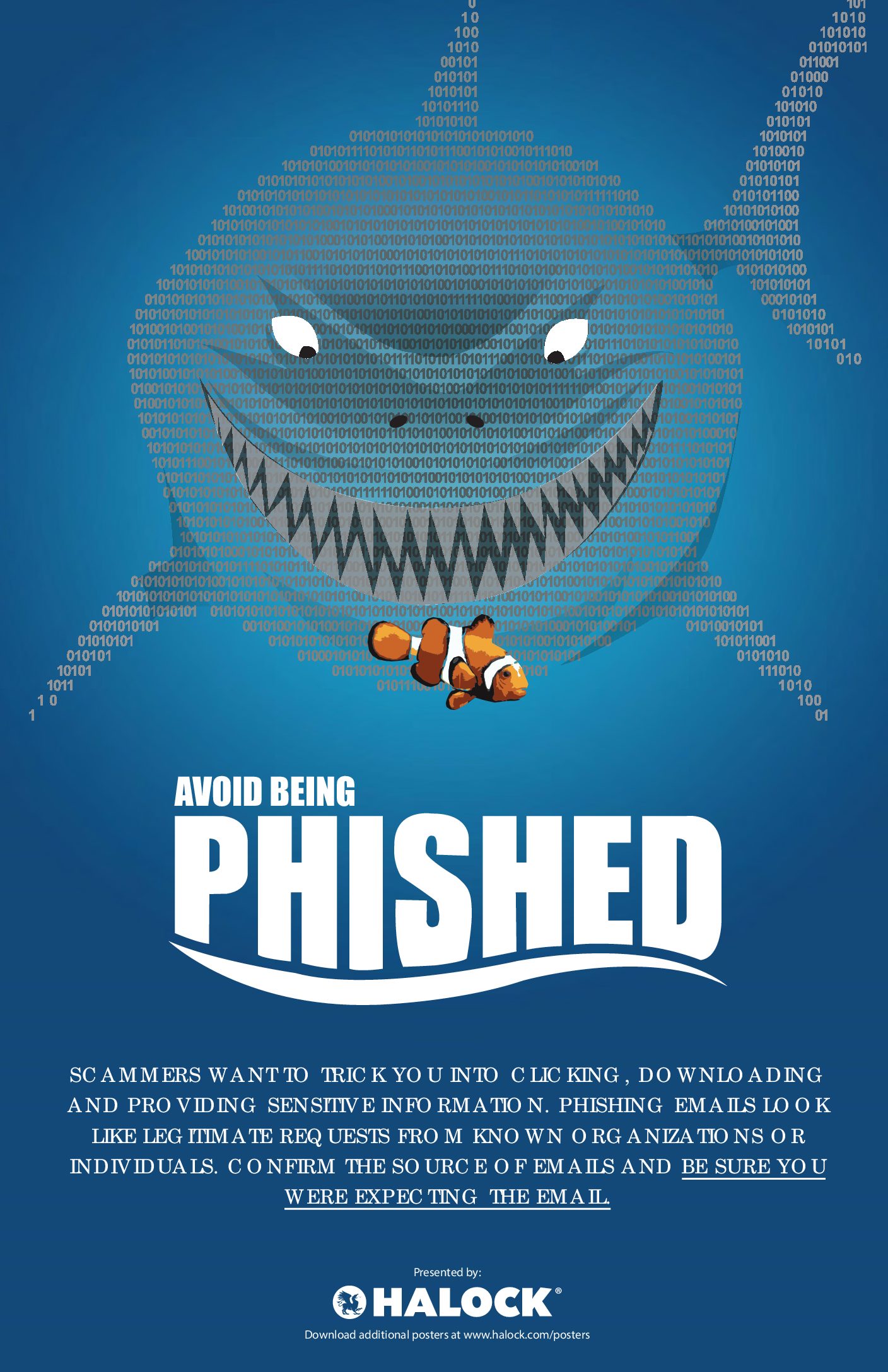
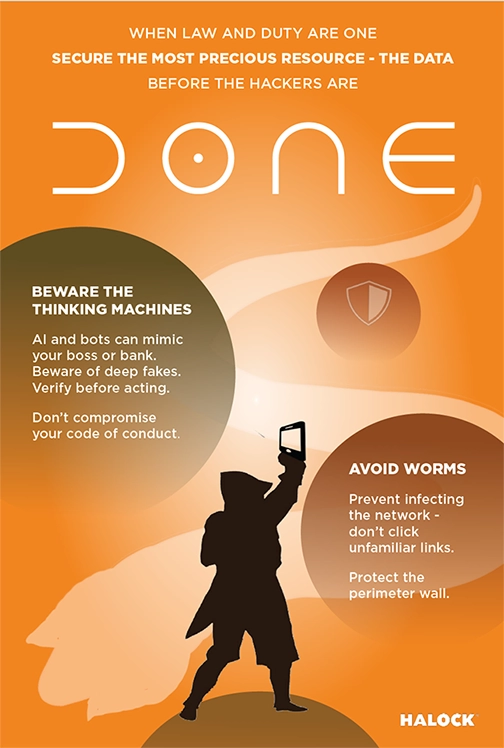
- Cybersecurity Awareness Posters to remind your office of security risks and protocols.
- Request a Security Briefing. What is a HALOCK Security Briefing? The HALOCK Security Briefing helps to advise and keep security leaders informed with as little impact as possible to their schedule. The Briefing is a review of significant events, trends, and movements that will influence how you manage cybersecurity, risk, and compliance. These editions will highlight both recent and past news so you keep pace with – and ahead of – changes in your field. Security Leadership, Internal Counsel, Operations, Compliance, Security Operations, and Business Leadership can all find useful insights from the security briefs.
Two More HIPAA Security Rules You Can No Longer Ignore
HALOCK is headquartered in Schaumburg, IL, in the Chicago area, and advises clients on risk management and reasonable security programs throughout the US.
And more cybersecurity awareness posters as a fun reminder to keep alert.