A common occurrence when discussing security of the cloud with our clients is confusion over what type of security assessment is needed to determine what potential risks and deficiencies are present with their deployed cloud environments. Platforms like AWS, Azure, and Google have different default and available security controls that are in place and configured, which often lead to unintended security gaps. Oftentimes, they are discussed as interchangeable, but in reality have fundamentally different objectives.
In this article, we will answer these questions.
- What are the objectives of a penetration test?
- What are the objectives of a cloud assessment?
- Are both needed for security visibility and vulnerability identification?
Penetration Testing
This is an adversarial simulation that is executed in a controlled manner to identify and exploit vulnerabilities that are present in systems, applications, and infrastructure.
The characteristics of a Penetration Test are:
- Testing focuses on exploits, what can an attacker see and do?
- Time-boxed assessments to keep the costs of execution lower
- Often scoped to specific systems, networks, and applications
- Demonstration of potential impact if exploited, with the evidence to support
The Limitations of a Penetration Test are:
- They are typically a snapshot in time, executed annually
- Limited visibility into how the cloud environment is designed and how it is managed
- May miss misconfigurations that cannot be exploited during the test
- Does not identify if security controls are implemented correctly
The objective of penetration testing is to confirm real-world vulnerabilities that can be exploited.
Cloud Assessments
These are comprehensive evaluations of how the environment is designed, configured, managed, and operated using published security best practices as the evaluation criteria.
The Characteristics of a Cloud Assessment are:
- Focuses on architecture as deployed and the controls that are in place
- It is focused on configuration vs. exploitability
- Maps to frameworks such as CIS Benchmarks and uses best practices, such as Azure and AWS published best practices for the evaluation
- Demonstration of potential impact if exploited with the evidence to support
- Digs into preventive and detective capabilities for the deployed environment
- Is typically not limited in scope, and evaluations are meant to be more frequent or continuous
- Created a baseline of normal behavior and highlighted areas such as overprivileged access, dormant account usage, and abnormal access
- Correlates different findings to communicate potentially toxic combinations. Example: A virtual system that has RDP access enabled, unrestricted access from the internet, and does not use multifactor authentication (MFA).
The Limitations of a Cloud Assessment are:
- Does not prove that the identified vulnerabilities are exploitable
- May appear as more theoretical to some target audiences
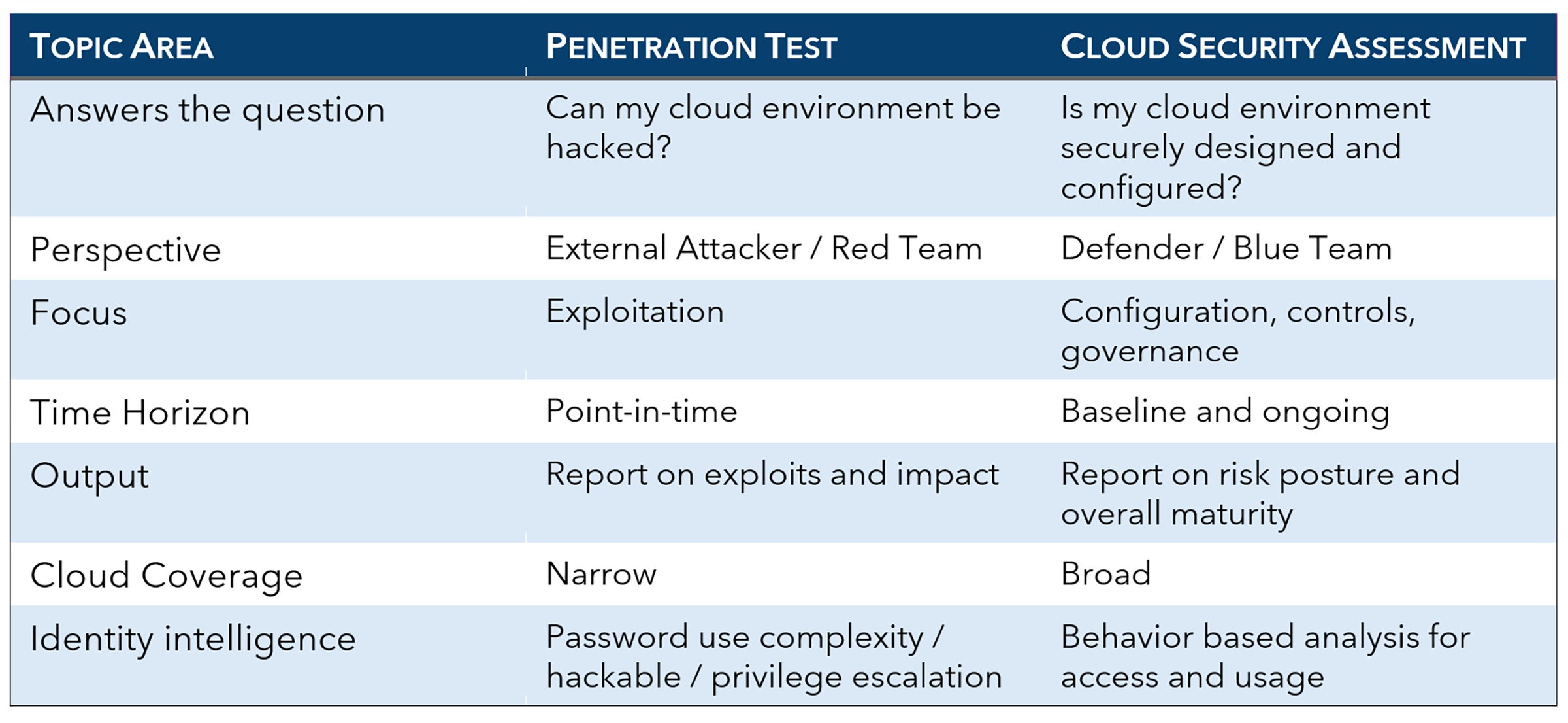
Key Differences – Comparison Matrix
A penetration test is not enough. Many high risks arise from misconfiguration rather than software vulnerabilities. Some examples are
- Over-privileged IAM roles
- Excessive API permissions
- Inadequate network segmentation
- Disabled or incomplete logging
- Misconfigured storage access controls
These risks may be missed during a shorter-term engagement but can materialize over an extended duration.
A cloud assessment is not enough. Multiple risks may be identified, but does not answer the question “What can an attacker do with the findings?” Without evidence of exploitability
- Risk prioritization may become subjective
- The business impact is harder to communicate
- Security teams may struggle to gain remediation buy-in
Better Together
When combined, penetration testing and cloud security assessments create a defensible, complementary security validation model
In cloud environments, security is not a single activity—it is a lifecycle. Penetration testing and cloud security assessments serve distinct but complementary roles within that lifecycle. Organizations that rely on only one are left with blind spots that attackers are increasingly adept at exploiting.
Effective cloud risk management requires both architectural assurance and adversarial validation.
LIMITED OFFER
To help support the journey to better cloud visibility and security, HALOCK is offering a 20% discount on a penetration test or cloud assessment when bundled.
Additionally, HALOCK offers External Attack Surface Management (EASM) assessments that are essential to a holistic Continuous Threat Exposure Management (CTEM) program, like cloud assessments and penetration tests. EASM was created to marry asset risk with exploitable vulnerability findings to assist with prioritizing remediations on a regular cadence with no limitations of scope and no time boxing.
Where are you on your CTEM journey? HALOCK would love to talk with you about it.
READ: Cloud Security Insights
Review Your Risk and Security Posture