You can feel it, can’t you? There’s a structural change happening in cybersecurity.
At the moment adversaries started using AI to speed reconnaissance, automate exploitation paths, the excuse-ridden reactive security model had no chance. The security world didn’t request it. No standards body pushed it. The reality is that AI must be a big part of the solution.
Preemptive Cyber Defense as a model is a logical step. It’s not about new techniques; rather, it’s about harnessing the speed of AI to operationalize the fundamentals that have always mattered. Patch, validate, verify, maintain lifecycle, reduce exposure, and break attack paths before they manifest. The fundamentals weren’t wrong. They were just not achievable.
AI (artificial intelligence) changes that proposition.
Preemptive Cyber Defense is an emerging model that advocates preventative measures through continuous exposure management and acting earlier in the kill chain. These measures begin to shift the focus from Detect and Respond to Identify and Protect, building upon established concepts from Zero Trust Architecture philosophy. This is not a future idea. It is a strategy built on what works, empowered with the speed and capability of agentic AI and machine learning.
The benefits machine learning provides to email filtering, endpoint protection, and identity can’t be denied, but while they reduced the noise, they didn’t change our strategy. Most teams are still operating in reactive mode, waiting for an event to occur before they act. The results are similar from company to company. Backlogs continue growing. SOC queues are nowhere near zero. Service desk tickets continue to age. Change requests contending for a window. Vulnerability lists grow so fast that organizations focus on the “criticals”. This isn’t failure. These are indicators of a system producing risk at a rate unmanageable by humans.
The reactive model leaning on Detect, Respond, and Recover is outdated given the tools available to threat actors, and the model needs to adapt in order to overcome. It was not designed for an adversary that can model and execute attack paths at machine speed. The offensive capability of the game has changed, and the defense needs to evolve to meet the threat.
Offensive Capabilities Levelled Up
For the adversaries, the adoption of AI was almost immediate. They are using AI to handle reconnaissance, identify exploitable paths, and chain vulnerabilities into plausible exploits in seconds. Practices that used to take hours, days, or even weeks are now being produced by agents, giving attackers speed, accuracy, and iteration capabilities that existing Detect and Respond processes were never designed to absorb.
Using AI, attackers are automating reconnaissance, chaining vulnerabilities, creating dynamic payloads, and launching phishing websites from a prompt. The attackers are operating intelligently at machine speed.
AI Adoption is at Mass Scale
It is hard to remember a technology that has been as rapidly adopted as AI (artificial intelligence). About half of all adults internationally are already using AI tools intentionally daily. This surprising rate of adoption propels operational functions forward at a rate human-based governance, security, and IT operations processes cannot match. Attackers aren’t just faster. Everything is faster.
A Shift From the Reactive Model to Preemptive Practices
The truth is out there. Security leaders know the reactive model is breaking down. Not because teams lack skill or effort. Rather, it’s down to the fact that the modern enterprise moves at a rate that human-based workflows can no longer absorb. The system outpaced the people responsible for it a long time ago, and AI has compounded the issue.
Signs that the Detect and Respond model is not working:
- Growing Backlogs.
- Aging service desk tickets.
- Mean time to address known vulnerabilities is only focused on the “critical”.
- Change requests wait for maintenance windows that never come.
This is the natural entropy of a system that moves faster than the supporting and defending mechanisms. Standard process improvement cannot change reality. The volume of work exceeds the capacity of the teams doing it. The backlogs are not a sign of failure. They are an indicator of a system producing risk at a rate unmanageable by humans.
Machine learning improved email filtering, endpoint detection, and identity analytics. It helped to reduce some of the noise, and it made signals cleaner. Though it never changed the underlying security model. Teams still wait for an event before they act (Detect and Respond). And hope to avoid a painful recovery. Machine learning reduced some alert fatigue, but it didn’t change the fact that humans sit at the center of processes that do not fit the pace of modern operations. They need help.
Fundamentals Fail Under a High Rate of Change
Cybersecurity hygiene best practices are known and take center stage. The fundamentals haven’t changed.
- Patch consistently
- Stay on the current supported versions
- Manage identities and their lifecycles like they were accessed through your perimeter firewall.
- Continuously validate controls.
- Retire systems and services when no longer needed.
- Remove policy, process, and configuration drift.
- Identify vulnerabilities and exposures early to reduce the opportunity for compromise.
Knowledge usually isn’t the problem. Every security team knows what to do for the most part. The failure occurs because today’s environments move faster than human-directed workflows can put and keep the fundamentals in place. Services are ephemeral. Cloud services shift by the minute. Identities expand without technical guardrails. Policies drift. Attack surfaces grow faster than teams can document them.
It isn’t a maturity or a staffing issue. Even the well-resourced teams are unable to continuously execute fundamentals across thousands of systems and identities that can change by the minute. The problem is velocity, volume, and coordination. The environment moves faster than human processes can react to.
Cybersecurity is beginning to look like flying a stealth aircraft. On paper, the pilot is in control. In reality, though, the plane is unstable, and no human can make the micro-corrections fast enough to keep it in the air. The flight control system does the work, making thousands of corrections per second while the pilot makes decisions and sets intent. Cybersecurity and IT Operations are the same now. The environment is too dynamic, too fast, and too unstable for humans to “fly” manually. AI must become the control system that keeps everything stable so teams can focus on their objectives instead of keeping the plane in the air.
That’s why Preemptive Cyber Defense requires AI. The velocity problem can’t be solved with more people, dashboards, meetings, or compliance cycles. The only way to run fundamentals continuously is with something that operates at the speed of the adversary.
What Preemptive Cyber Defense Means
Preemptive Cyber Defense is the continuous execution of the fundamentals that reduce risk before an attacker can use it. It keeps systems current, identities clean, controls working, configurations aligned, and exposures closed off. The fundamentals aren’t new. What’s new is the need to run them continuously. AI makes that possible by operating at the same speed the environment now moves, and at the same speed adversaries already operate.
The Six Pillars of Preemptive Cyber Defense
It’s rare because teams don’t know the fundamentals that programs break down. It’s because modern systems change faster than human-directed workflows can manage. Preemptive Cyber Defense doesn’t replace, rename, or change the fundamentals; it gives the organization a way to execute them continuously, with AI handling the tasks at the speed and scale humans cannot.
Below are the six pillars that define what preemptive security looks like in practice, and how each aligns with NIST CSF 2.0.
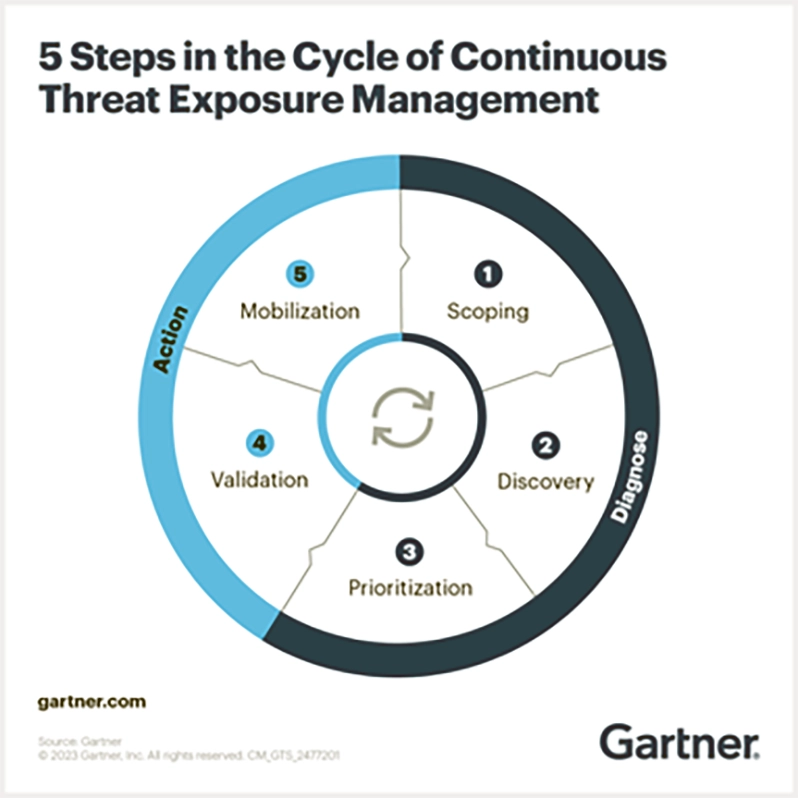
The Six Pillars themselves are a new structure first defined and presented here, but the ideas underneath are not new. They stem from what the industry has been signaling for years. The themes are evident through NIST CSF 2.0, CISA’s secure-by-design guidance, DORA mandates, Google’s work on preemptive cyber defense, Gartner’s CTEM (Continuous Threat Exposure Management) research, and practical insights from Veriti, Deepwatch, Ionix, and others who have been pushing security towards continued practices. What we’ve done is organize these long-standing fundamentals into a model that fits the speed of modern environments and the reality of AI on both sides of the fight.
1. Proactive Disruption of the Kill Chain
NIST CSF: Protect & Detect – Attack Path Analysis, Threat Modeling, Defensive Architecture
Proactive disruption of the kill chain is the primary objective of Preemptive Cyber Defense. At least for now, even when using AI, attackers still follow the steps: reconnaissance, access, escalation, movement, and impact.
Proactive disruption removes opportunities before attackers can use them, disrupting these patterns.
This aligns with Advanced Cyber Deception (ACD), Automated Moving Target Defense (AMTD), and Predictive Threat Intelligence (PTI), which all focus on disrupting attackers before a meaningful impact occurs.
Action:
Leverage AI and Machine Learning to identify and collapse potential attack paths by eliminating exploitable situations (configurations, vulnerability chains, static gateways) before reconnaissance can to turn to weaponization.
2. Lifecycle and Attack Surface Management
NIST CSF: Identify & Protect – Technology Lifecycle, Vulnerability Management
Zero days are required by attackers when the average environment is full of old operating systems, expired certificates, outdated libraries, forgotten/ghost cloud resources, and unmonitored endpoints. Lifecycle management has always been fundamentally essential, and it is impossible to scale with manual processes.
Preemptive defense means detecting outdated systems, aging components, software vulnerabilities, unsupported and vulnerable dependencies, and addressing them before they fail or become entry points for attackers.
This pillar connects with Gartner’s research on Automate Exposure Management and Predictive Threat Intelligence (PTI). PTI helps forecast which lifecycle weaknesses are likely to be targeted based on emerging attacker trends, and automate exposure management handles the continuous visibility, and ideally, remediation.
Action:
AI can help unwrap the compatibility onion while monitoring and prioritizing unsupported hardware and software, vulnerable libraries and packages, and ensuring that remediation focuses on changes that reduce the attack surface in a meaningful way.
3. Continuous Exposure Awareness
NIST CSF: Identify – Asset Management, Risk Assessment, Visibility
Continuous Exposure Awareness requires understanding of the environment, including the ephemeral, at all times. What exists, what changed, what’s exposed, and where is risk aggregating?
Today, organizations, for the most part, still rely on periodic inventory and vulnerability scans. They run annual asset impairment tests and maybe quarterly asset discovery. A “mature” organization likely has monthly risk reviews and occasional cloud posture assessments. Yet, attackers run automated tools and AI agents that can discover exposure in seconds.
Google’s work on Preemptive Cyber Defense emphasizes this point. Defenders need real-time visibility because attackers already have it.
AI facilitates this by identifying new assets, configuration drift, changes in permissions, and external exposures.
This pillar aligns with Gartner’s Automated Exposure Management and CTEM categories, focusing on continuous asset discovery, attack-surface monitoring, and risk prioritization. Exposure visibility can no longer be periodic.
Action:
Build an AI-enabled continuous discovery across your organization’s physical and digital footprint. Know what exists, what changed, and what’s exposed in real time, not when it’s been manually put in or taken out of production, or worse, on quarterly review.
4. Continuous Control and Configuration Validation
NIST CSF: Protect – Identity Management, Access Control, Governance
Controls usually fail quietly. Logging breaks. Agents don’t get applied in server builds. Endpoint agents fall offline. DLP policies get overwritten and reset to the default. Usually, these broken process components are only identified when an incident occurs.
The model flips with continuous validation. The environment contacts, checks, and alerts when something drifts, breaks, or is misconfigured, instead of assuming controls are working.
This pillar aligns with Automated Moving Target Defense (AMTD) and continuous configuration monitoring practices highlighted by Gartner and CISA’s secure-by-design guidance. AMTD evolved from the understanding that defenses must be dynamic and continuously validated.
Action:
Utilize CNAPP and other tools to automate validation of configuration and related controls at all times, especially upon change. Instrumentalize telemetry from tools to create complete situational awareness of configuration drift and associated risk.
5. Identity and Privilege Hygiene
NIST CSF: Protect – Identity Management, Access Control, Governance
Identity drift happens quickly. Temporary access lingers. Roles expand. Privileged accounts stack up. Service accounts multiply like rabbits without owners. Certificate lifecycle management is neglected.
Identity and privilege hygiene requires continuously maintaining access rights, roles, and entitlements in alignment with least privilege. Not during an audit or once per quarter.
IAM (Identity Access Management) Governance and CIEM (Cloud Infrastructure Entitlement Management) solution categories line up with this pillar. These solutions exist because the identity management challenges are now one of the largest cyber risk drivers. Identity is no longer the new perimeter. It’s just the perimeter.
Action:
By using AI, continuously review, evaluate, and correct application entitlements, privileges, and alert on drift to enforce least privilege access, and detect misuse from human and non-human identities.
6. Automated Security Posture Shaping and Drift Correction
NIST CSF: Protect – Configuration Management, Continuous Compliance, Policy Enforcement
Very little stays “correctly” configured for long. Cloud settings drift, identity rules get overwritten, endpoint coverage lacks completeness, and service configurations linger as systems evolve.
Automated Security Posture Shaping continuously adjusts the environment toward the intended secure state with small, frequent adjustments that prevent major issues.
Drift Correction detects deviations as they occur and fixes them before they can be exploited.
This pillar aligns with Gartner’s AMTD and continuous configuration monitoring. AMTD assumes a static environment invites exploitation by allowing reconnaissance to create actionable intelligence. Automated Security Posture Shaping is constantly changing the attack surface and applying compensating controls where required.
Action:
Keep the environment aligned with the intended state and close the exposures quickly with automated detection and correction of configuration drift across cloud, infrastructure, and identity platforms. Require exceptions with expiration dates to prevent automatic drift correction.
AI Operationalizes and Coordinates Preemptive Cyber Defense
AI is the only mechanism capable of turning the episodic reactive defense systems into continuous preemptive cyber defense programs. It takes on the tasks that happen too fast, too often, and at too great a scale for human workflows, closing the potential gaps between change and control at the speed of business.
Now AI doesn’t just execute tasks. It coordinates them as well to meet the objectives set by human managers and leadership. In today’s environments, identity, configuration, lifecycle, exposure, and behavioral data all influence each other. AI can see relationships and act on them in ways no single team or tool can.
AI enables continuous awareness across the environment, validates controls at the speed systems drift, maintains identity and privilege hygiene across the ecosystem, manages lifecycle and attack surface issues proactively, continuously shapes posture and corrects drift, and disrupts attack paths before they form.
AI becomes the coordinating fabric of operations, including Detect, Respond, and Recover. Even as Preemptive Cyber Defense shifts the emphasis to Identify and Protect, the traditional Detect, Respond, and Recover functions still matter. AI enhances those, too:
- Detect: Machine Learning and AI filter noise, correlate weak signals, and identify patterns humans would likely miss.
- Respond: recommends or takes containment actions, orchestrates response playbooks, and provides instant context.
- Recover: AI assesses impact, validates the restored states, and confirms operations and security posture after remediation.
This doesn’t manifest as a separate AI governance layer with meetings, approvals, and checklists. This is operational governance at machine speed. The intelligence that continuously coordinates actions across the environment keeps the fundamentals in place and ensures the defensive system behaves as a unit.
Our digital infrastructure is inherently unstable and constantly shifting. AI becomes the stabilizing force, like flight controls in a stealth aircraft, while humans set direction and make management decisions.
Conclusion
Artificial intelligence is changing how things actually get done across every part of the organization. About half of the people are using AI, including leadership, with or without organizational guidance or controls. Like smartphones and the internet in the past, AI has made its way into day-to-day processes and decision-making, before formal policy can catch up.
In cybersecurity, there’s a similarly rapid adoption of AI happening on the offensive side. AI-enabled attackers move at rates that effectively incapacitate the existing detection and response capabilities of most organizations. In some cases, a route to compromise can be determined and executed in seconds by adversarial agents.
AI changes that proposition.
Not by replacing people, but by handling the parts of information security and governance that break when humans try to do them manually. AI finally makes the fundamentals executable by implementing the real-time checks, the continuous hygiene, the drift detection, the exposure awareness, and the adjustments that no team could perform at scale. Humans set intent, strategy, and direction.
The shift is underway, and security leaders aren’t choosing between reactive and preemptive models. The real decision is simpler with much greater consequences: Do you redesign your program around execution enabled by AI, or do you continue relying on human-centered workflows built for 2010? One path matches the speed of the adversary. The other leaves the team waving at fireflies with wiffle ball bats.
Review Your Risk and Security Posture