Blog
Insights for Reasonable Cyber Security and Compliance
What’s happening in the world of cybersecurity? How do you define 'reasonable' security controls? Which cyber threats can be prevented? What steps should you take to make your systems safer? Read our blog posts to gain new insights into cybersecurity news, security awareness, the latest threats and risks, penetration testing, compliance, regulations and so much more.
Your Employees are Targets. Social Engineering is Increasing.
Even with advanced technology and security, your data is still at risk. Studies indicate that hackers are focusing on your teams to gain access to your networks and information. Social engineering is on the rise. This is a method of manipulating your teams into performing actions in order for an unauthorized person to get access to your systems and data. (more…)

Data Breach Litigation: Prepare for the Worst Case Scenario
Prepare for the worst – These words of wisdom are apropos in most aspects of life, especially when it comes to cyber security matters for your organization. (more…)

HALOCK Heroes Step Up for Kids
HALOCK supporting the compassionate work of Lurie Children’s Hospital.

HALOCK Annual Outing at Arlington Park
HALOCK celebrates over 20 years as an information security firm at the annual outing at Arlington Park. This year is quite special, as HALOCK co-developed with CIS® (Center for Internet Security), (more…)
SecureXII – 12th Annual ISSA and ISACA Chicago Chapters Security Conference and Networking Cruise
The 12th Annual ISSA and ISACA Chicago Chapters Security Conference and Networking Cruise – HALOCK was a proud attendee and sponsor at the educational and networking event. It was wonderful to connect with infosec leaders in the Chicagoland area. We hope to meet more in future events. (more…)

Cyber Security Summit: Chicago
HALOCK is proud to be a speaker at the Cyber Security Summit in Chicago on August 29, 2018. This educational and informational forum will focus on educating attendees on how to best protect highly vulnerable business applications and critical infrastructure.

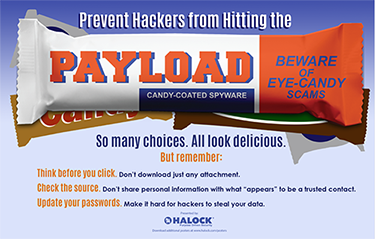
Infosec Poster: Payload
Prevent hackers from hitting the PAYLOAD with these cyber security awareness tips.
NetDiligence® Cyber Risk Summit: Getting to Reasonable Security
HALOCK partner Chris Cronin will be moderating a NetDiligence® Cyber Risk Summit panel on reasonable security. The panel includes industry experts on risk based analysis process and legal, regulatory and security best practices. Attend the event to learn how to best establish ‘duty of care’ for cybersecurity. (more…)
CIS RAM (Risk Assessment Method) Launch & Webinar
CIS RAM (Center for Internet Security® Risk Assessment Method) is an information security risk assessment method that helps organizations implement and assess their security posture against the CIS Controls™ cybersecurity best practices. CIS RAM, a free tool, provides step-by-step instructions, examples, templates, and exercises for conducting a cyber risk assessment. (more…)

4 Important Steps to Take When Creating an Incident Response Plan
By Erik Leach, CISSP, SCF
Imagine coming home and finding your house broken into and some of your belongings missing. As you totter from room to room, you would probably feel anger, frustrated, disturbed and a little overwhelmed. At a vulnerable moment such as that, it probably would not be the best time to engage in critical decision making that would most likely prove reactionary. This analogy can be applied to the instance of a data breach. (more…)
