Blog
Insights for Reasonable Cyber Security and Compliance
What’s happening in the world of cybersecurity? How do you define 'reasonable' security controls? Which cyber threats can be prevented? What steps should you take to make your systems safer? Read our blog posts to gain new insights into cybersecurity news, security awareness, the latest threats and risks, penetration testing, compliance, regulations and so much more.
CIS Controls 7 CIS RAM
CIS RAM (Center for Internet Security® Risk Assessment Method) was developed by HALOCK Security Labs in partnership with CIS. HALOCK had been providing CIS RAM methods for several years with a positive response from legal authorities, regulators, attorneys, business executives, and technical leaders. (more…)

We Just Gave Away Our Cyber Security Intellectual Property. It was the right thing to do.
Why a Chicago-Based Cyber Security Firm Just Released its Prized IP.
By Chris Cronin, ISO 27001 Auditor, Partner (more…)

HALOCK Supports Women’s Career Growth at WiCyS
Viviana Wesley, Managing Consultant at HALOCK, is used to being one of few women specializing in cyber security. But last week, for a change, she wasn’t alone. At the Women in Cybersecurity (WiCyS) Conference in Chicago, she was one of nearly a thousand participants from industry, academia, and areas of research who gathered for the organization’s fifth annual conference, designed to recruit, advance and retain women in that field. (more…)
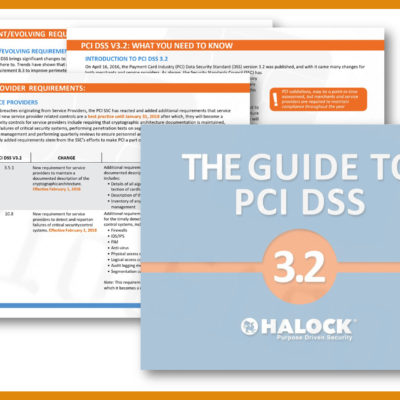
PCI Deadline is Fast Approaching on June 30, 2018
by Viviana Wesley PCI QSA, ISO 27001 Auditor – Managing Consultant, Governance & Compliance Services
Cyber security is a moving target. The technology and policies that kept users, devices and data safe at one time are eventually compromised at some point by the growing skills of cyber criminals and technology itself. This is one of the reasons security standards such as PCI DSS (Payment Card Industry Data Security Standard) are moving targets as well. Things never remain stationary in a world that is digitally transforming itself and security standards would not be relevant unless they dynamically changed along with the world. (more…)

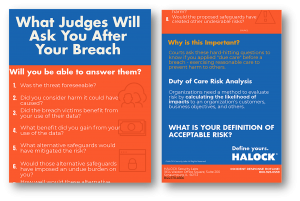
HALOCK Information Security Tip Posters
Download cyber security awareness tip posters for your office. Friendly reminders to your team and office of your security policies and procedures to keep your network safe.
What are Smishing Attacks and why are they Increasing?

Two things are inherently true when it comes to cyber criminals. The first is that they follow the money. This is why ransomware grew to a billion dollar business overnight. The second is that like water, their efforts flow towards the path of least resistance. Cyber criminals are like many people, they go for the easy money. Phishing has been the dominant delivery method for malware and cyber attacks for a number of years now. However, phishing is not as easy as it used to be. Spam filters and email gateways now react quickly in shutting down a malicious email domain. Email security technology is now using analytics to more accurately identify behavior abnormalities and possible email threats. Even users are growing more guarded when opening emails and are becoming more astute at identifying suspicious links and attachments. We have a long way to go of course, but it is getting better. (more…)

Women in Cybersecurity Conference – WiCyS 2018
The Women in Cybersecurity Conference (WiCyS) will be held in Chicago on March 23-24 and HALOCK is a proud sponsor of this important event. WiCyS is a community in which women in the cyber security field can engage, encourage and support one another in order to empower not only themselves, but also the cyber security industry at large. WiCyS was established in 2013 with the support from a grant from the National Science Foundation. (more…)