According to a survey conducted by the Ponemon Institute in 2018, 59 percent of companies have experienced a third-party breach of some type. Despite the high prevalence of these incidents however, only 16 percent say they effectively mitigate third-party risks. A separate healthcare cyber security report showed that about 56 percent of provider organizations have experienced a vendor or third-party breach. Some of the most publicized breaches in the past five years such as Home Depot and Target were attributed to third-parties. Some of the more recent third-party initiated breaches have included the Humana Health Insurance Company and retail giants Saks Fifth Avenue and Lord & Taylor. Considering the frequency of third-party attacks, it should be no surprise that 94.3 percent of executives had low to moderate confidence in their third-party risk management (TPRM) tools and technology according to a 2016 Deloitte Global survey.
Your Third-Party Vendor is an Extension of Your Own Organization
Thanks to the cloud and global communications, it is nearly impossible to find a company that doesn’t engage some sort of third-party vendor or supplier. Often times, these external vendors share some type of connection with their customers’ networks. It may be through cloud applications, secure file transfer sites, or VPN as examples. Once a third-party vendor is connected with your organization, your security and privacy compliance is only as strong as the vendor’s own privacy and security practices. This means that despite your own best efforts to attain best security practices and due care, your security is only as resilient as your weakest link.
New Compliancy Regulations Apply to Third-Party Vendors
More than just hackers are aware of the vulnerabilities that third-party vendors. Regulators are as well, which is why the recent wave of compliance regulations introduced by government legislators treats third-party vendors as an extension of your own domain. Europe’s GDPR specifically states that any third-party involved in the processing of personal data is legally obligated to comply with all aspects of GDPR. The recent California Consumer Privacy Act (CCPA) covers third-party vendors that qualify as “service providers” and requires companies that deal with the personal information of California residents to monitor the compliance of qualifying vendors. This focus on third-party vendors isn’t a recent phenomenon however. Even back in 2010, Massachusetts passed an Information Security law that not only required businesses to secure their networks but made them responsible for ensuring the security and compliance of their vendors, suppliers, and contractors.
Scrutinize and Review Your Vendors
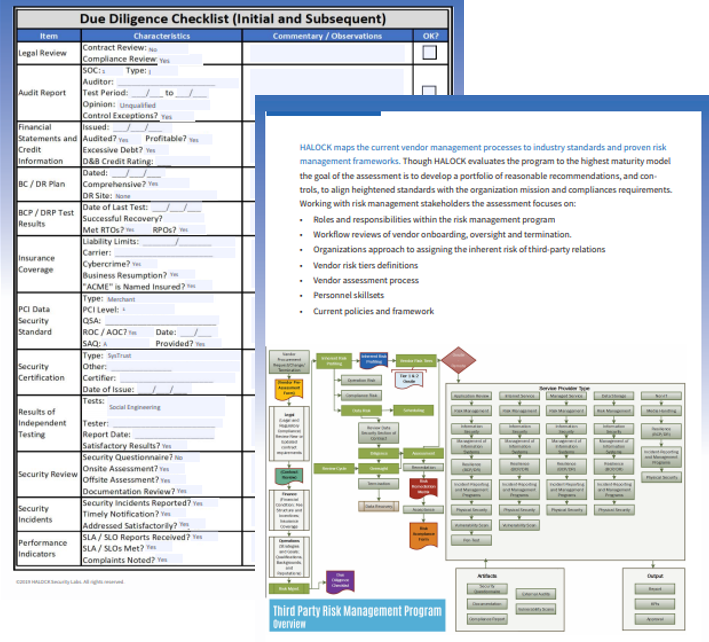
Too many companies fail to properly vet their vendors during the selection process from a cyber security perspective. An invited vendor brings with it invited risk. It is your job to determine the level of risk that your vendors introduce to your organization by conducting a risk assessment. This process involves assessing the likelihood and impact of safeguards being compromised as well as asking important questions such as the following:
- What is the security reputation of your vendors?
- Do they have a disaster recovery plan?
- Do they an active robust cyber security program?
- Does their security plan include policies and procedures that are regularly updated?
- What types of security and compliance resources do they have?
A vendor relationship constitutes some type of service level agreement (SLA) that outlines business requirements and deliverables. The inclusion of security should also be in SLAs or other types of contractual agreements. These agreements can be based on adherence to accepted standards such as the CIS Controls. You may also want to request your vendors to release copies of security audits they have undergone.
Managing Your Vendors
One of the reasons that so many companies continue to be at risk from third-party breaches and attacks is they lack the time and resources to properly conduct a comprehensive vendor risk assessment. These types of assessments can be lengthy and require a level of expertise that many organizations don’t have inhouse.
That’s why many companies turn to a partner with the security expertise to fully evaluate the cyber security risk and readiness of their vendors. The addition of a new vendor doesn’t have to mean the acceptance of added risks.
Assess your vendors with a Vendor Risk Checklist.
You can also start mapping out the TPRM process by requesting the Third-Party Risk Management (TPRM) Interactive Workbook.
To quickly get started on reviewing your third-party partners and vendors, contact us to scope your project.