After your organization has a data breach, what would you say to a judge that asked if your safeguards were ‘reasonable?’ In one of the highest-registered Compliance Week webinars, The Questions a Judge Will Ask You After a Data Breach, HALOCK Security Labs partner and DoCRA Chair Chris Cronin conducted an insightful session to provide insight into that very question. Over 540 compliance officers, general counsel, and security auditors attended the webinar seeking a peek into “judgment day” to see how well prepared they were.
It turns out that guilt by association does not necessarily apply in the case of a data breach. A breach by itself does not constitute negligence. Being the victim of a security incident doesn’t automatically imply that you or your staff did anything wrong. Breaches do often require some sort of legal investigation however; one in which a judge will ask hard questions of you. In that event, it will be perfectly understandable to be a little nervous. Litigation can be scary. It’s good to know however that the judge is not in pursuit of your guilt, but in understanding your “duty of care.” It’s the judge’s responsibility to determine whether the safeguards you used prior to the breach were reasonable for protecting the business from a potential breach. To gain an understanding concerning the preparedness to defend themselves in litigation matters, HALOCK asked the following survey question of those in attendance.
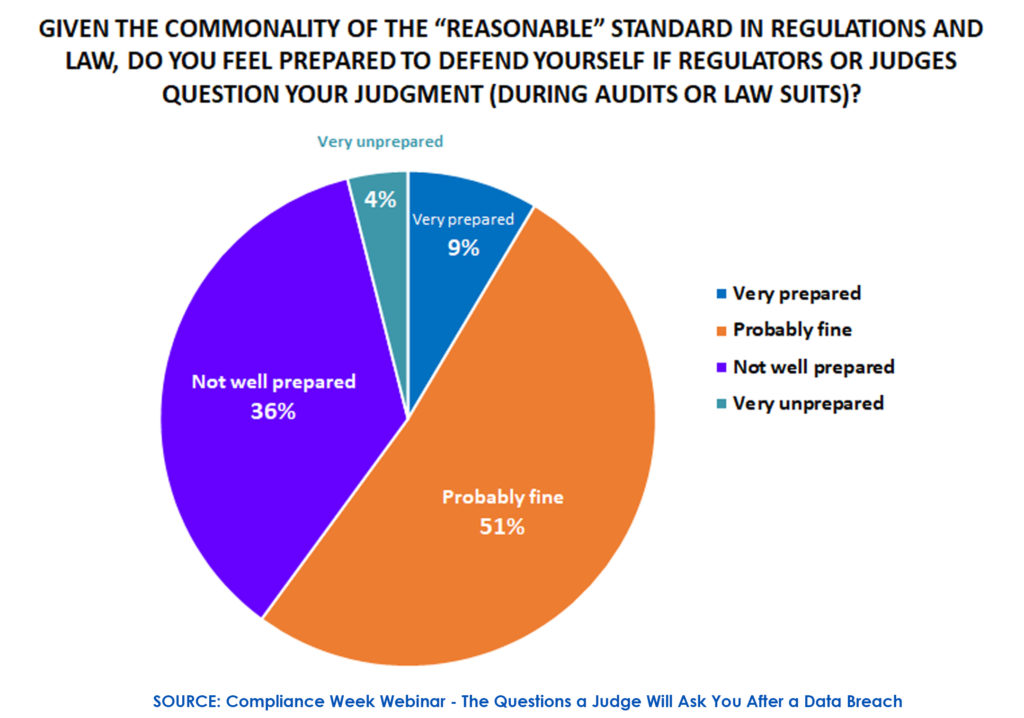
Given the commonality of the “reasonable” standard in regulations and law, do you feel prepared to defend yourself if regulators or judges question your judgment (during audits or law suits)?
Out of the 433+ respondents, about 40 percent of the respondents indicated they were not prepared for a regulatory audit or lawsuit, with only 9 percent citing themselves as very prepared.
With constantly evolving legislation – most recently the California Consumer Privacy Act and Ohio Data Protection Act — organizations have a hard time keeping up with the constant changes in security expectations … unless, of course, they understand why these regulations constantly refer to “reasonable” controls and risk. Once organizations know how to define these terms, they will be confident on judgment day, even if they are imperfect.
“Reasonable” is Not Hard to Define
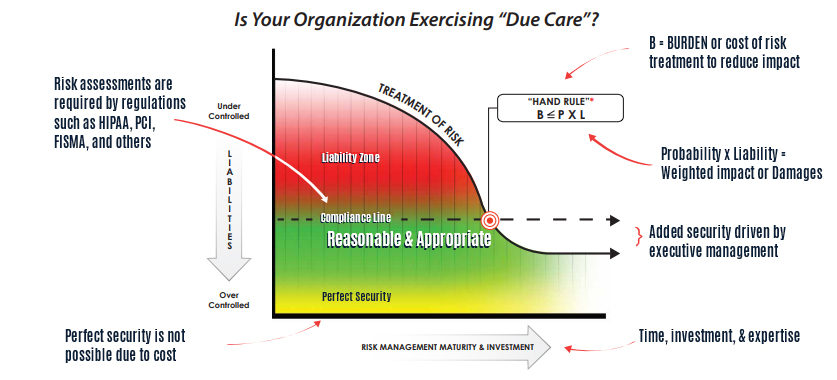
One of the ideas conveyed during the webinar was somewhat surprising to many in attendance. The term, “Reasonable” is a big gift to business, if you know how to use it. When it comes to a data breach, the term reasonable equates to balance. Since 1993, regulations concerning the protection of personal data and information must be supported by a cost-benefit analysis. This desired balance states that the burden of safeguards must not be greater than the harm to the public. If we were to present this in equation form, it would look like this:
Burden of safeguards < harm to others x likelihood of harm
Simply put, you should use safeguards to protect others from harm. But those safeguards should not create more of a burden on you than the risks of harm to others. The way you find that balance is through a risk assessment. If done right, you will identify your associated risks as well as the reasonable controls to protect against them. Determining this proper balance involves the evaluation of the following:
- Your Mission: What makes the risk worthwhile for people you may harm?
- Your Objectives: What are your organization’s indicators of success?
- Your Obligations: What care do you owe others?
A Duty of Care Risk Analysis (DoCRA) is a valuable process to help define your duty of care. DoCRA is a qualitative method that can plug into other quantitative and qualitative frameworks. It helps arm you with the facts and knowledge to find reasonable controls concerning the security of your enterprise. In the event of litigation or regulatory oversight, DoCRA will provide documentation and insight provided by subject matter experts that will aid a judge or regulator to understand how you identified the balance between your burden and the foreseeable the harm to others. In other words, proper knowledge results in the implementation of proper controls.
DoCRA for Regulators
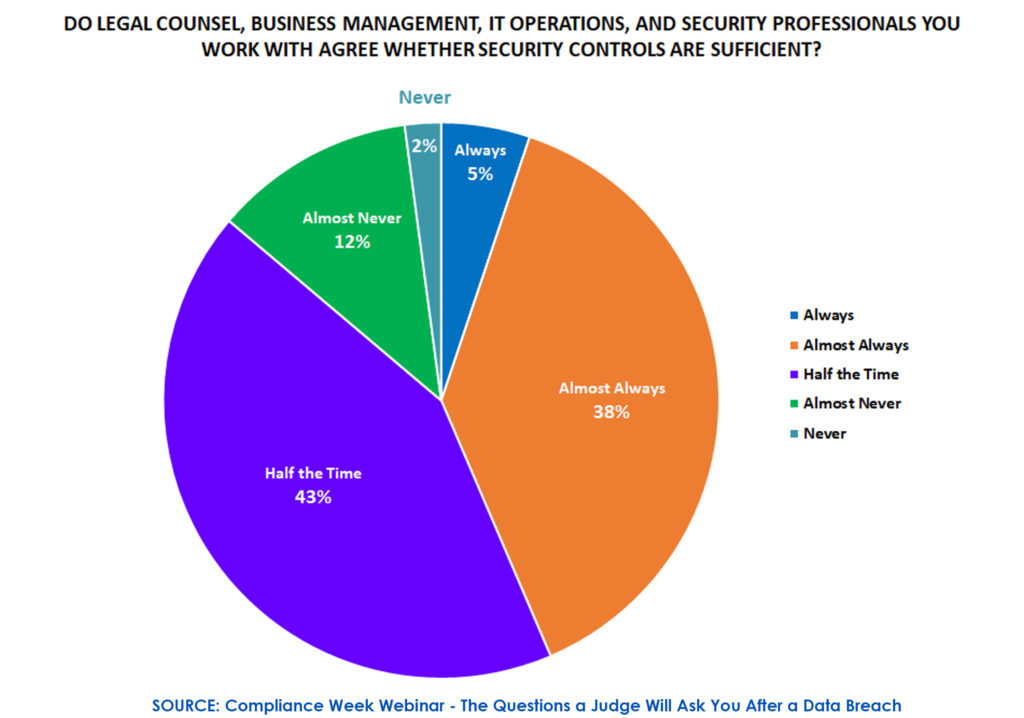
So are your cyber security controls sufficient? HALOCK asked another survey question to see whether attendees’ legal counsel, business management, IT operations and security professionals agree whether cyber security controls are sufficient. Out of the 427 respondents:
- 43 percent indicated half the time with 14 percent admitting to almost never
- Only 5 percent said always
Implementing DoCRA
The definition of what is reasonable for your business shouldn’t be an open-ended question. Partnering with qualified advisors can help establish duty of care. You don’t have to be uncertain as to what your risks are, or the controls you should reasonably implement to guard against them. If you are looking to implement DoCRA:
Organizations can reference CIS RAM, CIS® Risk Assessment Method, based upon DoCRA. It is free to download at cisecurity.org. It provides guidance on how to implement the CIS Controls reasonably.
DoCRA for Executives
Law firms can schedule a complementary 1-hour introductory session (CLE credit available) with HALOCK, followed by a complementary partial day DoCRA Training to enable attorneys to counsel their clients on duty of care risk analysis. For those unable to attend the Compliance Week webinar, the presentation material is available for download.
Learn more about DoCRA here or at future events to help answer the question.
What is your definition of reasonable security?