In the past decade we have seen companies defined by how their leadership responded to a cyber security incident. The most prominent incident is a data breach, which is becoming a too common occurrence, involving billions of people. The data of 765 million people were compromised in a 3-month period in 2018 alone, a 47 percent increase over the year before. If your company deals with the personal data of other people, then you are a target of highly organized criminal organizations that recruit some of the top cyber talent in the world. This is the new reality, and preparing for it is a cost of doing business today. What is your incident management strategy?
The Numbers and Costs tell a Disturbing Story
According to Juniper Research, the U.S. will account for half of all breached data by 2023. It is estimated that cyber criminals will steal an estimated 33 billion records that year, nearly triple the 12 billion expected in 2018. Not only is the U.S. the most targeted country in the world, but U.S. companies incur some of the highest incident response costs in the world. The average total cost of a data breach increased by 6.4 percent according to the Ponemon 2018 Cost of a Data Breach Study. Notification costs in the U.S. averaged to $740,000*, the highest in the world. Notification costs include the creation of contact databases, the determination of all regulatory requirements, hiring of outside experts, postal expenditures, etc. Companies that work with third party vendors such as SaaS and cloud service providers should know that third party involvement and cloud migrations increase the costs as well. According to the study, a breach caused by a third party incurs an increased cost of $13 per compromised record for an adjusted average cost of $161, compared to $148. Organizations undergoing a substantial cloud migration at the time of a breach incurred a $12 increase in cost per capita.
Speed is of the Essence
The world just runs faster today. Thanks to 24-hour broadcasting and social media, news travels fast, especially bad news. It’s another reality to deal with. Speed is of the essence to contain costs. A major cybersecurity incident is comprised of three types of costs:
- Direct costs – the cash expenses of dealing with a response
- Indirect costs – this includes all of the time and effort expelled by your personnel and other internal resources
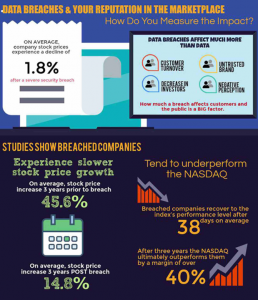
- Opportunity costs – while often neglected, there is the cost of lost business opportunity as the time and expense involved in your response could have been directed at making money for your company. Opportunities are also lost thanks to a tarnished reputation and corporate image as a result of the breach.
It is the culmination of these indirect and opportunity costs that speed becomes so important. According to the Ponemon Report, the mean time to identify a breach last year was 197 days. The corresponding time to contain it was 69 days. These elongated periods are also supported by Verizon’s 2018 Data Breach Investigations Report (DBIR) which shows that 66 percent of breaches take months or ever years to detect. In fact, 1 in 10 take more than one year. One of the most illuminating findings of the Ponemon Report is the direct relationship between how quickly an organization can identify and contain a data breach incident and the financial consequences of it. Companies that identified a breach in less than 100 days saved more than $1 million as compared to those that took more than 100 days. Subsequently, companies that were able to contain a breach in less than 30 days saved $1 million as well, compared to those that took more than 30 days.
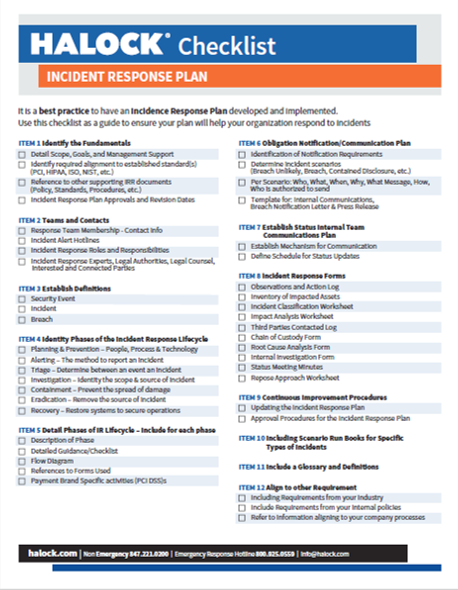
The ability to respond quickly to an incident requires preparedness. Those companies that had an effective incident response plan in place reduced the cost of a breach by at least $14 per compromised record. It should also be noted that the use of encryption reduced the per capita cost by $13 as well.
A Slow Response has Horrible Consequences
Perhaps no data breach has been scrutinized more concerning its lack of response than the Equifax data breach, who experienced the largest data breach ever back in 2017. The running total costs of the breach stand at $1.3 billion today. These costs include transformational costs concerning its IT and security infrastructure, legal fees, investigative services, government and regulatory costs and more. The company’s 2019 first quarter balance sheet listed $82.8 million in technology and security costs arising from the breach as well as $12.5 million in quarterly legal and investigative fees. Says one Equifax executive, “The ultimate amount paid on these actions, claims and investigations in excess of the amount already accrued could be material to the company’s consolidated financial condition, results of operations, or cash flows in future periods.”
Other examples of “what not to do” includes Panera Bread, whose website had been leaking millions of customer records for at least 8 months before the company took any initiative to eradicate it. Exposed information included customer names, email and mailing addresses, birthdays and partial credit card numbers. The exposure was uncovered by a third party cyber security consultant who contacted Panera, but the information was ignored. It wasn’t until the discovery was made public 8 months later that anything was done about it.
NBC News recently interviewed the Chief Information Security Officer (CISO) of a large U.S. bank about its recent breach. The interview was given under the agreement of anonymity. The CISO explained that the breach that took 185 days to discover it and exposed the information of 40,000 customers. The breach then took 59 days to contain it and costs are expected to exceed $7 million. The attack was implemented by a phishing email that spoofed the address of a trusted sender. The executive went on further to describe the negative impact concerning the diminished trust of its customers, business partners, and regulators.
As in anything in life, failing to plan translates into planning to fail. In fact, there are endless analogies we can use such as “an ounce of prevention is worth a pound of cure.” The costs of increasing the ability to identify malicious activities and formulating and implementing an incident response plan (IRP) are negligible when compared to the expenditure of dealing with the aftermath. Your goal is to find the issues and fix them fast. HALOCK Security Labs reduces the mean time to identify malicious activities through Security Threat Management and reduce the time to contain a cyber attack with a strategic incident response plan. HALOCK can help prepare your company for a data breach situation and provide the threat visibility and preplanned strategies to best manage the situation when seconds count. Time is money, and this combined approach can not only secure your enterprise but serve as a competitive advantage. We can partner with you to identify your priorities and specific preparedness needs to further protect and monitor your environment and keep your business running as normal as possible, in this vulnerable world that is the new normal.
Incident Management Response Resources
*These costs include the creation of contact databases, determination of all regulatory requirements, engagement of outside experts, postal expenditures, email bounce-backs and inbound communication setups.
Enhance your security strategy to address your changing working environment and risk profile.
HALOCK is a trusted cyber security consulting firm and penetration testing company headquartered in Schaumburg, IL in the Chicago area servicing clients throughout the United States on reasonable security strategies.
Are you prepared for a cyber security incident? Assess your incident response readiness. We can help if you have a security incident to help minimize the impact.
Incident Response Hotline: 800-925-0559