Remote Social Engineering Penetration Testing

Putting Security Awareness Training to the Test
That users are the weak link when it comes to cybersecurity is a generally accepted truth. Very few technical controls can compensate for the intricacies of human behavior such as a person’s natural tendency to trust another person. Remote social engineering exploits the “scripts” of human interaction — how people typically interact and what they expect to happen in a given situation — rather than exclusively leveraging technical security vulnerabilities to test the effectiveness of security awareness training, stated security policies, and processes such as incident response.

What is a Remote Social Engineering Penetration Test? How does HALOCK’s Security Awareness Evaluation work?
Remote social engineering penetration testing validates the effectiveness of user security awareness training, and spam and malware filters. HALOCK offers a Security Awareness Evaluation Penetration Test, conducted under controlled conditions. The testing presents a phishing email (the most common attack vector) containing red flags that users who have completed security awareness training could identify. The messages are designed to bait users into clicking simulated malicious links (social engineering techniques) to determine if training was effective.
Why should we conduct a Remote Social Engineering Penetration Test?
Targeting employees is a rapidly increasing threat that attackers use to gain access. Organizations routinely provided trusted employees with access to sensitive data. If an attacker can compromise the user, they instantly have rights to whatever that employee could access. Performing controlled spear phishing attack exercises tests employee security awareness and frontline controls such as spam and malware filters. Most security standards and regulations require security awareness training. HALOCK’s Security Awareness Evaluation, a robust remote social engineering assessment, is the most effective method of confirming it works.
Why should HALOCK perform our Remote Social Engineering Penetration Test?
HALOCK has the experience to best assess how well an organization’s security awareness policies and procedures are performed. For over two decades, HALOCK has conducted thousands of successful remote social engineering pen tests for companies of all sizes, across all industries.
HALOCK’s dedicated penetration test team is highly qualified, possesses advanced certifications, and is equipped with the labs, tools, and methodologies necessary to consistently deliver quality, accurate, detailed, and meaningful results.

How do I choose which employees to test?
You don’t. The attacker does. When preparing for a remote social engineering penetration test, there may be circumstances where certain employees cannot be included, however all remaining employees should be considered potential targets. An attacker is best equipped with a broad and diverse list of targets spanning multiple business units, job functions, or roles. This allows the attacker to probe and identify where opportunity presents. Information gathered is repurposed and leveraged for subsequent contact attempts. An attacker will generally not target all employees as doing so increases the likelihood of detection. To simulate these conditions, our remote social engineering penetration testing experts will select targets from the list.
A Comprehensive Methodology for Social Engineering Assessment
- Information Gathering Initial reconnaissance activities to gather the necessary information to prepare suitable and credible messaging, such as the services the target organization offers, relationships between varying business units or divisions, information exposed on public sources, and other employee or corporate specific information
- Infrastructure Preparation Systems to transport email, track responses and activity, and host content are deployed and configured.
- Campaign Preparation Target lists are grouped and sequenced, campaign batches are configured and scheduled, and related preparation tasks are completed.
- Campaign Launch Initial test messages are issued to gauge response behavior, identify technical controls that might warrant revising the planned approach, and fine-tuning attack methods.
- Initial Exploits As sessions are established, initial exploits are pursued to establish baseline access through payloads, command and control, scripted actions, identify secondary targets on the compromised network, and establish persistence.
- Secondary Exploits attempts to increase a presence throughout the connected environment by bypassing user access controls, identifying internal weaknesses to exploit, leveraging excessive user rights, and compromising connected systems.
- Exfiltration Attempts to identify local data repositories that would be of value to an attacker stored on locations such as local repositories, mapped drives, databases, and file sync folders.
- Disengaging Winding down activities including terminating sessions, gathering evidence necessary for reporting, and preventing continued contact following the conclusion of the campaign.

Deliverables
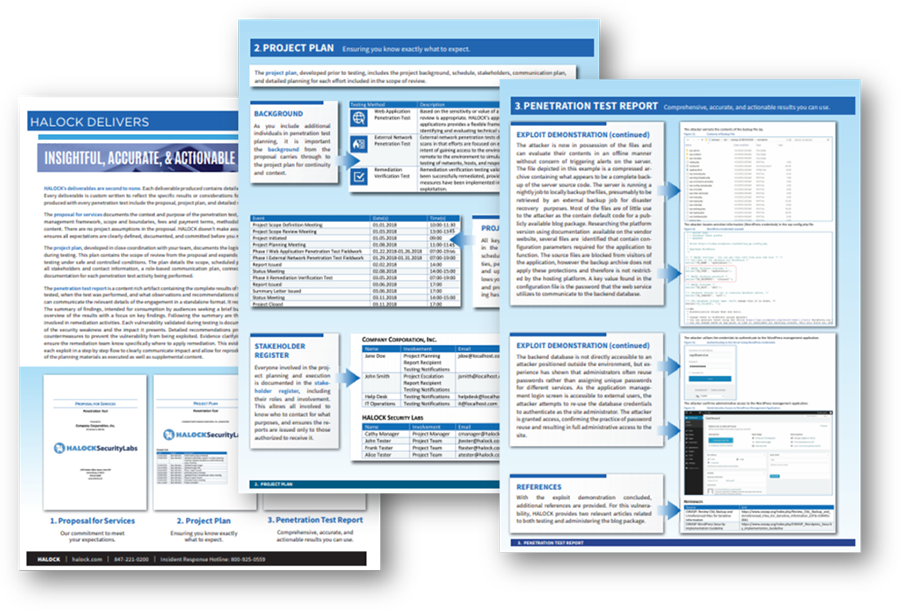
- Project Plan: Prior to remote social engineering penetration testing, HALOCK will develop a project plan detailing the specific plan, timing, and related considerations. This ensures all parties know what to expect throughout the execution of testing and reporting.
- Penetration Test Report: The complete results of the remote social engineering pen test are documented in our content rich report which includes the background, summary of findings, detailed findings, scope and methodology, and supplemental content for context and reference.
- Background: An introduction of the general purpose, scope, methodology, and timing of the remote social engineering penetration test.
- Summary of Findings: A concise overview summarizing the social engineering assessment results at a glance, such as key critical findings requiring priority attention, system or recurring issues, and other general results.
- Detailed Findings: Comprehensive results of each vulnerability, including a description of the vulnerability observed, the impact, recommendations for remediation, evidence where the vulnerability was observed, step-by-step demonstrations of exploits performed, and additional reference materials.
- Scope and Methodology: A detailed recap of the specific scope of what was tested, the methodologies utilized, and related historical information necessary for audiences such as auditors to understand the specifics of the test approach.
- Supplemental Content: Additional content and guidance, such as recommended post social engineering assessment activities.
Consider a Recurring Penetration Testing program to assess your safeguards throughout the year for a proactive security approach.

HALOCK, a trusted penetration testing company headquartered in Schaumburg, IL, near Chicago, advises clients on reasonable security strategies, risk management, and compliance throughout the US.
