Breached? So, What’s the Plan?
If you are breached, having a plan in place to quickly detect, remediate, and secure your network can make a difference between being a hero or the negligent party. Know your options.
INCIDENT RESPONSE PLANNING: A roadmap to follow during a security event.
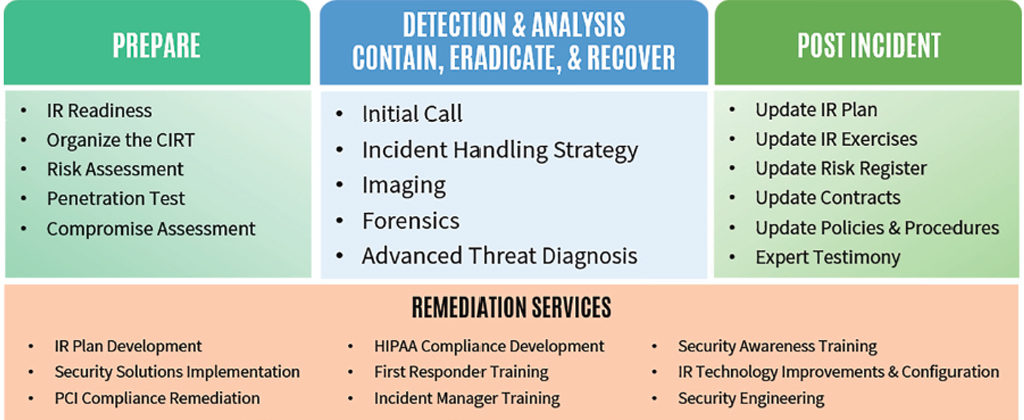
UNDERSTAND YOUR SECURITY POSTURE: Regularly refine your strategy.
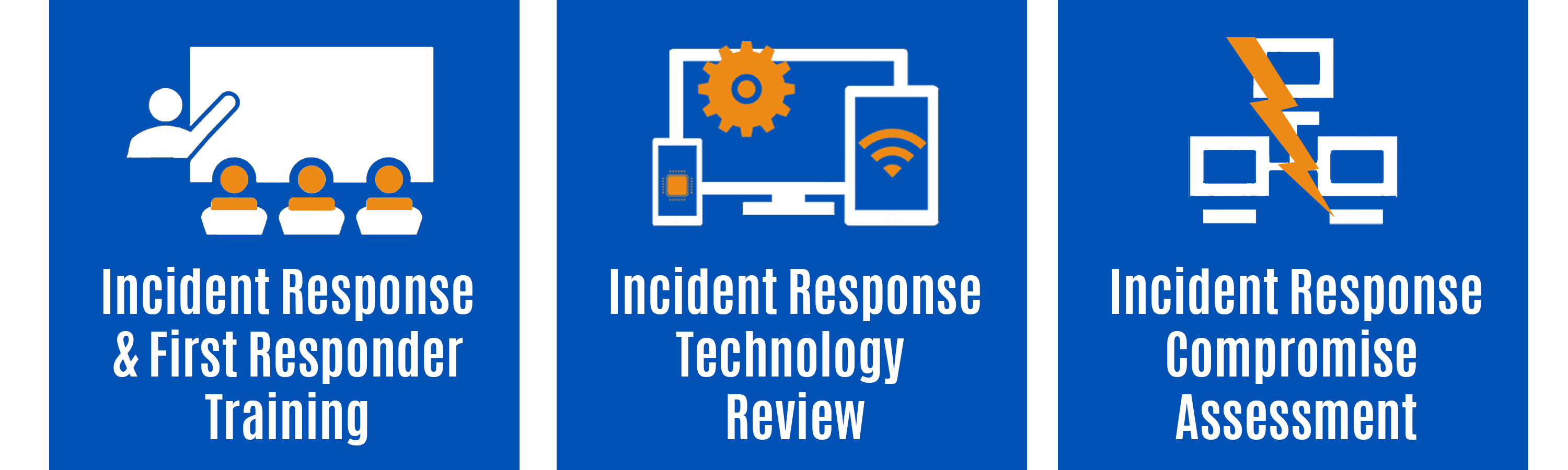
Prepare the Team: Know protocols, member roles, and how to preserve evidence for investigations.
Evaluate Your Current Readiness: Review your posture against industry requirements, with lists of gaps and recommendations.
Manage & Monitor Active Threats: Hunting and assessing threats within the organization.
FORENSIC SERVICES: Analyzing your systems post-breach to determine what happened, how it happened and impact to your information. HALOCK Helps contain the incident, eradicate any infections, and recover while recording the chain of events that led to the breach.
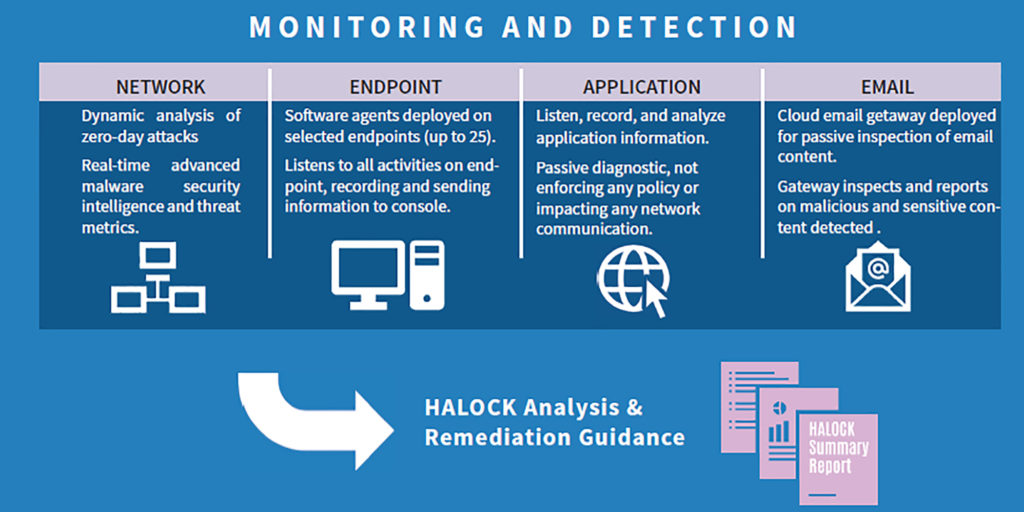
SECURITY THREAT MANAGEMENT: Continually monitor your organization — with HALOCK providing alerts, blocking improper access and delivering real-time cyber threat analysis. Partner with us to reduce the time to identify and contain a breach, offering you peace of mind by reducing your risk.

ARE YOU READY? SCHEDULE A SCOPING CALL TODAY.
