Web Application Penetration Testing
Are Your Critical Web Applications Protected?
Conducting business on the Internet has become an essential requirement for almost every organization. However, those web applications are exposed to near-constant bombardment from entities looking to exploit vulnerabilities for malicious purposes. Frequent, in-depth security reviews combined with web application pen testing are necessary to ensure that your critical assets are protected.

What is Web Application Penetration Testing?
For sensitive or high value web applications, a comprehensive review is appropriate. HALOCK’s web app penetration testing fully identifies and evaluates web application vulnerabilities. Testing is performed with knowledge of the functionality available to users and their access levels to ensure a detailed review of the application.
application penetration testingWhy should we conduct a Web Application Security Testing?
Custom web applications are designed to provide access to services and information. Validating if that access is used as intended requires very specific and specialized web application security testing methodology. Because every custom application is unique, web application pen testing is conducted to identify vulnerabilities in the underlying code that an attacker can leverage to gain unauthorized access. Verify that your AppSec cycle addressed all risks. Most regulations governing organization security obligations specifically call out web applications as requiring this form of testing, above and beyond other internet facing assets. PCI DSS requires web application security testing for those that have not used web app firewalls. Performing web application penetration testing is a critical step in ensuring the code is secure, the organization is compliant, and customers can trust their data is protected.
73% of successful breaches in the corporate industry were done by penetrating web applications through their vulnerabilities.
“Very rapid turn-around. Appreciate the review.”
Why should HALOCK perform our Web Application Pen Test?
HALOCK has the experience to best assess the security controls effectiveness for web applications. For over two decades, HALOCK has conducted thousands of successful web application penetration testing programs for companies of all sizes, across all industries.
HALOCK’s dedicated application penetration testing team is highly qualified, possesses advanced certifications, and is equipped with the labs, tools, and methodologies necessary to consistently deliver quality, accurate, detailed, and meaningful results.
HALOCK leverages industry standard methodologies to ensure thorough and comprehensive web app penetration testing is conducted under safe and controlled conditions. HALOCK’s reports are content rich, regularly stand the scrutiny of regulatory requirements, exceed expectations of auditors, and frequently receive the praise of our customers. HALOCK does not simply validate automated scans. HALOCK’s expert team discovers vulnerabilities not yet published and often not yet discovered. Exploits are pursued, documented step by step, with screen capture walkthroughs, to provide both the technical and visual clarity necessary to ensure corrective actions can be prioritized and remediation is effective.
“extremely helpful making sure all pen tests were completed in a small time frame.”
– Financial Services Consulting Company
Which web applications should we have tested?
Commercially provided web applications, especially those with minimal customization, are generally well documented through public sources for known vulnerabilities as well as the patches required to remediate those issues. Commercial applications that lack this history of testing should be considered for comprehensive web application testing as unknown (zero day) vulnerabilities may exist, but this is not common. Custom developed web applications, however, are most commonly selected for comprehensive web application security testing. As each customer web application is unique, these public sources do not exist. Custom web applications, in particular those protecting sensitive information, should be considered for comprehensive web application penetration testing. Regulatory requirements also often dictate certain applications be tested at least annually.


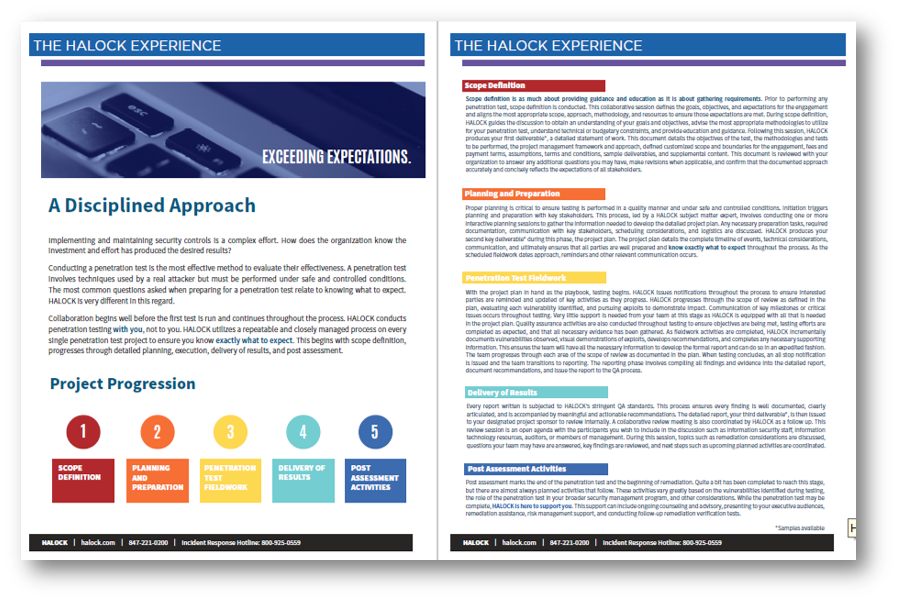
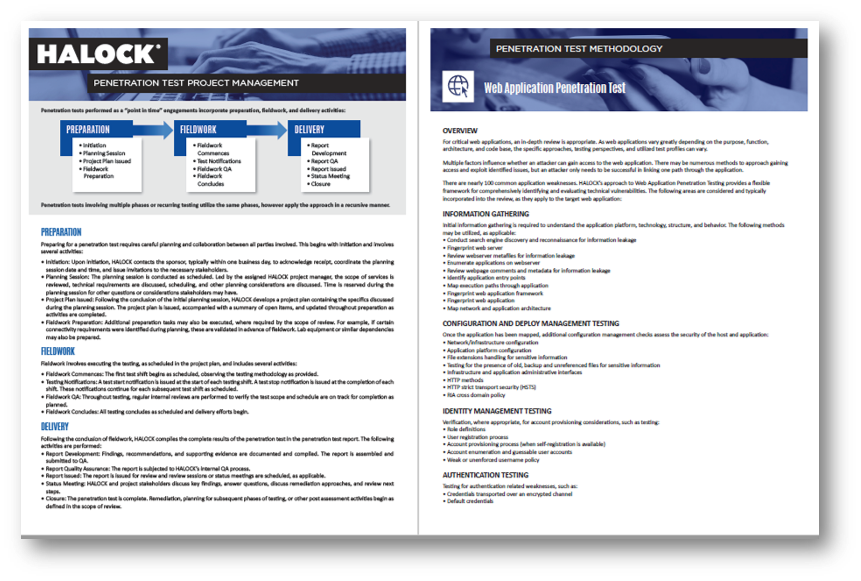
Web Application Security Testing Methodology
- INFORMATION GATHERING: Conducting reconnaissance activities to locate information leakage, identify the technologies utilized, map application entry and functionality, and related tasks to guide testing.
- CONFIGURATION AND DEPLOY MANAGEMENT TESTING: Testing the configuration of underlying platform and infrastructure and identifying potential change control weaknesses such as the presence of orphaned code or code backup files.
- IDENTITY MANAGEMENT TESTING: Verification, where appropriate, for account provisioning considerations such as user registration processes or account enumeration.
- AUTHENTICATION TESTING: Testing for authentication related weaknesses, such as insecure authentication, default credentials, or password weaknesses.
- AUTHORIZATION TESTING: Testing to validate the security of authorization controls such as privilege escalation or bypassing authorization.
- SESSION MANAGEMENT TESTING: An evaluation of session-related vulnerabilities such as session fixation, exposed session variables, and cross-site request forgery.
- DATA VALIDATION TESTING: Data validation testing including cross-site scripting, parameter tampering, SQL injection, and command injection.
- TESTING FOR ERROR HANDLING: Testing error handling issues, as they relate to security, such as analysis of Error Codes and Stack Traces.
- TESTING FOR WEAK CRYPTOGRAPHY: Testing to evaluate the effectiveness of encryption related protections such as weak SSL ciphers.
- BUSINESS LOGIC TESTING: Testing to determine if the flow or architecture of the application can be manipulated to gain access to sensitive information through flaws in business logic or application workflows.
- CLIENT-SIDE TESTING: Assessing vulnerabilities that commonalty affect the client side of the application session such as JavaScript execution, CSS injection, cross-site flashing, and clickjacking.
Deliverables
Project Plan: Prior to testing, HALOCK will develop a project plan detailing the specific plan, timing, and related considerations. This ensure all parties know what to expect throughout the execution of web application penetration testing and reporting.
Web Application Penetration Testing Report: The complete penetration testing results are documented in our content rich report which includes the background, summary of findings, detailed findings, scope and methodology, and supplemental content for context and reference.
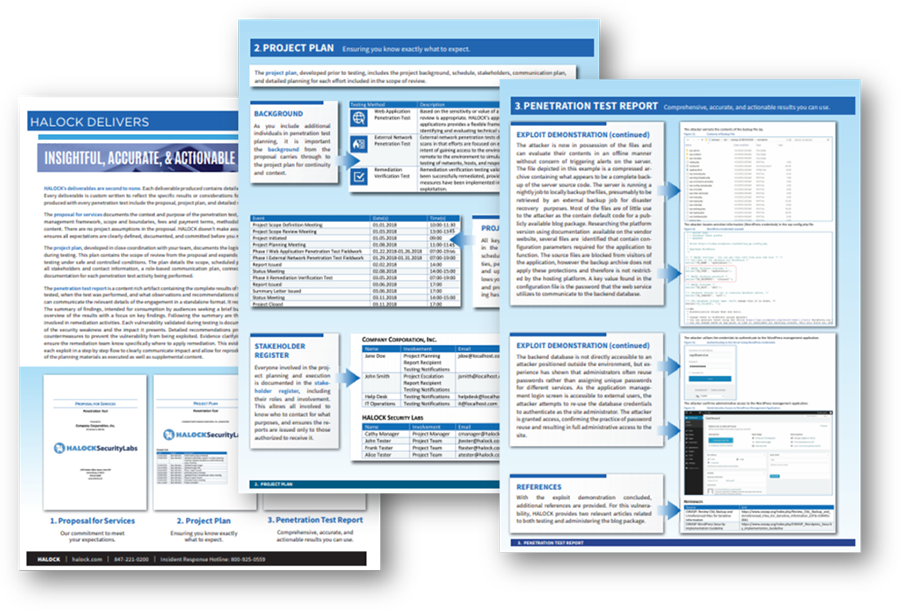
- Background: An introduction of the general purpose, scope, methodology, and timing of all web app penetration testing.
- Summary of Findings: A concise overview summarizing the results at a glance, such as key critical findings requiring priority attention, system or recurring issues, and other general results.
- Detailed Findings: Comprehensive results of each vulnerability, including a description of the vulnerability observed, the impact, recommendations for remediation, evidence where the vulnerability was observed, step-by-step demonstrations of exploits performed, and additional reference materials.
- Scope and Methodology: A detailed recap of the specific scope of what was tested, the methodologies utilized, and related historical information necessary for audiences such as auditors to understand the specifics of the test approach.
- Supplemental Content: Additional content and guidance, such as recommended post assessment activities (Samples available upon request).
Consider a Recurring Penetration Testing program to assess your safeguards throughout the year for a proactive security approach.
”Thank you for all your help.”
-Professional Association
KEEPING YOU INFORMED – HALOCK SECURITY BRIEFING FOR CLIENTS
The HALOCK Security Briefing is a review of significant events, trends, and movements that will influence how you manage cybersecurity, risk, and compliance. Our clients receive periodic overviews with an extensive report file on the topics discussed. This insightful document also includes reference links throughout the report for easy navigation and deeper research.
HALOCK, a trusted web application penetration testing company headquartered in Schaumburg, IL, near Chicago, advises clients on reasonable information security strategies, risk assessments, third-party risk management (TPRM), penetration testing, security management, architecture reviews, and HIPAA,Privacy, & PCI compliance throughout the US.