Category Archives: Reasonable Security | Reasonable Risk

Cloud Security Assessment
Cloud Covered
HALOCK’s Cloud Security Assessment gives you insight on your risks. The assessment provides a review of Azure, AWS, and Google (GCP) cloud environments to identify risk and recommends how to remediate them. HALOCK combines manual analysis of these cloud platforms using the applicable CIS benchmarks combined with the Tenable Cloud Security solution. Clients receive a comprehensive look at cloud environments, allowing them to better enhance their security. HALOCK will provide analysis for the following security areas:
Identification of:
- Assets related to all user, computer, network, data, management and security resources.
- Potential toxic combinations of access privileges, non-secure configurations, and vulnerabilities.
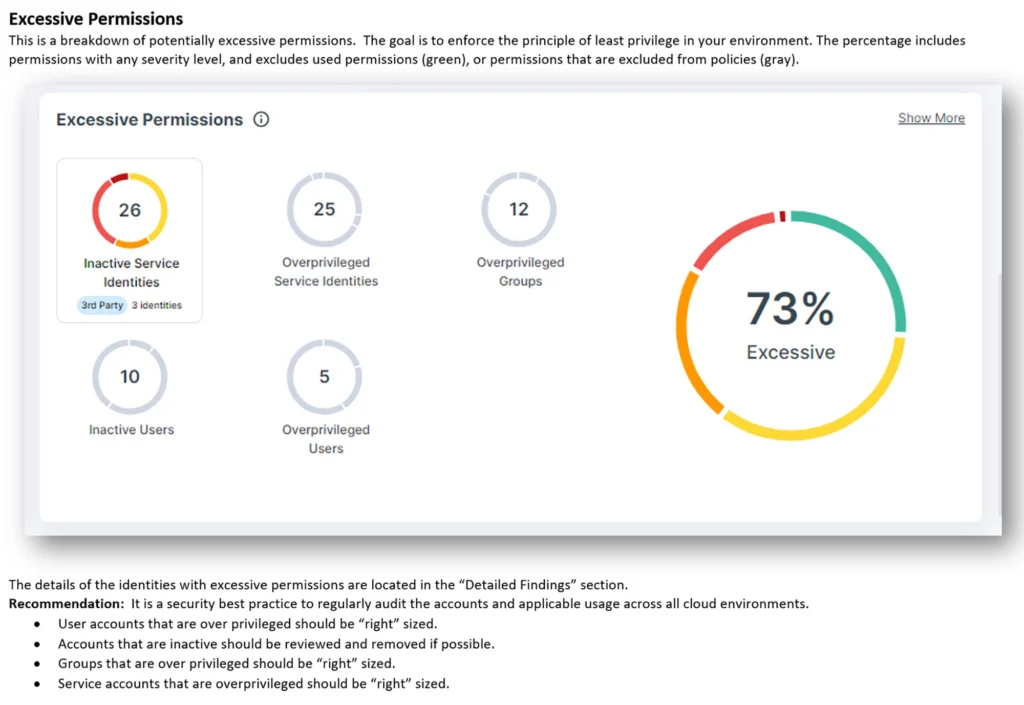
- Accounts that are over-privileged, unused, and may pose higher risk.
- Anomalous events based on the behaviors of account usage and access.
Analysis of:
- Security events
- Logging and monitoring configuration
- Configured policies
- Deployed subscriptions and applicable configurations
- Authentication methods
- Network architecture as deployed
- Configured security center capabilities
The Methodology and Deliverables
- Manual review using the appropriate security benchmarks from CIS for Azure, AWS, and GCP.
- Automated review using Tenable Cloud Security.
- A detailed report with prioritized findings and recommendations to address findings.
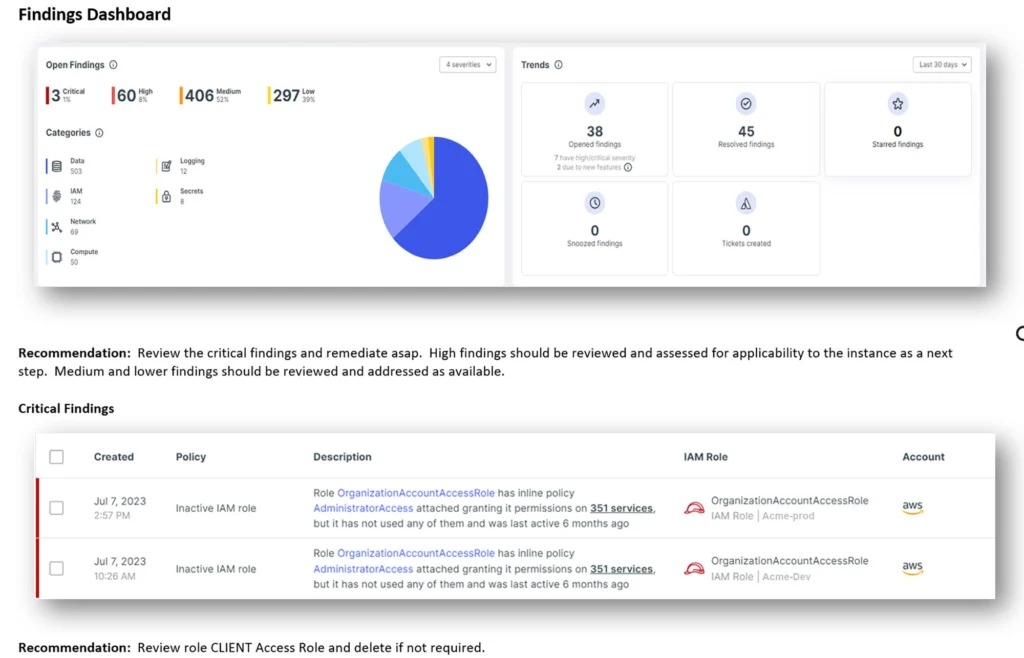
The Cloud Security Assessment identifies
- Critical configuration flaws
- Inventory of cloud assets and identities
- Unused and over-privileged accounts
- Toxic combinations
- Non-secure ports and protocols in use
- Permissions on assets and services that are too permissive
- Exposed secret keys
Why Choose HALOCK?
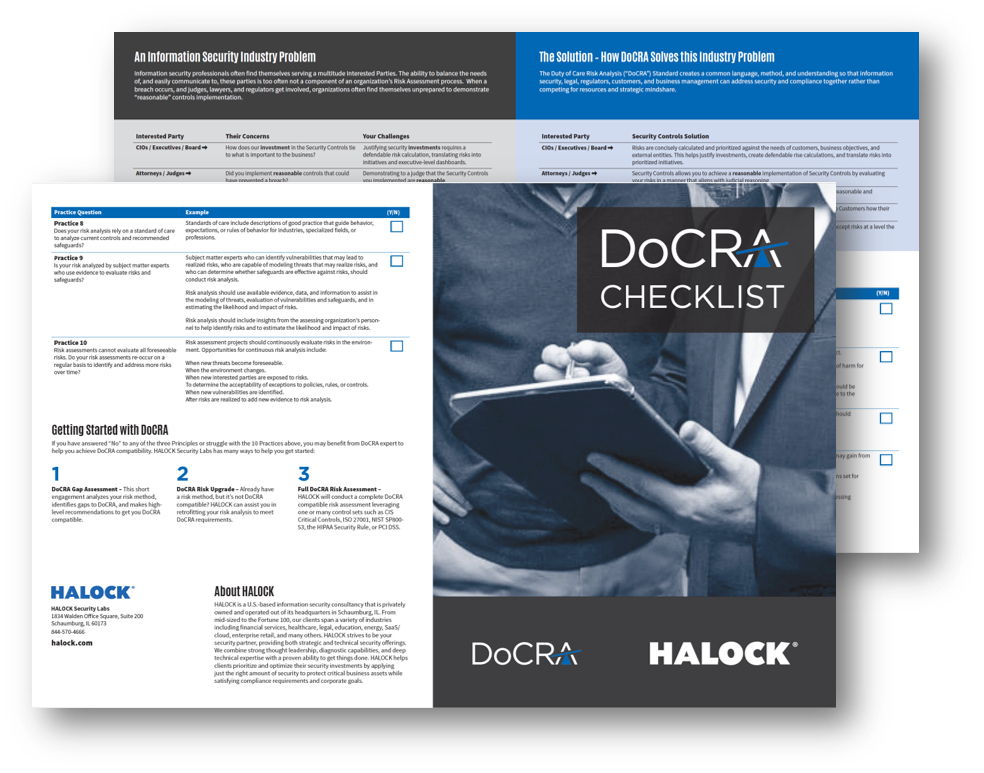
As authors of the DoCRA Standard and developers of CIS RAM, HALOCK has specialized insight to guide you through a risk method to establish reasonable and appropriate security. Risk expertise like no other.
KEEPING YOU INFORMED
The HALOCK Security Briefing is a review of significant events, trends, and movements that will influence how you manage cybersecurity, risk, and compliance. Our clients receive periodic overviews with an extensive report on the topics discussed. There are reference links throughout the report for easy navigation and deeper research.
HALOCK, a trusted risk management and cybersecurity consulting company headquartered in Schaumburg, IL, near Chicago, advises clients on reasonable security throughout the US.
Scope and quote your Cloud Security Assessment.
What’s New in Reasonable Security?
What’s New in Reasonable Security?
Recent developments on ‘reasonable security’ and the cybersecurity industry. Keep current on the evolution of regulatory requirements and how it may affect you.
Reasonable Security: Getting on the same page
As regulations and privacy laws require ‘reasonable security’, we are seeing more organizations focusing on their duty of care to all interested parties. We are finding more references to ‘reasonableness’ in breach litigation and security programs. The goal is to have all relevant teams involved in analyzing the appropriate risk for your unique business environment. It is a positive sign that there are increased efforts to incorporate all perspectives to mitigate risk and manage cyber threats – and finding a common language to do so. And more importantly, developing a security program holistically.